The argument Canton uses confuses "can someone send a bogus message?" with "can that message have any effect?". Every bank website, FIX gateway or API on the planet is bombarded with unauthorized requests. Compliance is about what executes and settles, not whether packets can be sent. If you use the internet as an analogy, your data packets will traverse any router it thinks is the quickest path. Inevitably, this can mean it hits sanctioned jurisdictions or routers owned by bad actors. No regulator treats that as you "using a terrorist's infrastructure" in any meaningful legal sense, the network fabric is neutral. A base layer blockchain is the same. Neutrality at the base layer (transport/mempool/consensus), with access control and policy enforced at the application/contract layer. This is entirely compatible with the "appropriate systems, policies, procedures, and controls" language you quoted. The fact that unauthorized calls can appear in the mempool is a red herring.
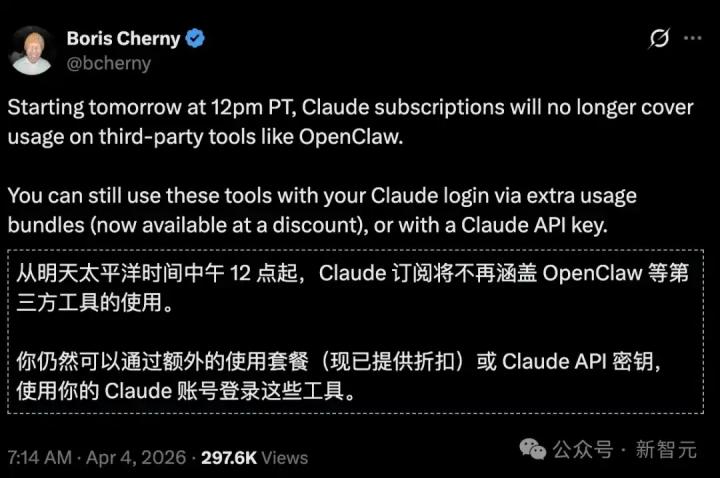
From Twitter
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share