Author: Beosin
Foreword
This research report was initiated by the Blockchain Security Alliance and co-authored by alliance members Beosin and Footprint Analytics, aiming to comprehensively explore the development of the global blockchain security landscape in 2024. Through the analysis and evaluation of the current state of global blockchain security, the report will reveal the security challenges and threats faced, and provide solutions and best practices.
Through this report, readers will be able to gain a more comprehensive understanding of the dynamic evolution of the Web3 blockchain security landscape. This will help readers assess and address the security challenges in the blockchain field. In addition, readers can also obtain valuable recommendations on security measures and industry development directions from the report, to help them make wise decisions and take actions in this emerging field. Blockchain security and regulation are key issues in the development of the Web3 era. Through in-depth research and discussion, we can better understand and address these challenges, and promote the security and sustainable development of blockchain technology.
1. Overview of the Web3 Blockchain Security Landscape in 2024

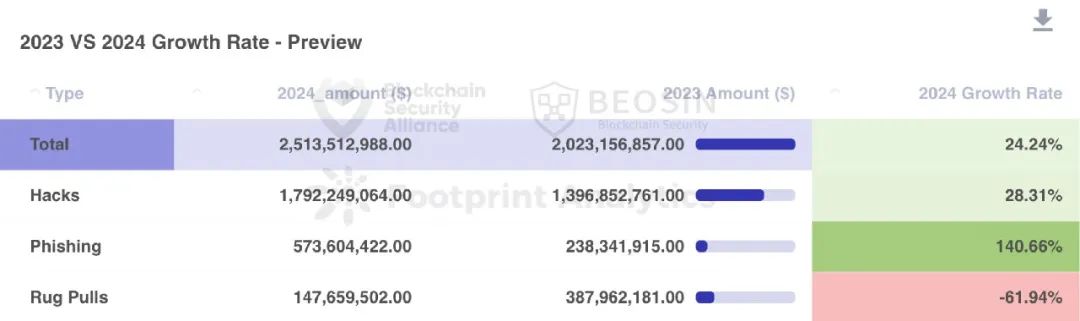
According to the monitoring of the Alert platform under the security audit company Beosin, the total loss in the Web3 field in 2024 due to hacker attacks, phishing scams, and Rug Pull by project parties reached $2.513 billion. Among them, there were 131 major attack incidents, with a total loss of about $1.792 billion; 68 Rug Pull incidents by project parties, with a total loss of about $148 million; and the total loss from phishing scams was about $574 million.
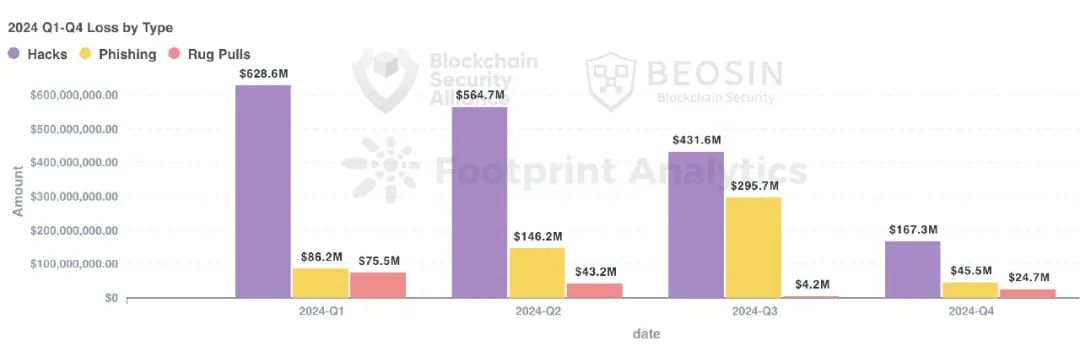
In 2024, the amount of hacker attacks and phishing scams has increased significantly compared to 2023, with phishing scams increasing by 140.66% compared to 2023. The loss amount of Rug Pull incidents by project parties has decreased significantly, down about 61.94%.
In 2024, the types of projects attacked include DeFi, CEX, DEX, public chains, cross-chain bridges, wallets, payment platforms, gambling platforms, crypto brokers, infrastructure, password managers, development tools, MEV bots, TG bots, and more. DeFi is the project type with the highest frequency of attacks, with 75 attacks on DeFi causing a loss of about $390 million. CEX is the project type with the highest total loss amount, with 10 attacks on CEX causing a loss of about $724 million.
In 2024, there were more types of public chains attacked, with multiple security incidents involving theft across multiple chains. Ethereum remains the public chain with the highest loss amount, with 66 attack incidents on Ethereum causing a loss of about $844 million, accounting for 33.57% of the total annual loss.
In terms of attack methods, 35 private key leakage incidents caused a loss of about $1.306 billion, accounting for 51.96% of the total loss, which is the attack method that caused the most loss.
Contract vulnerability exploitation is the attack method with the highest frequency, with 76 out of the 131 attack incidents, accounting for 58.02%, coming from contract vulnerability exploitation.
About $531 million of the stolen funds were recovered throughout the year, accounting for about 21.13%. About $109 million of the stolen funds were transferred to mixers, accounting for about 4.34% of the total stolen funds, a decrease of about 66.97% compared to 2023.
2. Top 10 Security Incidents in the Web3 Ecosystem in 2024
In 2024, there were 5 attack incidents with losses over $100 million: DMM Bitcoin ($304 million), PlayDapp ($290 million), WazirX ($235 million), Gala Games ($216 million), and the theft from Chris Larsen ($112 million). The total loss of the top 10 security incidents was about $1.417 billion, accounting for about 79.07% of the total annual attack incident amount.
No.1 DMM Bitcoin
Loss Amount: $304 million
Attack Method: Private Key Compromise
On May 31, 2024, the Japanese cryptocurrency exchange DMM Bitcoin was attacked, and Bitcoin worth over $304 million was stolen. The hackers scattered the stolen funds to more than 10 addresses in an attempt to launder the money.
No.2 PlayDapp
Loss Amount: $290 million
Attack Method: Private Key Compromise
On February 9, 2024, the blockchain game platform PlayDapp was attacked, and the hackers minted 2 billion PLA tokens worth $365 million. After failing to negotiate with PlayDapp, on February 12, the hackers minted 15.9 billion PLA tokens worth $253.9 million and sent some of the funds to the Gate exchange. The PlayDapp project team then temporarily suspended the PLA contract and migrated the PLA tokens to the PDA token.
