Upon discovering security vulnerabilities in intelligent agents such as "Lobster," or security threats and attacks targeting such agents, reports can be submitted to the Ministry of Industry and Information Technology's Cybersecurity Threat and Vulnerability Information Sharing Platform immediately. The platform will promptly organize handling in accordance with the "Regulations on the Management of Security Vulnerabilities in Network Products."
Article author and source: CCTV News
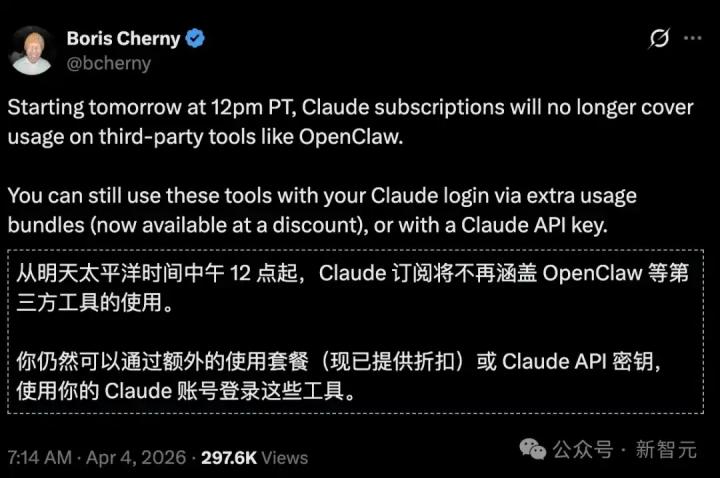
Recently, the open-source AI agent OpenClaw (commonly known as "Lobster") has become extremely popular. Experts from the China Academy of Information and Communications Technology (CAICT) reiterated today (the 10th) that although the "Lobster" agent has been updated to the latest version and can fix known security vulnerabilities, this does not mean that security risks have been completely eliminated. Previously, the Ministry of Industry and Information Technology's Cybersecurity Threat and Vulnerability Information Sharing Platform had already issued relevant security risk warnings.
OpenClaw, an open-source AI agent tool, is nicknamed "Lobster" because its icon is a red lobster. It integrates communication software and a large language model to autonomously perform complex tasks such as file management, email sending and receiving, and data processing on the user's computer.
"Lobster" cybersecurity features include autonomous decision-making and the ability to utilize system resources. Coupled with blurred trust boundaries and a lack of rigorous vetting in the skill package market, these technologies pose significant risks. Cybersecurity is dynamic and constantly evolving, and hacker attack methods are continuously iterating. "Patching" and "upgrading" cannot be considered a "one-size-fits-all" security guarantee.
Experts urge government agencies, enterprises, public institutions, and individual users to use "Lobster" and other intelligent agents with caution. Upon discovering security vulnerabilities in "Lobster" or other intelligent agents, or upon encountering security threats or attacks against them, they should immediately report to the Ministry of Industry and Information Technology's Cybersecurity Threat and Vulnerability Information Sharing Platform. The platform will promptly organize handling in accordance with the "Regulations on the Management of Network Product Security Vulnerabilities."
In addition to timely upgrades and updates, the secure use of any network product must adhere to the principles of "least privilege, proactive defense, and continuous auditing." Experts recommend the following aspects for the secure use of the "Lobster" intelligent agent:
- Use the latest official version. When deploying, prioritize downloading the latest stable version from official channels and enable automatic update reminders. Back up your data before upgrading, and restart the service after upgrading to verify that the patches are effective. Never use third-party images or older versions.
- Strictly control internet exposure. Never expose "Lobster" agent instances to the public internet, and restrict access source addresses by using strong passwords or authentication methods such as certificates or hardware keys.
- Adhere to the principle of least privilege. During deployment, it is strictly forbidden to use accounts with administrator privileges. Only grant the minimum permissions necessary to complete the task. For important operations such as deleting files, sending data, and modifying system configurations, secondary confirmation or manual approval is required.
- Use the skill marketplace with caution. ClawHub is a community platform that provides skill packs for "Lobster" AI users. These skill packs may contain malicious software. We recommend downloading with caution and reviewing the skill pack code before installation. Reject any skill packs that ask you to "download a zip file," "execute a shell script," or "enter a password."
- Protect yourself from social engineering attacks and browser hijacking. Avoid browsing websites from unknown sources and clicking on unfamiliar web links. It is recommended to use website filters and other extensions to block suspicious scripts, enable OpenClaw rate limiting and log auditing, and immediately disconnect from the gateway and reset your password if you encounter suspicious activity.
- Establish a long-term protection mechanism. Enable detailed log auditing to regularly check for and patch vulnerabilities. Government agencies, enterprises, and individual users can combine this with real-time protection using cybersecurity tools and mainstream antivirus software. Regularly monitor risk warnings from OpenClaw official security bulletins and vulnerability databases such as the Ministry of Industry and Information Technology's cybersecurity threat and vulnerability information sharing platform, and promptly address any potential security risks.
Users must thoroughly understand and implement the safety configuration specifications when using AI intelligent agents such as "Lobster" and develop safe usage habits.