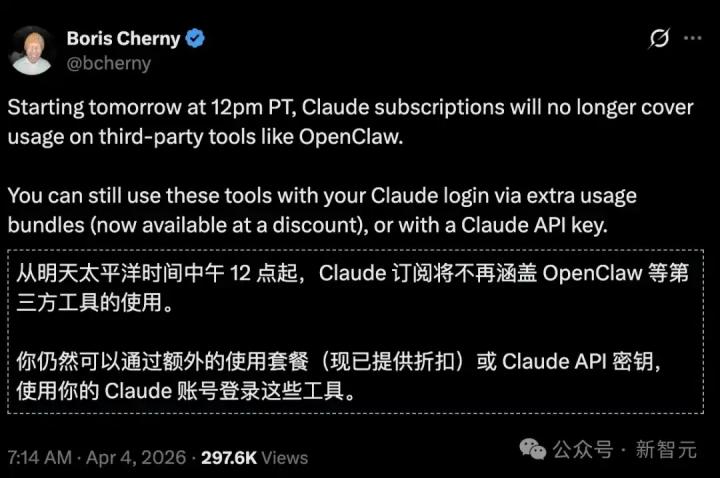
According to Mars Finance, on March 15th, OKX founder and CEO Star responded to the "hacking attack incident by Wuhan Anjun Technology team exploiting a plugin vulnerability," stating that "the OKX Wallet security team has completed its investigation, and the original description of it as an 'OKX wallet vulnerability' is inaccurate. Two points need clarification: • This incident is not a security vulnerability in the OKX Web3 wallet. The attack method involved hackers using Trojan software to control the user's device, then stealing locally stored encrypted files and passwords by modifying the webpage's JS code to implant hooks or by monitoring keystrokes. • The OKX Web3 wallet is a 100% self-custodied wallet. Private keys and passwords only exist on the user's own device; OKX cannot access or control user assets. However, if the user's device itself has been controlled by a hacker, then no wallet—including MetaMask—can guarantee security. This is like a thief being able to operate your computer and see all your keystrokes. Users are advised to avoid installing software or plugins from unknown sources, regularly check device security, and properly protect seed phrase and private keys." According to reports, the Wuhan Anjun Technology team stole seed phrase and remotely transferred digital assets by controlling a large number of user terminals, with the amount involved reaching 7 million US dollars.
OKX Star clarifies: The attack on Wuhan Anjun Technology was not a security vulnerability in the OKX Web3 wallet.
This article is machine translated
Show original

Source
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share
Relevant content