No.3 WazirX
Loss Amount: $235 million
Attack Method: Network Attack and Phishing
On July 18, 2024, a multi-signature wallet of the Indian cryptocurrency exchange WazirX was hacked, with over $230 million stolen. The multi-signature wallet was a Safe wallet smart contract wallet. The attackers lured the multi-signature signers to sign an upgrade transaction, and through the upgraded contract, they were able to directly transfer the assets in the wallet, ultimately transferring over $230 million in assets.
No.4 Gala Games
Loss Amount: $216 million
Attack Method: Access Control Vulnerability
On May 20, 2024, a privileged address in Gala Games was compromised, and the attacker used this address to directly mint 5 billion GALA tokens worth about $216 million through the token's mint function, and then gradually exchanged the minted tokens for ETH. Subsequently, the Gala Games team used the blacklist function to block the hacker and recovered the losses.
No.5 Chris Larsen (Ripple's co-founder)
Loss Amount: $112 million
Attack Method: Private Key Compromise
On January 31, 2024, Ripple's co-founder Chris Larsen reported that his four wallets were hacked, resulting in a total loss of about $112 million. The Binance team successfully froze $4.2 million worth of the stolen XRP tokens.
No.6 Munchables
Loss Amount: $62.5 million
Attack Method: Social Engineering Attack
On March 26, 2024, the Web3 game platform Munchables based on Blast was attacked, resulting in a loss of about $62.5 million. The reason the project was attacked was that it had hired North Korean hackers as developers. All the stolen funds were eventually returned by the hackers.
No.7 BTCTurk
Loss Amount: $55 million
Attack Method: Private Key Compromise
On June 22, 2024, the Turkish cryptocurrency exchange BTCTurk was attacked, resulting in a loss of about $55 million. Binance assisted in freezing over $5.3 million of the stolen funds.
No.8 Radiant Capital
Loss Amount: $53 million
Attack Method: Private Key Compromise
On October 17, 2024, the multi-chain lending protocol Radiant Capital was attacked. The attacker illegally obtained the permissions of 3 out of the 11 owners of the Radiant Capital multi-signature wallet. Due to the 3/11 signature verification mode of this multi-signature wallet, the attacker was able to perform off-chain signing and then initiate an on-chain transaction to transfer the ownership of the Radiant Capital contract to a malicious contract under their control, causing a loss of over $53 million.
No.9 Hedgey Finance
Loss Amount: $44.7 million
Attack Method: Contract Vulnerability
Here is the English translation of the text, with the terms in <> retained as is:On April 19, 2024, Hedgey Finance was attacked multiple times by attackers. The attackers exploited a token approval vulnerability to steal a large amount of tokens from the ClaimCampaigns contract, with the value of tokens stolen from the Ethereum chain exceeding $2.1 million and the value of tokens stolen from the Arbitrum chain being around $42.6 million.
No.10 BingX
Loss Amount: $44.7 million
Attack Method: Private Key Leak
On September 19, 2024, the BingX exchange's hot wallet was hacked by attackers. Although BingX activated an emergency plan, including urgently transferring assets and suspending withdrawals, according to Beosin's statistics, the total loss of assets from the abnormal outflow of the hot wallet reached $44.7 million, involving assets from Ethereum, BNB Chain, Tron, Polygon, Avalanche, Base, and other blockchains.
3. Types of Attacked Projects
In addition to the common types such as DeFi, CEX, DEX, public chains, cross-chain bridges, and wallets, the projects attacked in 2024 also included payment platforms, gambling platforms, crypto brokers, infrastructure, password managers, development tools, MEV bots, and Telegram bots.
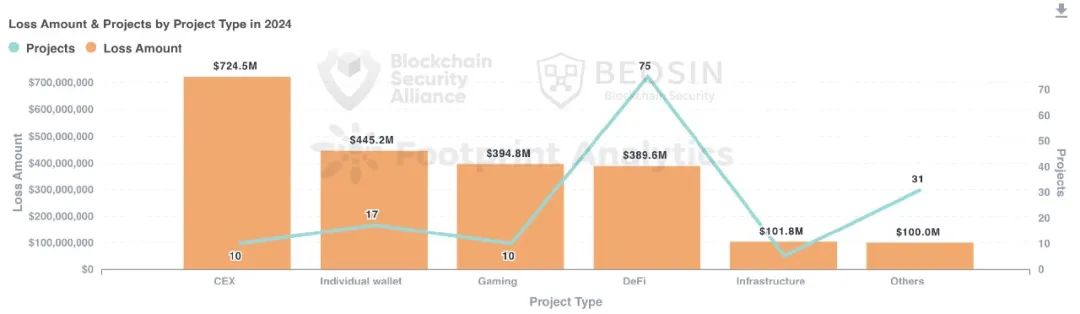
DeFi projects were attacked 75 times in 2024, making them the most frequently attacked project type (about 50.70%). The total loss of DeFi attacks was about $390 million, accounting for about 15.50% of the total loss, making it the 4th highest in terms of loss amount.
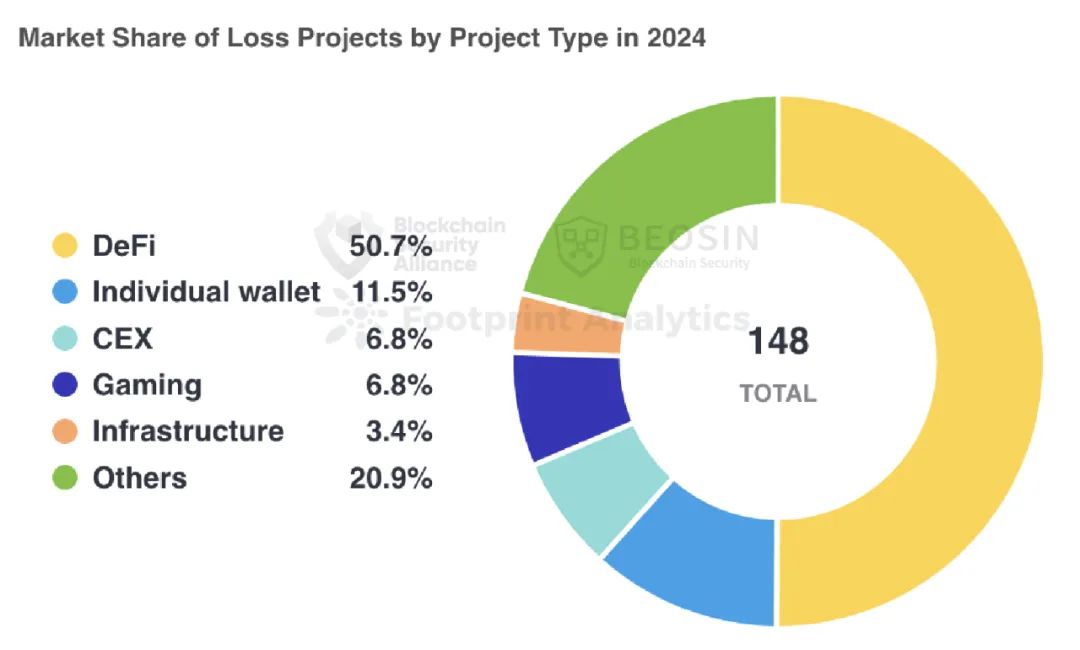
CEXs (centralized exchanges) had the highest loss amount, with 10 attacks causing about $724 million in losses, making them the project type with the highest loss amount. Overall, exchange types experienced frequent security incidents in 2024, and exchange security remains the biggest challenge in the Web3 ecosystem.
