In February 2025, another heavy blow was added to the history of encryption: Safe (Wallet), the industry's most trusted multi-signature scheme, lost $1.6 billion in a front-end attack. This was not due to some profound zero-day exploit or quantum computing breakthrough, but rather to a persistent problem that has existed since the birth of encryption: the inherent weakness of the user interface for manipulating keys.
Since 2020, more than $50 billion has vanished from supposedly secure wallets. The hacker attacks seem to follow a similar pattern: the blockchain was not compromised, the cryptography was not cracked, but the funds mysteriously disappeared. The unacceptable truth is that "secure" wallets are not actually secure – the locks are strong enough, but we often guard the wrong door.
What if the problem lies not in security protection, but in the underlying architecture itself?
1. Assets are on-chain, keys are in the wallet.
A Clarification of the Concept of "Wallet"
First, most people don't realize that wallets don't store crypto assets; your Bitcoin isn't on Ledger, and your Ethereum isn't on MetaMask.
Crypto assets exist on the blockchain, an indestructible and transparent "vault." The authenticity of crypto assets can be verified, but they do not exist in any wallet. The blockchain vault is perfect – it cannot be attacked by hackers, cannot be altered, and exists forever. What you store in your wallet is the key chain to open the vault, not the assets themselves.
Understanding this will reshape our perception of security:
- The Vault : Assets reside in a blockchain vault – distributed across thousands of nodes and protected by mathematical consensus.
- Private Key : The only way to open the vault – once this string of characters is leaked, absolute control over the assets is lost.
- Public Key/Address : The address of an asset on the blockchain – it can be securely shared, just like an email address.
- Digital Signature : Unforgeable authorization – a mathematical credential through which a transaction can be executed.
- Transaction : An instruction signed that allows assets to be transferred.
Once you understand this logic, the security challenges wallets face become crystal clear: assets are very secure on the blockchain, and every hacking attack, every theft, every loss – is because someone exploited a vulnerability to obtain the key.
The question that has driven wallet evolution for 15 years is both simple and complex: how to protect the key?
Evolution of Second and Fourth Generation Key Management Technologies
The history of encrypted wallets is essentially a history of key hiding. Innovations in wallet technology have learned from the failures of previous generations, but have also inevitably introduced new vulnerabilities. Perhaps it is time to avoid problems from the perspective of architectural design.
First generation: Software wallets/hot wallets (2009 to present)
The initial solution was logically sound but old-fashioned: encrypt the key and hide it with a password, then store the user's private key on their device in the form of a seed phrase(12 or 24 words). Users were repeatedly warned to write the seed phrase down on paper, keep it safe, and never lose it.
This method, though seemingly simple, is riddled with vulnerabilities. The software can be hacked, computers can be infected with viruses, clipboard malware can swap addresses, phishing websites can steal seed phrase, and browser extensions can also be compromised. To date, vulnerabilities in software wallets have caused users billions of dollars in losses, and these losses are increasing daily.
The key is stored in the software and is therefore very vulnerable.
Second generation: Hardware wallets/cold wallets (2014 to present)
The industry's response to this is physical isolation. Hardware wallets such as Ledger and Trezor store keys offline in dedicated hardware, without contact with the network. The keys reside in a secure chip and sign transactions inside the device, thus avoiding exposure to the security risks of malicious software.
But new problems arise. Hardware wallets are extremely inconvenient to use – imagine carrying a USB device to buy coffee. They can be lost, stolen, or damaged in daily life. Supply chain attacks can implant malicious code before the device even reaches the user. The well-known Ledger user data breach exposed the addresses of millions of users, meaning that hackers can even move their attacks from online to offline.
Isolation does bring safety, but it comes at the cost of availability.
Third generation: Multi-party secure computation wallet (MPC) (2018 to present)
Multi-party secure computation wallets attempt a different approach: the key is fragmented, with no single participant holding the complete key. Multiple participants must collaborate to sign a transaction, but the key itself is never fully reconstructed in one place.
Institutional clients are very satisfied, as they can finally achieve corporate control over their wallets without the risk of seed phrase. However, MPC has also reintroduced something the crypto world was trying to eliminate: trust. Users must rely on hosting providers who may collude, disappear, be hacked, or simply refuse to provide services.
On October 14, 2025, Privy, an MPC wallet provider, experienced a server outage for two hours due to network load issues, preventing hundreds of thousands of Privy wallet users from making transfers. In addition, the deployment of MPC wallets is relatively complex and costly, and ultimately, the fragments of the keys are entrusted to others. Now, more and more regulatory agencies are beginning to consider MPC wallets to be partially custodied rather than truly self-custodied.
