Written by: Karen, Foresight News
On the evening of November 25, the addresses marked as the creators of RIF and URO on pump.fun issued Urolithin B (URO) tokens, leading many community members to mistakenly believe that this was the official token issued by pump.science. Urolithin B (URO) quickly "graduated" and its market value soared to $10 million within two minutes after joining the liquidity pool, but then began to decline continuously, and the current market value has fallen back to about $100,000.
This event also seems to have affected the market performance of Urolithin A (URO) and Rifampicin (RIF), both of which fell by more than 30% within 24 hours. So, what's the story behind this?
Leak of pump.science wallet key pair
The cause of the incident is the leak of the wallet key pair of pump.science.
According to the official announcement of pump.science, due to an oversight in their GitHub repository, the wallet address T5j2UBTvLYPCwDP5MVkSALN7fwuLFDL9jUXJNjjb8sc was attacked, and the attacker found the key pair in the source code of the website. This key pair was originally used for testing purposes in pump.science's GitHub, and the development team was unaware of its importance.
From the fraudulent URO token page that appeared on pump.fun last night, the wallet address that deployed this fake token is T5j2UBTvLYPCwDP5MVkSALN7fwuLFDL9jUXJNjjb8sc. The pump.fun platform shows that this address had previously deployed the official Urolithin A (URO) and Rifampicin (RIF) tokens, with current market values of approximately $87 million and $37 million, respectively.
The fraudulent URO token was issued on-chain by the T5j2UBT-starting address that had the leaked key pair. This is why the new token was displayed on pump.fun as being issued by the deployer of the official URO and RIF tokens.
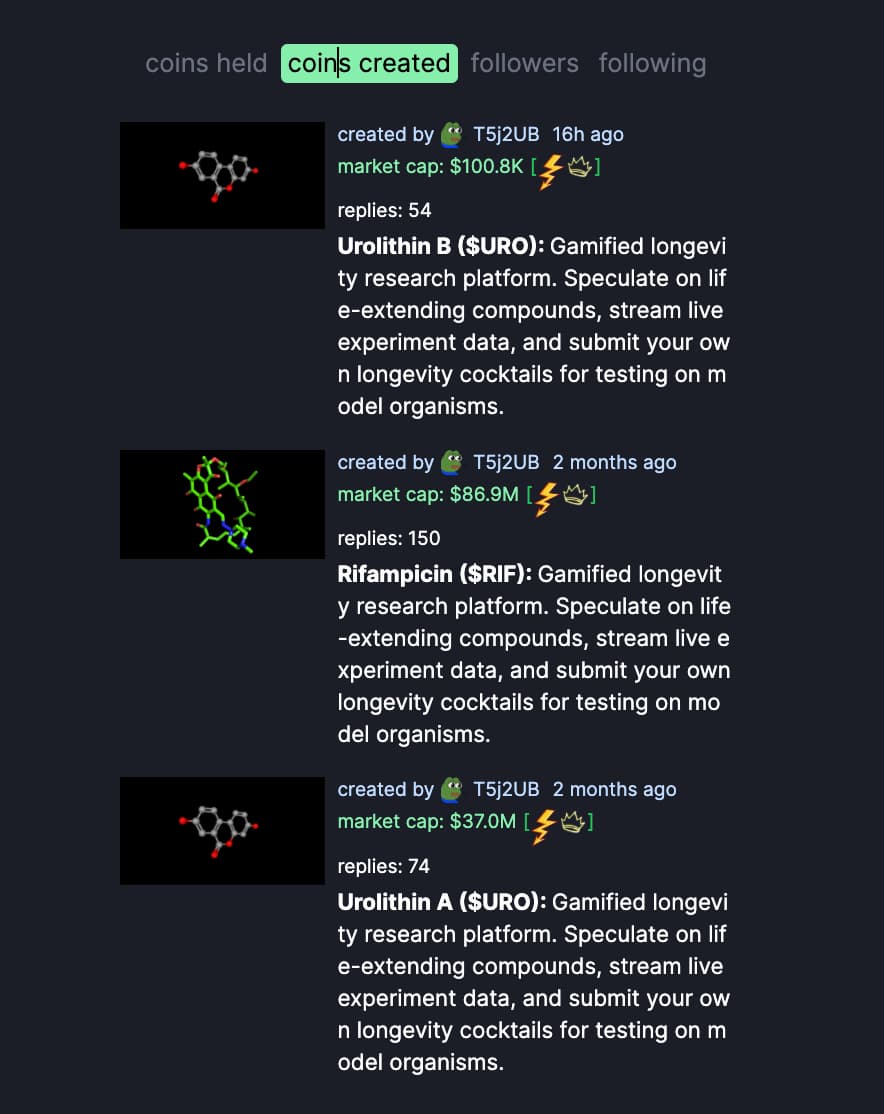
pump.science stated that this wallet was marked on pump.fun as the off-chain token creator of URO and RIF, and the attacker may use this wallet to issue more tokens. Any tokens issued by this wallet other than URO and RIF should be considered fraudulent.
It is worth noting that the pump.science official has not taken any remedial or compensation measures for those users who mistakenly believed and bought the fraudulent URO tokens, which has caused widespread attention and discussion in the community.
The off-chain token creation function of pump.fun leads to confusion in blockchain explorers and data tools
Another source of confusion in the community is the display of token creators on pump.fun and blockchain explorers and data tools.
The official URO and RIF tokens of pump.science were created off-chain on pump.fun, while the fraudulent URO was created on-chain on pump.fun. However, the blockchain explorer solscan shows that the deployment address of Urolithin A (URO) and Rifampicin (RIF) is: BLDRZQiqt4ESPz12L9mt4XTBjeEfjoBopGPDMA36KtuZ.
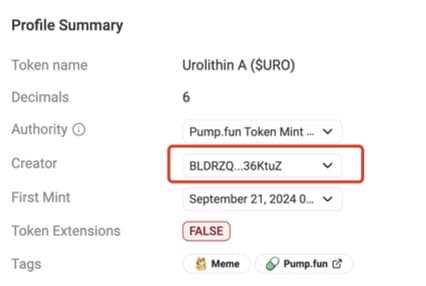
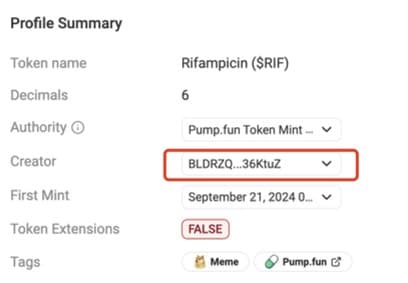
Next, let's understand the off-chain token creation function of pump.fun. On the pump.fun platform, off-chain token creation is free, and the tokens are not immediately recorded on the chain after issuance, until the first buyer appears. The first buyer needs to pay the issuance cost of the tokens. So, for tokens created off-chain, the first buyer's wallet address is often mistakenly recognized as the token deployer by blockchain explorers like solscan or GMGN.
For example, after the official URO and RIF tokens were created off-chain, the wallet address BLDRZQiqt4ESPz12L9mt4XTBjeEfjoBopGPDMA36KtuZ of the first buyer was incorrectly marked as the token deployer by solscan or GMGN.
Here, the author reminds investors to be aware of the distinction between tokens created on-chain and off-chain on pump.fun, and to verify them carefully to avoid falling into fraud traps. In addition, investors should also be vigilant about any potential tokens issued by wallets starting with T5j2UBTvLY, which were leaked by pump.science. At the same time, we also hope that the platform and token deployers can strengthen their security measures to prevent the recurrence of such fraudulent activities.