Personal wallets had the second-highest loss amount, with a total loss of about $445 million. 12 attacks targeting crypto whales and a large number of phishing attacks and social engineering attacks on ordinary users have caused the total loss of personal wallets to increase by 464.72% compared to 2023, making it the second-biggest challenge after exchange security.
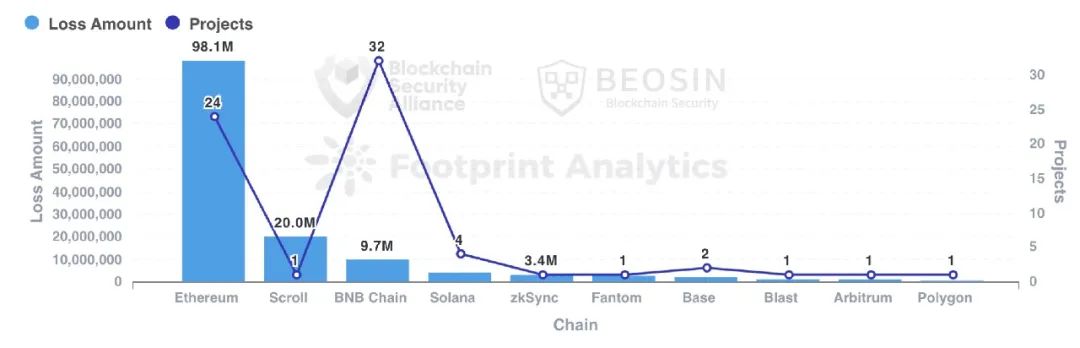
4. Loss Amount Situation for Different Chains
Compared to 2023, the types of public chains that experienced attacks in 2024 were more diverse. The top five in terms of loss amount are Ethereum, Bitcoin, Arbitrum, Ripple, and Blast:
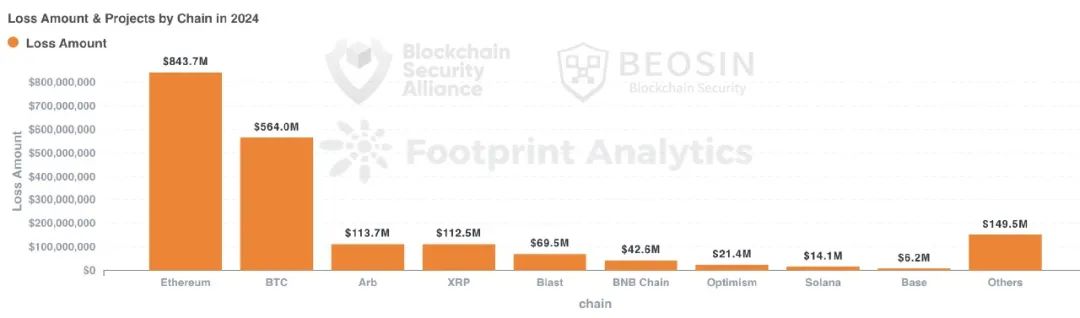
The top six in terms of the number of attack incidents are Ethereum, BNB Chain, Arbitrum, Others, Base, and Solana:
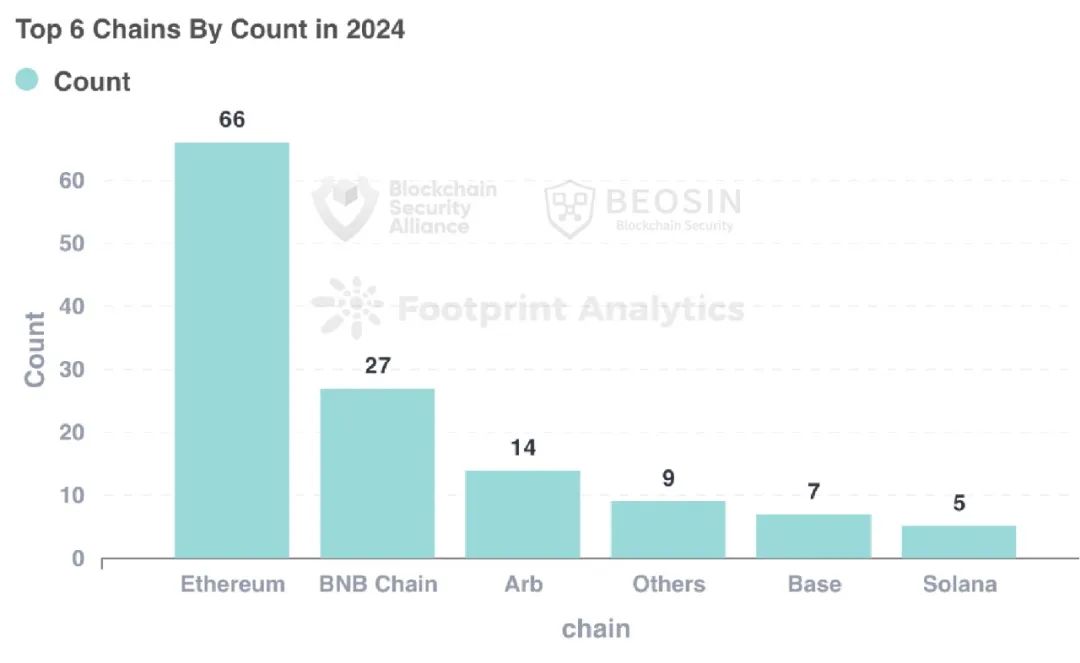
Similar to 2023, Ethereum remains the public chain with the highest loss amount. 66 attack incidents on Ethereum caused about $844 million in losses, accounting for 33.59% of the total annual loss.
