Author: Julien Urraca, Fabian Jahr, 0xb10c, CedArctic
Source: https://bitcoinmagazine.com/print/the-core-issue-your-node-vs-the-digital-wilderness
Fifty years ago, the first message on the internet was successfully sent; however, peer-to-peer networks have always been a rarity. Bitcoin's ability to provide an open monetary system is built upon its peer-to-peer network architecture; simultaneously, this networking layer—the discovery and connection of peer nodes—is also the most vulnerable part of its attack surface. There are two main locations where problems arise: Bitcoin's own peer-to-peer protocol, and the internet protocol underlying the Bitcoin protocol. From this perspective, Bitcoin Core bears a dual mission: to protect against denial-of-service (DoS) attacks that could be abused by peer nodes, and to ensure that nodes can communicate securely in the vast hostile environment of the internet.
P2P
Governments are good at shutting down centralized networks (like Napster), but pure peer-to-peer networks (like Gnutella and Tor) seem to be able to operate on their own.
— Satoshi Nakamoto, November 7 , 2008
Bitcoin's peer-to-peer protocol defines how nodes exchange information about transactions, blocks, and other peers. This information exchange is a prerequisite for any transaction to propagate and for consensus to be verified, and is therefore of paramount importance.
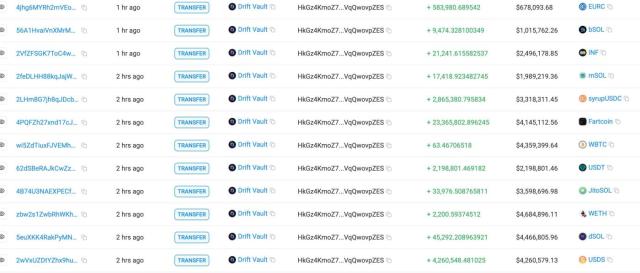
Over the years, several bugs have emerged in this field. For example, a malicious SOCKS server vulnerability was patched and disclosed in 2017. In 2020 , a high-risk vulnerability was reported: a remote peer node could allow a local node to block connections to certain IP addresses, causing this block list to grow exponentially, thus constituting a DoS attack on the node; this vulnerability was patched that year but not disclosed until 2024. This bug was rightly marked as "high-risk" because such attacks are easy to execute, result in the victim node becoming inoperable, and require very few prerequisites for a successful attack. This is the kind of bug that keeps Bitcoin Core developers working through the night, which is why we strongly recommend upgrading your software to a maintained version (very old Bitcoin Core versions will no longer receive active maintenance/upgrades).
This distributed network, which we call "Bitcoin," is relatively small: its clearnet nodes hover around 20,000, and even assuming 100,000 Tor nodes, it remains a small and easily monitored network. Recently, Daniela Brozzoni and naiyoma proved that if a node is running both the clearnet port and the Tor port simultaneously, it's easy to associate its IPv4 network address with its Tor network address.<sup> 4 </sup> Intelligence agencies and blockchain analytics firms are likely already doing this. Once the nodes' network addresses are identified, it's easy to notice which nodes published which transaction first—that is, the originating IP of each transaction—and then use that IP to pinpoint the transactor's location. While this isn't exactly a bug, as nodes don't crash or deviate from their intended path, it can be considered a vulnerability because it provides a way to associate an IP address with a transaction.
How to prevent this method remains an open question.
World Wide Web Desert
We build computers like we build cities. Brick by brick, without a plan, unwilling to leave behind ruins.
— Ellen Ullman 5
Bitcoin operates on the Internet, and its ability to maintain a distributed, decentralized system depends on the inherent properties of the Internet itself. Unfortunately, the Internet's architecture, as we know it, remains highly insecure to this day, with various known attacks still occurring. The vast majority of these attacks remain undetected until they cause real damage, not to mention the ubiquitous surveillance on the Internet today.
The most well-known and practical attack technique to be concerned about is called an "eclipse attack," where a group of malicious nodes completely surround a victim node, providing it with a unique perspective of the network and blockchain. This attack is rooted in distributed systems; once you control all of a node's peers, you control its understanding of the network. Ethan Heilman and his collaborators demonstrated one of the earliest practical eclipse attacks at USENIX 2015<sup> 6</sup> ; in 2018, the Erebus attack paper described a "stealthy" eclipse attack launched through a malicious Autonomous System (AS) <sup>7 </sup>.
