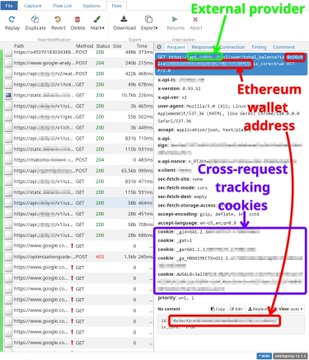
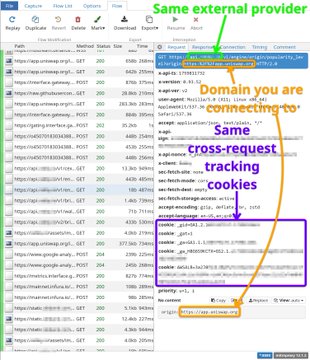
If you want to contribute to identifying which wallets are actually spyware, this is a very good guide for doing so, and is important work to contribute to. It's also great for learning how to intercept network traffic on your devices.

polymutex
@polymutex
10-07
🚢 Walletbeat worklog 2025-10-06
1. Wrote guide on how to use `mitmproxy` to capture and analyze the network requests generated by a wallet, then how to populate the Walletbeat data about a wallet's data collection practices. x.com/polymutex/stat…
From Twitter
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share
Relevant content