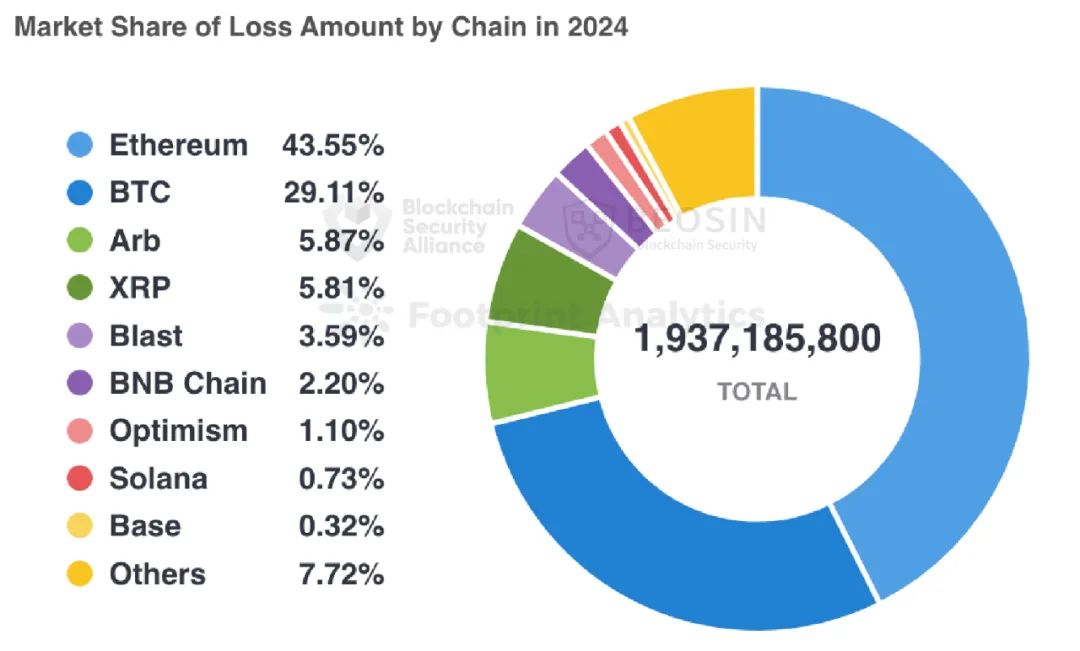 Note: The total loss data does not include on-chain phishing losses and some CEX hot wallet losses.
Note: The total loss data does not include on-chain phishing losses and some CEX hot wallet losses.
The Bitcoin network's loss is ranked second, with a single security incident loss reaching $238 million. The third is Arbitrum, with a total loss of about $114 million.
5. Attack Method Analysis
The attack methods in 2024 were highly diversified, including not only common contract vulnerability attacks but also various other attack methods, such as supply chain attacks, third-party service provider attacks, man-in-the-middle attacks, DNS attacks, and front-end attacks.
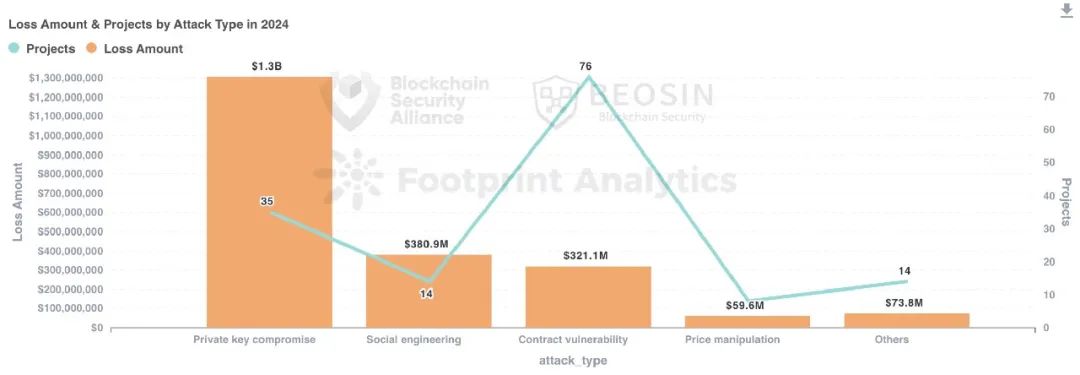
In 2024, 35 private key leakage incidents caused a total loss of $1.306 billion, accounting for 51.96% of the total loss, making it the attack method that caused the most loss. Major private key leakage incidents that caused significant losses include: DMM Bitcoin ($304 million), PlayDapp ($290 million), Ripple co-founder Chris Larsen ($112 million), BTCTurk ($55 million), Radiant Capital ($53 million), BingX ($44.7 million), and DEXX ($21 million).
Contract vulnerability exploitation is the attack method with the highest frequency, with 76 out of 131 attack incidents coming from contract vulnerability exploitation, accounting for 58.02%. The total loss caused by contract vulnerabilities is about $321 million, ranking third in terms of loss amount.
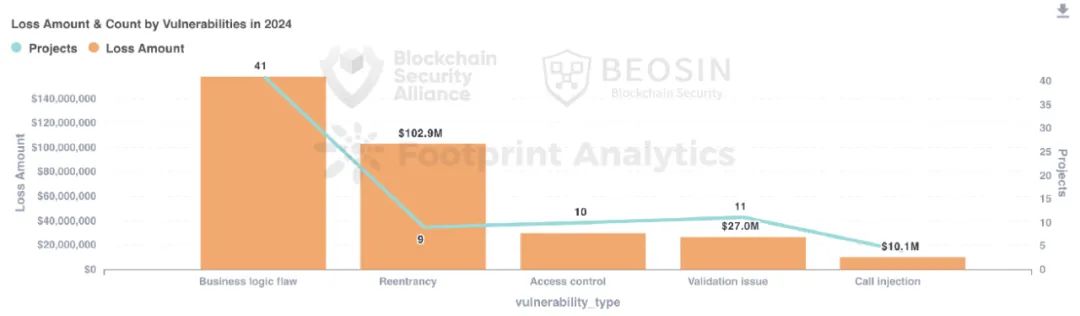
In terms of vulnerability breakdown, business logic vulnerabilities have the highest frequency and cause the most losses, accounting for about 53.95% of the loss amount from contract vulnerability incidents, causing a loss of about $158 million.
