Preface
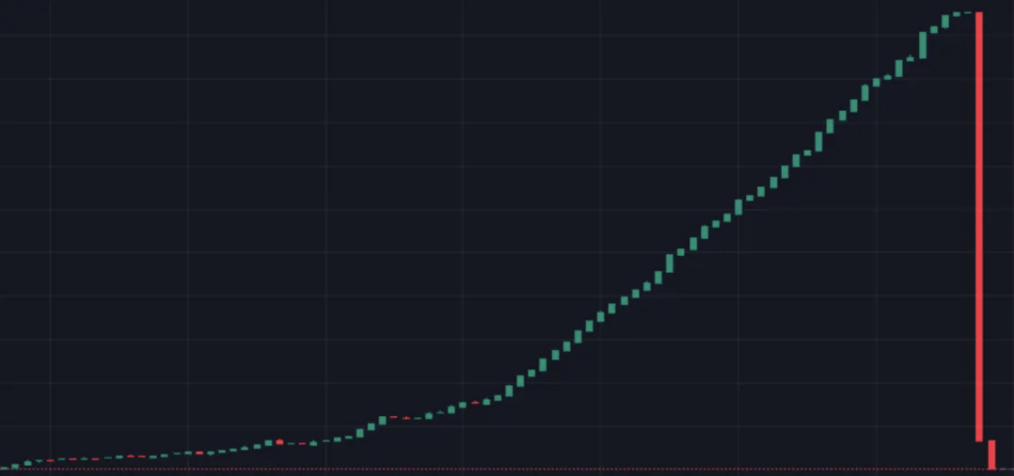
As an old hand in the crypto, everyone knows about the crypto honeypot. A friend you met online says, "I found a great coin with huge potential." After checking the K-line, the trend indeed looks awesome. Unable to resist the temptation or with a casual buying mindset, you buy some. A few hours later, the price has doubled or tripled. When trying to sell, you find yourself forbidden. Now you realize you've bought a crypto honeypot. You watch helplessly as the coin price goes to the Moon, then drops to zero.
The above briefly describes the entire process of a small investor being scammed on the chain. Today, we'll look at it from a development perspective. How are crypto honeypots born? From the case above, everyone should be clear now. A crypto honeypot is essentially a token that only allows incoming transactions. Developers typically achieve this by modifying transfer rules, imposing restrictions on users' selling behavior in the smart contract.
We strongly oppose such behavior!!!
Below, we'll explain how it's implemented in code.
Note: This demo is for case analysis only. Individual developers should run it on the testnet
[The rest of the document follows the same translation approach, maintaining technical terms and preserving the original structure]