While decentralized trust is better than centralized trust, it still relies on trust in people.
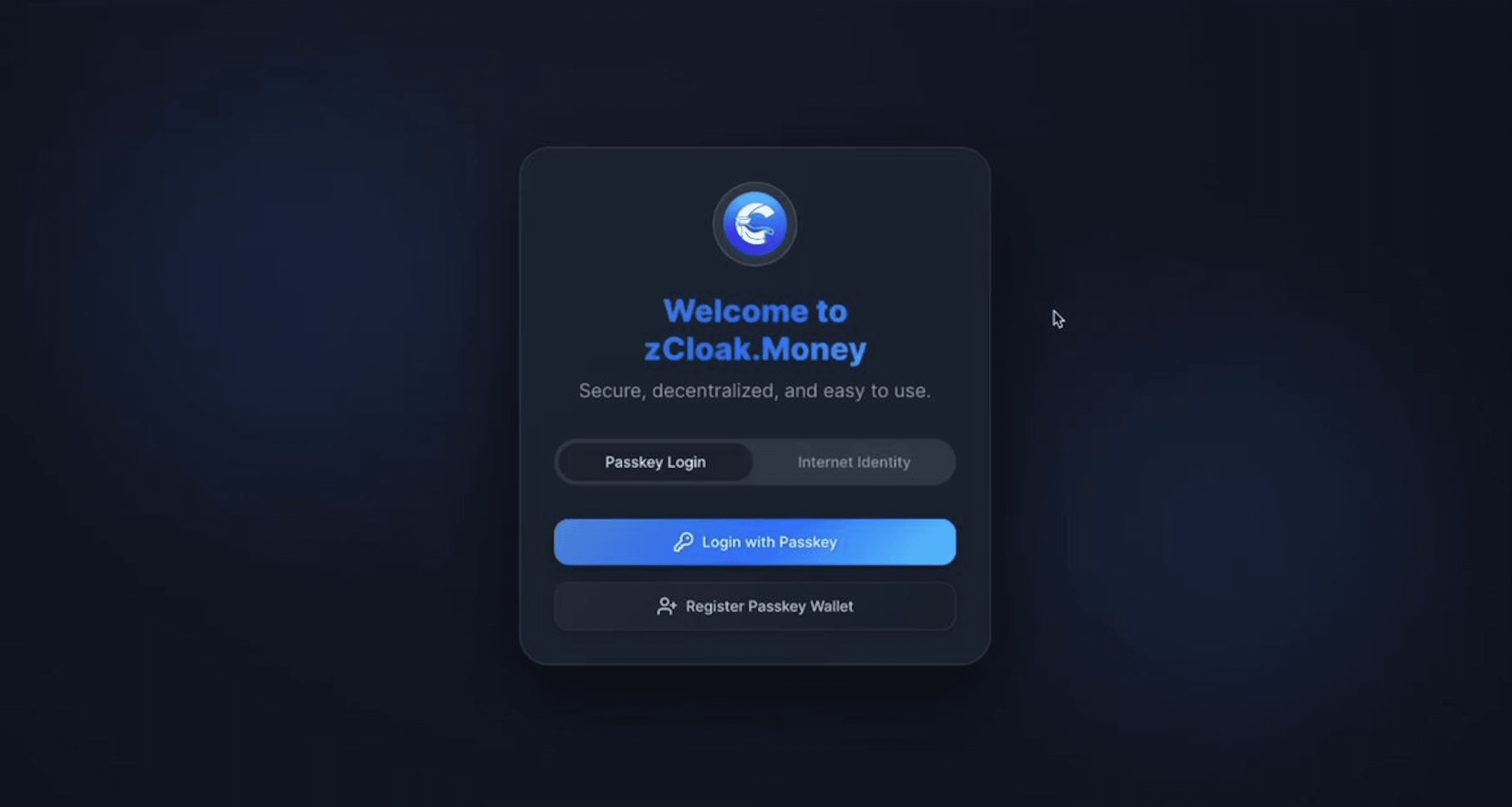
Fourth generation: Passkey wallet (2024 to present)
The fourth-generation wallet takes a fundamental architectural turn. Instead of hiding or splitting the key, it seals the key in a secure chip in your device – the same hardware that protects Apple Pay and Google Pay. The key exists, but it can never be retrieved, transferred, or stolen. It can only be used when the user's biometric authentication is passed.