6. Anti-Money Laundering Typical Incident Analysis
6.1 Polter Finance Security Incident
Incident Overview
On November 17, 2024, according to Beosin Alert's monitoring and warning, the FTM chain lending protocol Polter Finance was attacked, and the attacker used a flash loan to manipulate the token price in the project's contract to profit.
Vulnerability and Fund Analysis
The attacked LendingPool contract (0xd47ae558623638f676c1e38dad71b53054f54273) used 0x6808b5ce79d44e89883c5393b487c4296abb69fe as the oracle, and this oracle used a recently deployed price feed contract (0x80663edff11e99e8e0b34cb9c3e1ff32e82a80fe). This price feed contract used the token reserves in the uniswapV2_pair (0xEc71) contract, which can be attacked by the attacker using a flash loan, resulting in a price manipulation vulnerability.
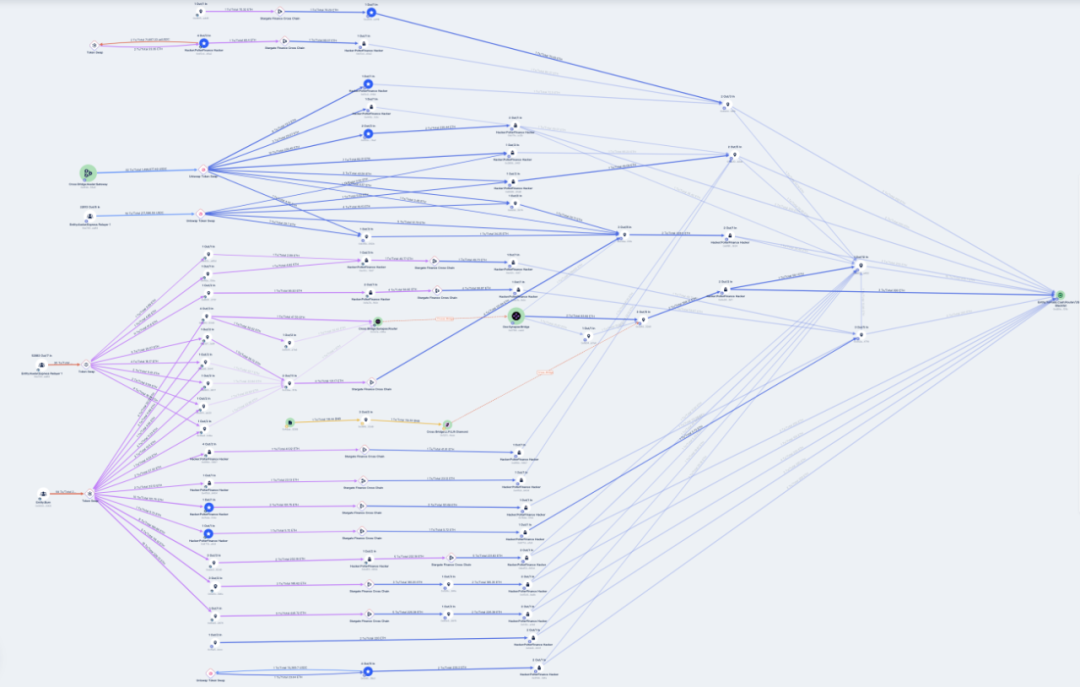
The attacker used a flash loan to artificially inflate the $BOO token value, then borrowed other crypto assets. Subsequently, the stolen funds were converted to FTM tokens and then cross-chained to the ETH chain, with all the funds stored on the ETH chain. The following is a schematic diagram of the fund flow process on the ARB chain and ETH chain:
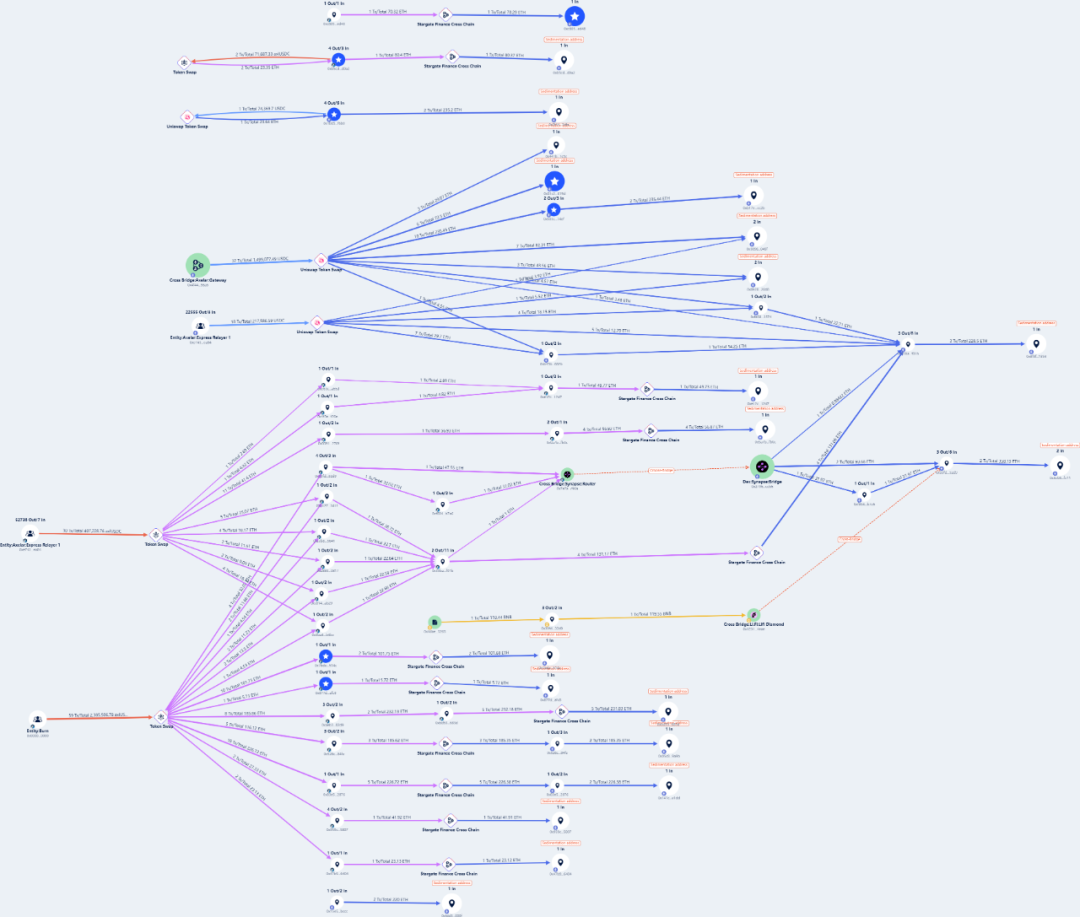
On November 20, the attacker continued to transfer over 2,625 ETH to Tornado Cash, as shown in the following image:
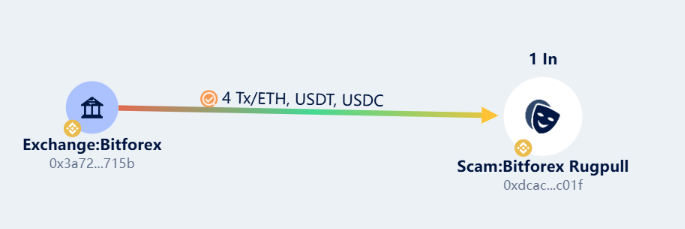
6.2 BitForex Security Incident
Incident Overview
On February 23, 2024, the well-known on-chain investigator ZachXBT revealed through his analysis tool that BitForex's hot wallet experienced an outflow of about $56.5 million, and the platform temporarily suspended withdrawal services during this process.