These attacks largely exploit weaknesses in how the networks that make up the internet communicate with each other, such as autonomous system routing topologies or a protocol called Border Gateway Protocol (BGP). While there are projects under development to protect the BGP protocol—BGPsec, RPKI—they all have well-known limitations, so internet administrators are still yearning for more robust solutions. Until then, the internet will remain the Wild West.
A recent analysis from cedarctic of Chaincode Labs revealed that Bitcoin nodes are distributed across only 4,551 autonomous systems, a tiny fraction of the network of units that make up the internet. They described a set of attacks that could launch an Eclipse attack by brute -forcing the upstream autonomous systems these nodes reside in. The sparse distribution of these nodes across the anonymous systems, and the specific relationships between these systems, creates a unique attack interface. While remediation exists, it remains unclear whether Bitcoin users or adversaries will understand this attack interface first.
Any attack that requires breaching one or more autonomous systems demands resources, collaboration, and skill. While no one has yet reported a successful attack on a Bitcoin node, such attacks have been successful on miners , wallet software , swap platforms , and bridging contracts . While we cannot fix the internet, we can equip nodes with the tools to survive in such a hostile environment.
Cyber weaponry
The following are some features and functionalities that Bitcoin Core has developed or integrated to protect users from network-level attacks:
TOR (Onion Routing) was the first privacy-preserving overlay network integrated into Bitcoin Core . It creates random hops in the peer-to-peer network to obfuscate traffic.
v2transport 13 encrypts connections between peer nodes, hiding the content of traffic from monitors and censors. Its purpose is to prevent passive network observers from snooping on your communications with other nodes.
I2P (Invisible Internet) 14 is an optional feature in Bitcoin Core that enables an additional, privacy-preserving, cryptographic layer for connections. It's a Tor-like anonymous network that relies on peer nodes to obfuscate traffic between clients and servers.
ASmap 15 is another optional feature in Bitcoin Core that implements a mitigation measure against Erebus attacks (summarized in the paper by the authors and applicable to all attacks based on autonomous systems). By making Bitcoin's peer-to-peer mechanism aware of the autonomous systems its peers reside in and ensuring peer diversity, Eclipse attacks become much more difficult, as the attacker would need to compromise multiple autonomous systems, which is very difficult (if not impossible) to remain undetected. Starting with version 20.0, Bitcoin Core supports obtaining a mapping from an IP network to its autonomous system (an AS map), and the Kartograf project allows any user to easily generate such AS maps.
The internet may still have many weaknesses, and one thing we can do is observe the actions of our peer nodes and try to detect malicious activity. This is the original intention of the " Peer Node Observer Project " initiated by 0xb10c 16. It provides a complete logging system based on eBPF observation points (to observe the most minute actions of a program running on an operating system) to observe the activity of a node, including the behavior of peer nodes. It also provides everything you need to customize your own logging system.
Bitcoin must be strong
The ability to secure connections to peer nodes and exchange messages is the keystone that makes Bitcoin work.
Bitcoin lives in a multi-dimensional, hostile environment, with many threats stemming from the inherent limitations of the internet architecture itself. For Bitcoin to survive and thrive, its developers and users must learn to navigate these challenges.
The price of open networks is that we cannot let our guard down.
footnote
1. https://web.mit.edu/gtmarx/www/connect.html ↩
2. https://satoshi.nakamotoinstitute.org/emails/cryptography/4/ ↩
3. https://bitcoincore.org/en/2019/11/08/CVE-2017-18350/ ↩
4. https://bitcoincore.org/en/2024/07/03/disclose-unbounded-banlist/ ↩
5. https://delvingbitcoin.org/t/fingerprinting-nodes-via-addr-requests/1786/ ↩
6. https://en.wikiquote.org/wiki/Ellen_Ullman ↩
7. https://www.usenix.org/system/files/conference/usenixsecurity15/sec15-paper-heilman.pdf
8. https://ihchoi12.github.io/assets/tran2020stealthier.pdf ↩
9. https://delvingbitcoin.org/t/eclipsing-bitcoin-nodes-with-bgp-interception-attacks/1965
10. https://www.theregister.com/2014/08/07/bgp_bitcoin_mining_heist/ ↩
11. https://www.theverge.com/2018/4/24/17275982/myetherwallet-hack-bgp-dns-hijacking-stolen-ethereum ↩
12. https://medium.com/s2wblog/post-mortem-of-klayswap-incident-through-bgp-hijacking-en-3ed7e33de600 ↩
13. www.coinbase.com/blog/celer-bridge-incident-analysis ↩
14. https://bitcoinops.org/en/topics/v2-p2p-transport/ ↩
16. https://asmap.org ↩