No seed phrase, no hardware devices, no third parties.
Evolution Timeline
- 2009: The first Bitcoin wallets, storing keys locally.
- 2014: Ledger launched its first consumer-grade hardware wallet.
- 2018: MPC technology begins to be applied in institutions
- 2025: The first enterprise-grade Passkey wallet (zCloak.Money) launches.
- 2025-2027: Mass migration to Passkey wallets begins
Each generation of wallets addresses the key shortcomings of its predecessor, but also introduces new problems. Users are always forced to choose between security and convenience, and Passkey Wallet is the first solution that can provide both at the same time.
III. Fatal Flaw – Weak Interface
There is a taboo fact in the industry: the first three generations of wallets all shared a fatal flaw unrelated to key storage .
Whether users are using software wallets, hardware wallets, or multi-party computation (MPC) solutions, they must access them through the Web2 infrastructure:
- The front-end/application is hosted on a centralized server (which may be hijacked).
- DNS may have been compromised (directing users to fake websites).
- Browser extensions may be replaced (with malicious versions).
- The web interface may be vulnerable to phishing attacks (a perfect copy can steal the user's key).
The $1.6 billion Safe (Wallet) attack definitively proved this point: if the interface used to access wallets can be compromised, then even the most secure key storage is meaningless.
The current problem in the industry is :
- First-generation software wallets: The seed phrase is encrypted with military-grade technology, but accessed through a browser plugin or app that is automatically updated/distributed by a centralized server.
- Second-generation hardware wallets: Your keys are stored in secure hardware that cannot be cracked, but managed by desktop software downloaded from a website that may be compromised.
- Third-generation multi-party secure computation (MPC) wallets distribute keys using advanced encryption to multiple participants, but the keys are controlled by a web portal provided by traditional infrastructure. This is like having an impregnable vault but a cardboard door. Every generation of wallets has been obsessed with protecting the keys, neglecting the user interface. Hackers are clever; while security teams are busy creating more sophisticated locks, attackers simply replace the door. This is the pain point that fourth-generation wallets address – they protect both the keys and the user interface simultaneously.
IV. Analysis of Wallet Attack Patterns
To understand why Passkey wallets are revolutionary, it's essential to understand how crypto assets are stolen. These attacks, which exploit specific architectural weaknesses, can be broadly categorized into four types.
Front-end/Interface Attacks
The most destructive attacks don't target the blockchain or wallet – they target the interface. DNS hijacking redirects users to fake sites that look exactly the same. The Safe (Wallet) attack mentioned above works in this way: attackers compromise the network front-end and inject malicious code, and when users sign what they believe to be legitimate transactions, their wallets are emptied.
Browser plug-in attacks are equally insidious. They can compromise developer accounts and push malicious updates, or trick users into downloading hacker scripts that replace secure extensions with malicious variants. Users trust the familiar interface but are unaware that every transaction they sign is sending their assets to attackers.
Seed Seed phrase Theft
The 12 or 24 words protecting billions of dollars in crypto assets are actually very vulnerable, and attacks can take many forms:
- Physical theft : Taking pictures of or stealing written seed phrase.
- Digital theft : Tongyi software scans and identifies specific patterns in seed phrase.
- Social verification : Impersonating customer service or technical support to trick users into "verifying" their seed phrase.
- Forged seed phrase generator : Generates pre-determined, vulnerable seed phrase.
Once a seed phrase is leaked, it means a complete and permanent loss that cannot be recovered, arbitrated, or revoked.
Phishing Operations
Crypto phishing has evolved into an industrialized fraud system, with common tactics including:
- Approval phishing : tricking users into granting unlimited token permissions.
- Fake airdrops : Create a sense of urgency to lull users into a false sense of security.
- Website Cloning : A 1:1 replica of the interface of a popular DeFi website, stealing users' credentials and seed phrase.
In the online world, perfect imitation is actually incredibly cheap, and even experts can be fooled.
Supply chain contamination
Modern software systems are interdependent, which means countless attack opportunities. A leaked npm package (JavaScript dependency library) may affect thousands of wallets, hardware wallet firmware updates may introduce backdoors, and multiple layers of dependencies may hide malicious code that only starts months after installation.
The Ledger Connect Kit attack is a prime example: a corrupted library simultaneously affected multiple DeFi applications, resulting in the emptying of wallets across the entire ecosystem.