Fund Analysis
The Beosin security team conducted an in-depth trace and analysis of the BitForex incident:
Ethereum
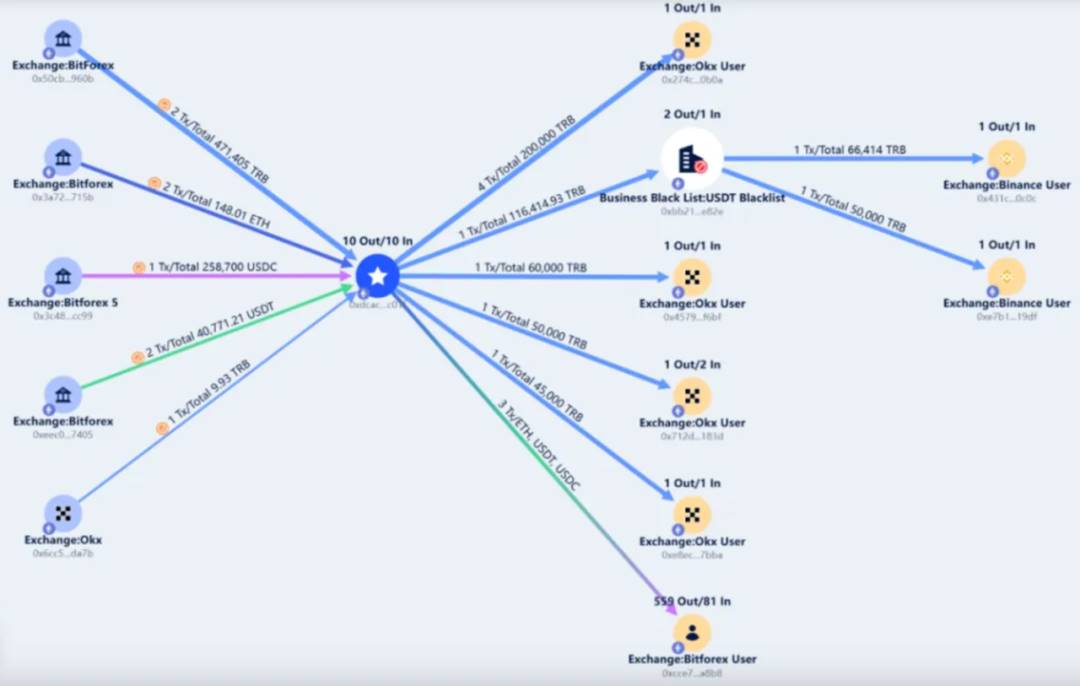
On February 24, 2024, at 6:11 (UTC+8), BitForex exchange began to transfer 40,771 USDT, 258,700 USDC, 148.01 ETH, and 471,405 TRB to the Ethereum exit address (0xdcacd7eb6692b816b6957f8898c1c4b63d1fc01f).
Subsequently, on August 9 (Beijing time), the exit address transferred all the tokens except TRB (including 147.9 ETH, 40,771 USDT, and 258,700 USDC) back to the BitForex exchange account (0xcce7300829f49b8f2e4aee6123b12da64662a8b8).
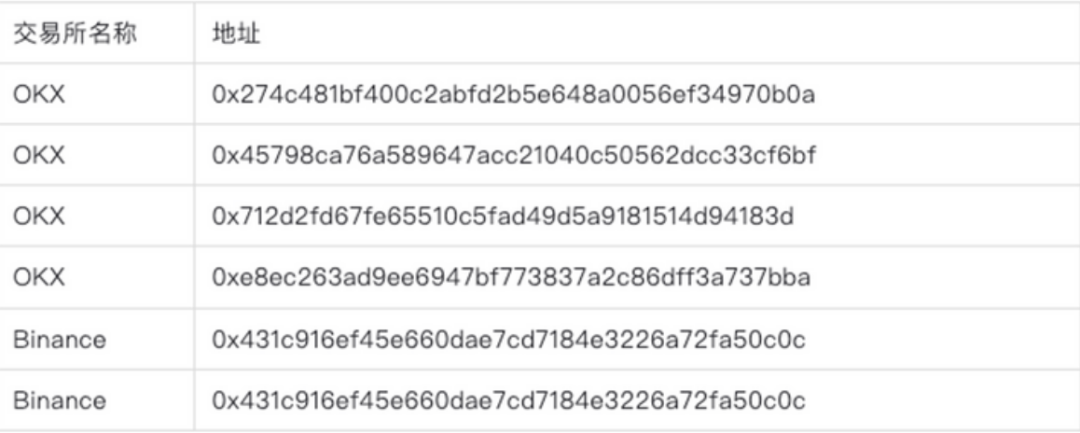
Then, from November 9 to November 10 (Beijing time), the exit address transferred 355,000 TRB to four different OKX exchange user addresses through 7 transactions:
0x274c481bf400c2abfd2b5e648a0056ef34970b0a
0x45798ca76a589647acc21040c50562dcc33cf6bf
0x712d2fd67fe65510c5fad49d5a9181514d94183d
0xe8ec263ad9ee6947bf773837a2c86dff3a737bba
Subsequently, the exit address transferred the remaining 116,414.93 TRB to an intermediate address (0xbb217bd37c6bf76c6d9a50fefc21caa8e2f2e82e), and this address then transferred all the TRB to two different Binance exchange users in two transactions.
