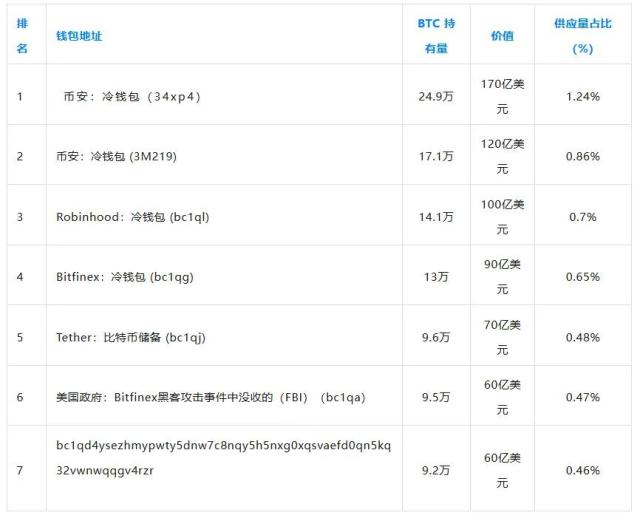
Binance is successfully attracting institutional trading activity, but a wave of data security concerns among retail investors threatens to further complicate the exchange's growth ambitions.
The world's largest cryptocurrency exchange by market Capital has started 2026 strongly in the over-the-counter (OTC) trading segment. In January and February alone, Binance's OTC platform recorded volume accounting for 25% of the total for the entire year of 2025.
A captcha bypass error exposed the information of 1.5 million Binance users in a data scanning attack.
This surge reflects the market's maturity, as large and institutional investors increasingly demand access to private trading channels to execute large-volume transactions.
Richard Teng, CEO of Binance, explained that these institutions prioritize deep liquidation to avoid slippage and significant market impact. The exchange's OTC desk allows buyers and sellers to execute trades directly , helping to keep strategies secure from public Order Book .
However, beneath this positive surface, several warning signs about operational issues are increasing .
On March 28, 2026, cybersecurity platform VECERT reported that an individual using the alias PexRat was selling a private database containing personal information of 1.5 million Binance users .
The leaked data reportedly includes full names, email addresses, phone numbers, and KYC verification status.
Even more concerning, this attacker also claims to have the last logged-in IP address, user device information, and two-factor authentication (2FA) status, such as when users use SMS, email, or separate app authentication.
In addition, the potential for 2FA logs and KYC data leaks is also a major risk, making affected users vulnerable to SIM-Swap attacks and sophisticated phishing campaigns .
Notably, according to VECERT's analysis of authentication logs and data samples, Binance's internal servers were not directly hacked. Instead, this was a professional account theft campaign that used the exact same stolen account and automated anti-bot encryption.
"Evidence suggests that the attacker bypassed or exploited limitations in security mechanisms (such as Captchas) at the login interface or certain platform APIs, allowing persistent requests to be made without being blocked," VECERT explained.
This follows a January 2026 report by cybersecurity researcher Jeremiah Fowler, who discovered approximately 420,000 Binance-related accounts were compromised by similar malware designed to steal information.
Overall, these events serve as a serious test of Binance's security policies , as the exchange cannot afford to allow the automated collection of user data to continue.