V. Passkey Wallet Makes its Debut
What is a Passkey?
Passkey is not some new encryption technology; it is a future digital security authentication system that Apple, Google, and Microsoft have invested billions of dollars in. When users use Face ID to unlock their iPhones, Touch ID to log in to GitHub, or Windows Hello to access the system, they are already using Passkey.
Today, the world's leading technology and financial giants have adopted this system. Binance, Coinbase, and PayPal use Passkey to protect millions of accounts, and Amazon, Google, and Microsoft have made it a security standard. This technology, based on the WebAuthn/FIDO2 standard, has been tested in real-world scenarios by billions of users.
The new breakthrough lies in the fact that this mature technology will be applied to crypto wallets.
How Passkey reshapes the security model :
- Biometric authentication : The user's face or fingerprint becomes the only access method.
- Domain binding security : Each Passkey is bound to a specific domain, making phishing mathematically impossible.
- No shared secret : Unlike passwords or seed phrase, Passkey never leaves the user's device.
- Hardware support : The key resides in the device's secure enclave, the same one that protects payment credentials.
When Apple made Passkey the standard in iOS 16, they weren't just improving passwords – they were completely eliminating them, and the same revolution is sweeping through the cryptocurrency space.
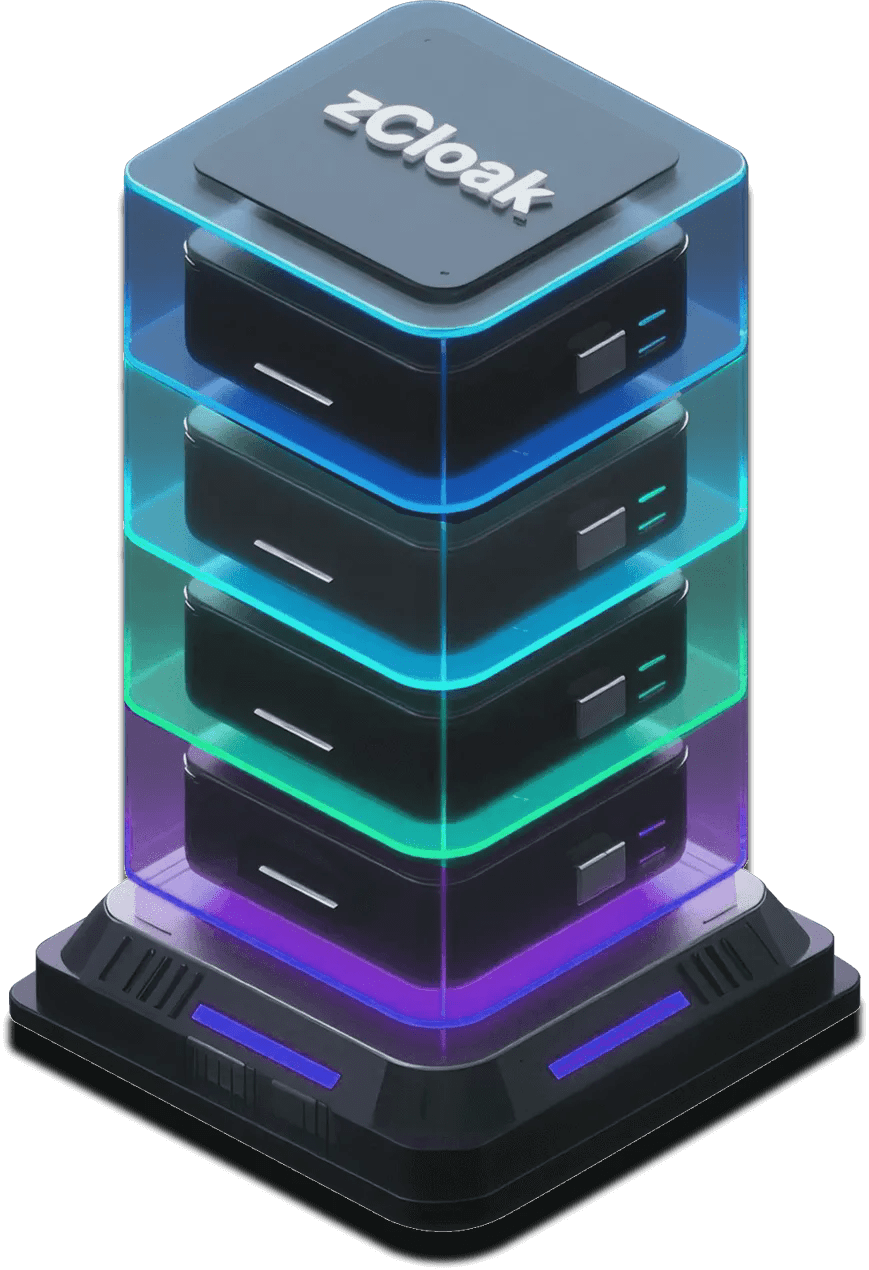
The Complete Architecture
The implementation of a modern Passkey wallet combines three key layers that work together to create unprecedented security.