0x431c916ef45e660dae7cd7184e3226a72fa50c0c
0xe7b1fb77baaa3bba9326af2af3cd5857256519df
BNB Chain
On February 24, the Bitforex exchange withdrew 166 ETH, 46,905 USDT, and 57,810 USDC to the BNB Chain address (0xdcacd7eb6692b816b6957f8898c1c4b63d1fc01f), which has remained dormant until now.
Polygon
On February 24, Beijing time, the Bitforex exchange withdrew 99,000 MATIC, 20,300 USDT, and 1,700 USDC to the POL chain address: 0xdcacd7eb6692b816b6957f8898c1c4b63d1fc01f.
Among them, 99,000 MATIC was transferred to the address 0xcce7300829f49b8f2e4aee6123b12da64662a8b8 on August 9 and has remained dormant since then, while the remaining USDT and USDC tokens have remained dormant until now.

TRON
On February 24, the Bitforex exchange withdrew 44,000 TRX and 657,698 USDT to the TRON chain address TQcnqaU4NDTR86eA4FZneeKfJMiQi7i76o. On August 9, the above tokens were all transferred back to the Bitforex exchange user address: TGiTEXjqx1C2Y2ywp7gTR8aYGv8rztn9uo.

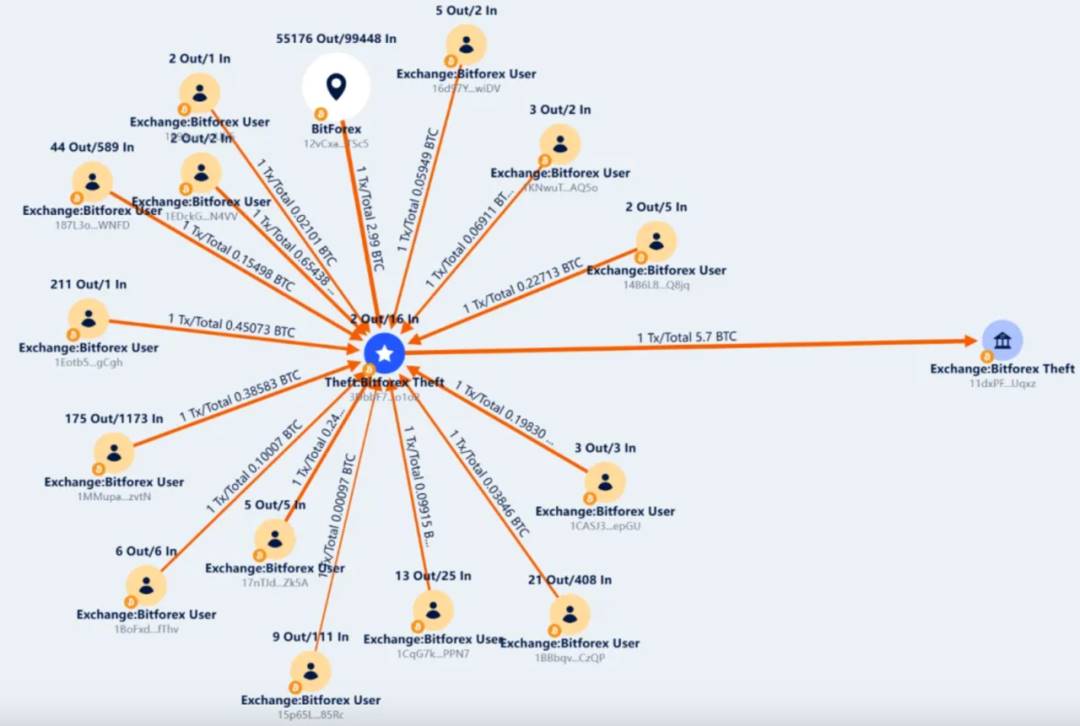
Bitcoin
Starting on February 24, a total of 16 Bitforex addresses gradually transferred a total of 5.7BTC to the BTC chain address 3DbbF7yxCR7ni94ANrRkfV12rJoxrmo1o2. This address then transferred the 5.7BTC back to the Bitforex exchange address: 11dxPFQ8K9pJefffHE4HUwb2aprzLUqxz on August 9.
In summary, on February 24, the Bitforex exchange transferred 40,771 USDT, 258,700 USDC, 148.01 ETH, and 471,405 TRB to the ETH chain; 44,000 TRX and 657,698 USDT to the TRON chain; 5.7 BTC to the BTC chain; 166 ETH, 46,905 USDT, and 57,810 USDC to the BNB Chain; and 99,000 MATIC, 20,300 USDT, and 1,700 USDC to the Polygon chain. On August 9, it transferred all tokens on the BTC chain, TRON chain, and ETH chain (except TRB tokens) back to the Bitforex exchange, and on November 9 and 10, it transferred all 471,405 TRB to 4 OKX accounts and 2 Binance accounts. At this point, all tokens on the ETH chain, TRON chain, and BTC chain have been transferred, with 166 ETH, 46,905 USDT, and 57,810 USDC remaining dormant on BSC, and 99,000 MATIC, 20,300 USDT, and 1,700 USDC remaining dormant on POL.
Attached are the deposit addresses for TRB:
7. Analysis of the Flow of Stolen Assets
In 2024, approximately $1.312 billion of the stolen funds remained in the hacker's addresses (including cases of cross-chain transfers and distribution to multiple addresses), accounting for 52.20% of the total stolen funds. Compared to last year, hackers this year tend to use multi-chain money laundering and distribute the stolen funds to many addresses, rather than directly using a mixer. The increase in the number of addresses and the complexity of the money laundering paths have undoubtedly increased the difficulty for projects and regulatory authorities to investigate.
