crazy that the attacker almost lost-out due to a prescheduled multisig change, then was again able to compromise a new multisig member on the new multisig to continue the attack...I really hope @DriftProtocol uncovers and fully explains what social engineering attack was used...

Drift
@DriftProtocol
Below is the timeline of events.
March 23: Initial Nonce Setup
Four durable nonce accounts were created:
- Two associated with Drift Security Council multisig members
- Two associated with attacker-controlled accounts
Relevant accounts:
a.
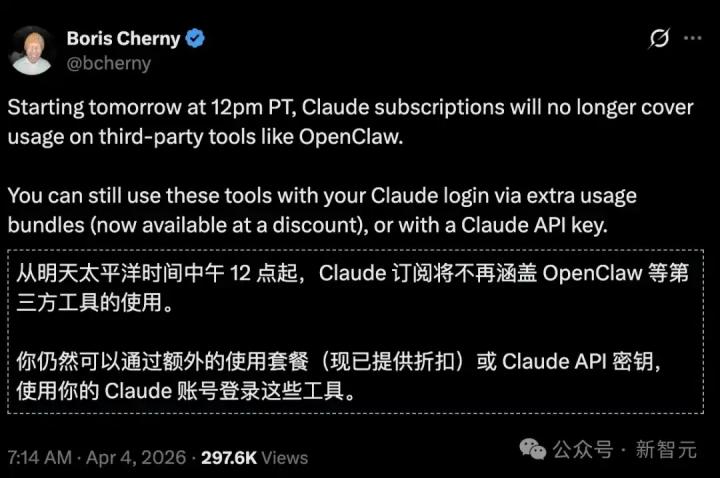
From Twitter
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share
Relevant content