Layer 1: Passkey in the security chip
The private key is generated within the device's secure chip and exists permanently. It is not stored in software and cannot even be accessed by the user. Its sole function is to sign transactions when the user verifies their identity.
Layer 2: Immutable Frontend
The Passkey wallet interface is no longer provided by a traditional web server, but the entire front end is deployed on the blockchain. This front end is immutable and irreplaceable – as permanent as the blockchain itself.
Layer 3: Direct Blockchain Execution
Transactions flow directly from the certified device to the blockchain, without intermediary servers, API keys, or centralized infrastructure that could be attacked.
Practical Applications
Currently, some teams are exploring Passkey wallets, but zCloak.Money has already implemented a complete architecture:
- Passkey for identity verification
- ICP building chain frontend
- Chain-key Cryptography enables multi-chain support
This system has been launched and is in practical use.
The crucial, unalterable front end
The ingenious combination of Passkey and an immutable front-end solves the problems at both ends of the security system. Traditional wallets, even with the most secure keys, can still crash completely if the access interface is hijacked. Passkey wallets using traditional network front-ends are still vulnerable to DNS hijacking or server intrusion.
However, since the front end itself resides on the blockchain – immutable, verifiable, and permanent – there is nothing that can be hijacked, and the wallet that the user sees and operates is itself part of the protocol.
This technological convergence has created an unprecedented achievement: an unhackable wallet, not through stronger defenses, but by completely eliminating entry points for attacks.
VI. Immune-level architecture innovation
Passkey wallets are more than just attack-resistant – they make most attacks logically impossible. Security isn't achieved by building walls, but by architectural immunity.
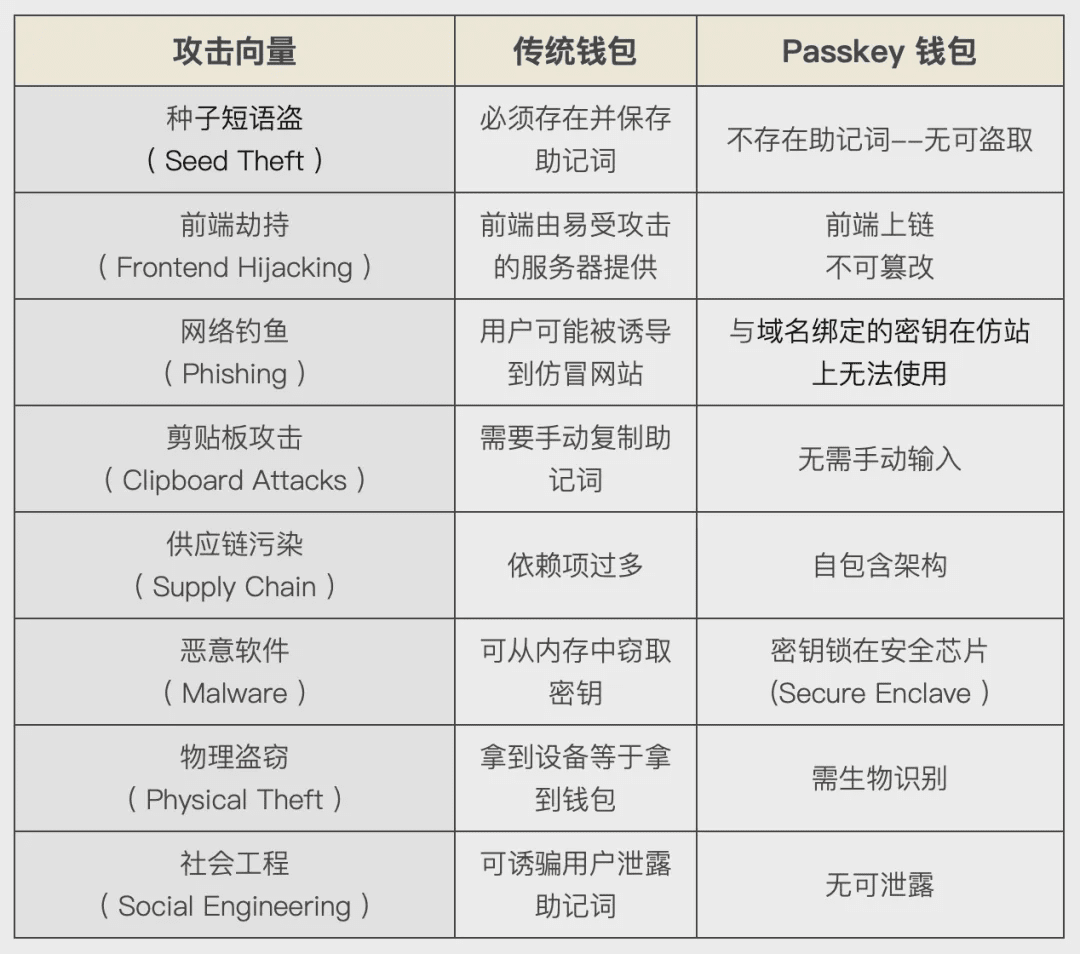 Immune Matrix
Immune MatrixTechnical Principles
This immunity stems from fundamental architectural differences:
- The passkey cannot be extracted or copied . The private key is generated and permanently bound in the secure chip. There is no function to extract it, no API to read it, and it cannot be accessed even with root access to the device.
- Biometric authentication is performed locally , and facial or fingerprint data never leaves the user's device. The security chip verifies the user's biometrics and allows key signing only after pairing, independent of network requests, external authentication, and attack surfaces.
- Domain binding prevents redirection . Each Passkey is encrypted and bound to a specific domain, so even if an attacker creates a perfect copy of the website, the Passkey simply cannot function there, making the attack physically impossible.
- The immutable front end cannot be hijacked . When the wallet interface exists as a blockchain protocol rather than a traditional network hosting, there are no servers to attack, no DNS to hijack, and no CDN to pollute. This interface is as immutable as the blockchain itself.