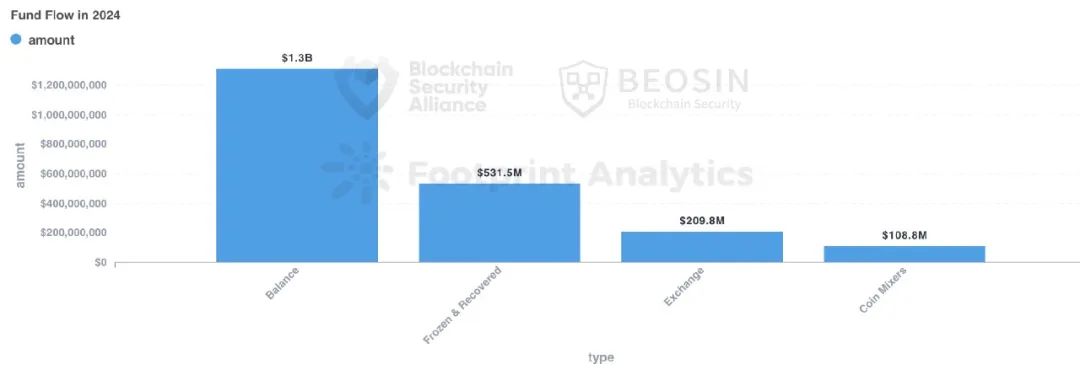
Approximately $531 million of the stolen funds were recovered, accounting for about 21.13%. In 2023, the recovered funds were approximately $295 million.
Approximately $109 million of the stolen funds were transferred to mixers, accounting for about 4.34% of the total stolen funds. Since the US OFAC sanctioned Tornado Cash in August 2022, the amount of stolen funds transferred to Tornado Cash has decreased significantly.
8. Analysis of Project Auditing Situation
Among the 131 attack incidents, 42 incidents involved projects that were not audited, 78 incidents involved projects that were audited, and the audit status of 11 incidents could not be confirmed.
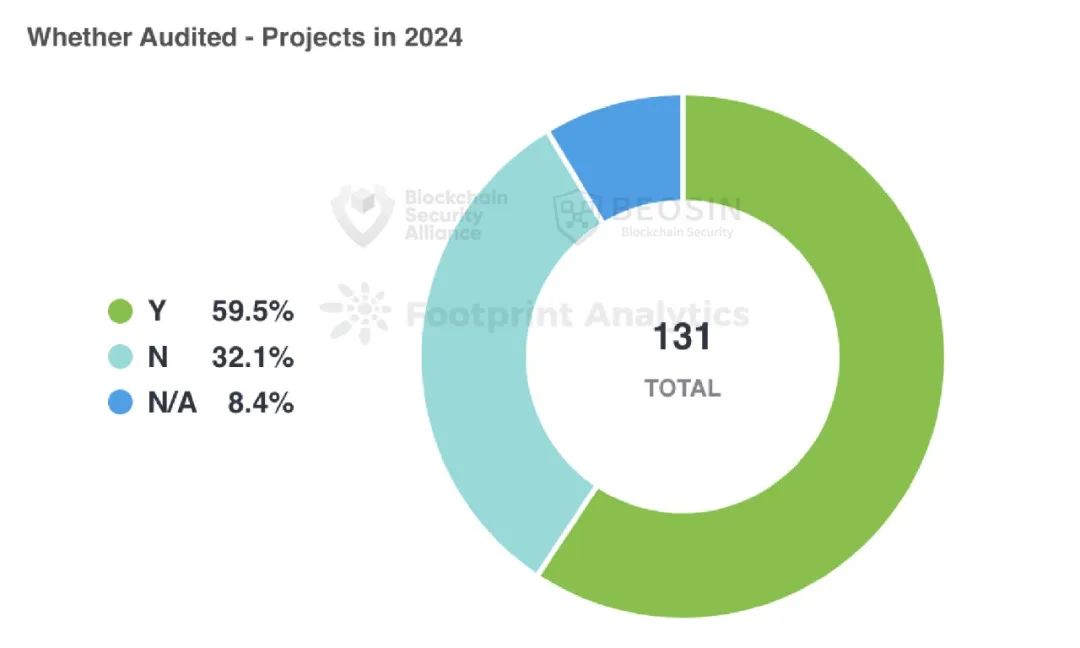
Among the 42 unaudited projects, contract vulnerability incidents accounted for 30 (about 71.43%). This indicates that projects without audits are more likely to have potential security risks. In comparison, among the 78 audited projects, contract vulnerability incidents accounted for 49 (about 62.82%). This shows that audits can to some extent improve the security of projects.
However, due to the lack of a well-developed regulatory framework in the Web3 market, the quality of audits is uneven, and the results presented are far from expected. To effectively safeguard asset security, it is recommended that projects seek professional security companies for audits before launch.
9. Rug Pull Analysis
In 2024, the Beosin Alert platform monitored a total of 68 major Rug Pull incidents in the Web3 ecosystem, with a total amount involved of about $148 million, a significant decrease from $388 million in 2023.
In terms of amount, among the 68 Rug Pull incidents, there were 9 projects with amounts involved over $1 million, which are Essence Finance ($20 million), Shido Global ($2.4 million), ETHTrustFund ($2.2 million), Nexera ($1.8 million), Grand Base ($1.7 million), SAGA Token ($1.6 million), OrdiZK ($1.4 million), MangoFarmSOL ($1.29 million), and RiskOnBlast ($1.25 million), with a total loss of $33.64 million, accounting for 22.73% of the total loss from all Rug Pull incidents.
Rug Pull projects on Ethereum and BNB Chain accounted for 82.35% of the total, with 24 and 32 incidents respectively, and there was 1 Rug Pull incident over $20 million on Scroll. A small number of Rug Pull incidents also occurred on other chains, including Polygon, BASE, and Solana.
10. Summary of the Web3 Blockchain Security Landscape in 2024
In 2024, the number of on-chain hacking attacks and project Rug Pull incidents has decreased significantly compared to 2023, but the loss amount is still increasing, and phishing attacks are becoming more rampant. The attack method that caused the highest loss is still private key leakage. The main reasons for this change include:
After the rampant hacking activities last year, the entire Web3 ecosystem has paid more attention to security this year, with efforts made by both project parties and security companies in various aspects, such as real-time on-chain monitoring, more emphasis on security audits, and actively drawing lessons from past contract vulnerability exploitation incidents, making it more difficult for hackers to steal funds through contract vulnerabilities. However, project parties still need to strengthen their security awareness in private key management and project operation security.
With the integration of the crypto market and the traditional market, hackers are no longer limited to attacking DeFi, cross-chain bridges, and exchanges, but have turned to attacking payment platforms, gambling platforms, crypto brokers, infrastructure, password managers, development tools, MEV bots, TG bots, and other targets.
In 2024-2025, as the crypto market enters a bull market, with active on-chain funds, this will to some extent attract more hacker attacks. In addition, regulatory policies on crypto assets in various regions are gradually improving to crack down on various criminal activities using crypto assets. Under this trend, it is expected that hacking activities will remain at a high level in 2025, and global law enforcement agencies and regulatory authorities will still face severe challenges.