VII. Tesla Moment
Just as Tesla didn't build a better internal combustion engine but instead eliminated the need for gasoline, Passkey wallets no longer require seed phrase.
Model Disruption
The pattern of technological revolutions is traceable. At first, it was ignored ("Since horses run so well, why do we need cars?"), then it was considered out of touch with reality ("Where do we charge electric cars?"), and finally, it became the new standard for disruptive forces ("You still use gasoline? That's so primitive!").
We are at a turning point, with Passkey wallets shifting from innovative technology to necessities.
Application Outlook
Currently, early adopters – crypto-native enterprises and visionary institutional vaults – are migrating to Passkey wallets to gain a competitive edge through superior security and operability.
- 1-2 years later : Enterprises began to adopt Passkey wallets on a large scale, as major hacking attacks continued to hit traditional wallets, insurance companies began to require the use of Passkey wallets as a condition of coverage, and boards of directors began to question why their vaults were not using the "most secure wallet".
- 3 to 5 years later : mainstream adoption, using seed phrase becomes a dangerous signal, just like using passwords without two-factor authentication (2FA), new users completely skip seed phrase and use Passkey directly.
- The future : Seed phrase will disappear, just like dial-up modems or floppy disks. The idea that we used to protect billions of dollars with 24 words written on paper will be as absurd as hiding money under a mattress.
Straightforward truth
Every technological revolution follows this pattern: resistance, adoption, dominance. From telegraph to telephone, from film to digital, from internal combustion engine to tram. Superior technology does not prevail through incremental improvements, but rather by rendering previous technologies obsolete.
Passkey wallets are not just a step in the same direction; they represent an evolution in digital asset security models.

Conclusion: The Time to Make a Choice
The solution is in sight.
After losing $50 billion, the crypto industry is at a crossroads, either continuing to iterate on the same vulnerable architecture—putting a stronger lock on a cardboard door—or embracing a shift in the way we think about wallet security.
The Passkey wallet represents this shift, not through localized optimizations, but through a radical architectural change.
Tech giants have proven that Passkey is the future of identity verification, with the first encrypted implementation, zcloak.money, already online, demonstrating that security and convenience are not mutually exclusive.
Technological change follows a predictable pattern; what seems revolutionary today may become standard tomorrow. The question is not whether Passkey wallet will become the norm, but when.
The Tesla moment for crypto wallets has arrived.
The only question is: Are you ready?