There is no "undo" button in the crypto world; once funds are sent to the wrong address, the chances of recovery are extremely slim.
Written by: etherscan.eth
Compiled by: AididiaoJP, Foresight News
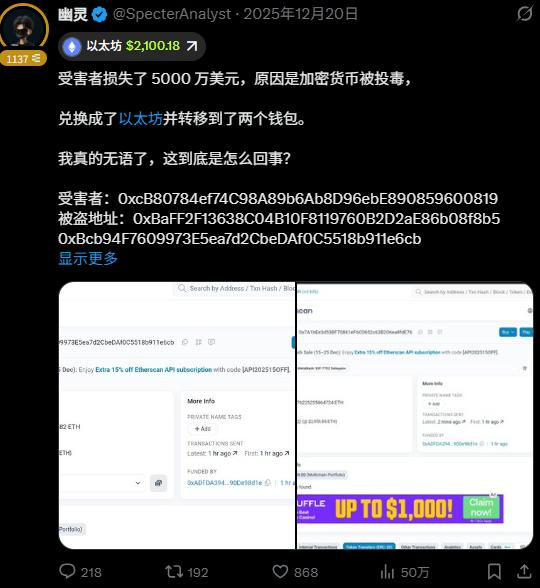
A few weeks ago, an Etherscan user named Nima shared an unpleasant experience. After completing only two stablecoin transfers, he received more than 89 emails alerting him about address monitoring within a short period of time.

As Nima points out, these alerts are triggered by address poisoning transactions. The attackers create these transactions with the sole purpose of implanting highly similar fake addresses into the user's transaction history, intending to trick the user into mistakenly copying and using these fake addresses in their next transaction.
Address poisoning has existed on Ethereum for several years. However, this incident highlights how automated and large-scale such attacks have become. What used to be sporadic spam can now be carried out on a massive scale, with attackers typically able to implant poisoned transfers within minutes of a legitimate transaction.
To understand why such attacks have become more prevalent today, we need to analyze them from two dimensions: the evolution of address poisoning attack methods and the fundamental reasons why they can be easily scaled up.
In addition, this article will focus on a core prevention principle to help users effectively defend against such attacks.
I. The Industrialization of Geographic Poisoning
Address poisoning was once considered a niche fraud tactic employed by opportunistic attackers. However, its operational model has increasingly become industrialized.
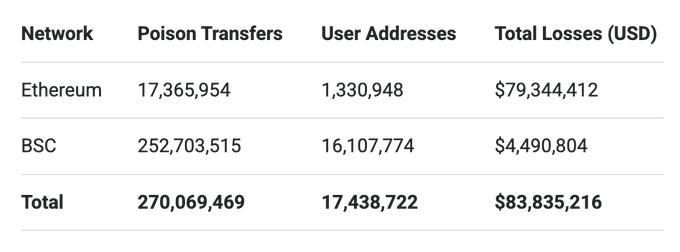
A study published in 2025 analyzed address poisoning activities between July 2022 and June 2024 (before the Fusaka upgrade). The study showed that approximately 17 million poisoning attempts occurred on Ethereum, involving approximately 1.3 million users, with confirmed losses of at least $79.3 million.
The table below, based on the results of the "Blockchain Address Poisoning Study," shows the scale of address poisoning activities on Ethereum and BSC from July 2022 to June 2024. The data indicates that poisoned transfers occurred 1355% more frequently on the BSC chain, where transaction fees are significantly lower.
Attackers typically identify potential targets by monitoring blockchain activity. Once a target user's transaction is detected, an automated system generates highly similar addresses with the same first and last characters as legitimate addresses that have interacted with that user. The attacker then sends poisoned transfers containing these fake addresses to the target address, causing it to appear in the user's transaction history.
Attackers tend to target addresses with higher potential for profit. Addresses that frequently make transfers, hold large amounts of tokens, or participate in large transactions are typically more likely to receive poisoning attempts.
Competition mechanism improves attack efficiency
A 2025 study revealed a concerning phenomenon: different attack groups often compete with each other. In many poisoning campaigns, multiple attackers send poisoned transfers to the same target address almost simultaneously.
Each attack group attempted to be the first to implant their fake addresses into users' transaction history, hoping that their fake addresses would be prioritized when users copied addresses later. The group that successfully implanted their fake addresses first had a higher probability of their addresses being mistakenly copied by users.
The following case vividly illustrates the intensity of this competition. In this case, within minutes of a legitimate USDT transfer, 13 poisoned transactions were implanted.
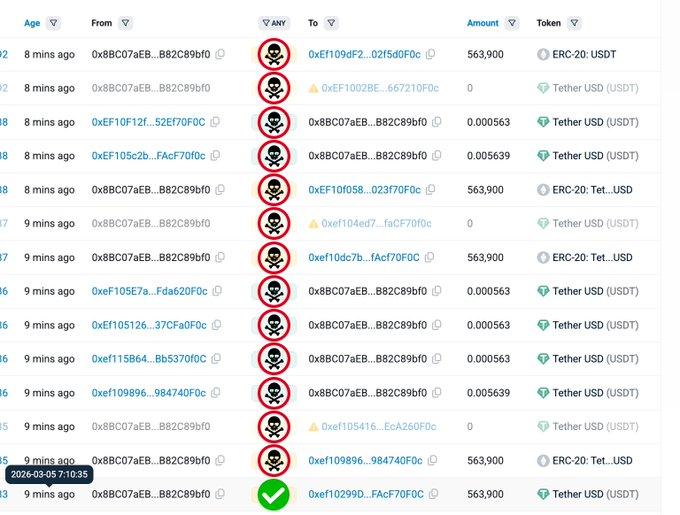
Note: Etherscan hides zero-value transfers by default; this has been removed for demonstration purposes.
Common techniques used in address poisoning attacks include dust transfers, counterfeit token transfers, and zero-value token transfers.
II. Reasons why address poisoning attacks are easy to scale up
At first glance, the success rate of address poisoning seems low. After all, most users won't fall for it. However, from an economic perspective, the logic behind this type of attack is quite different.
The logic of probability games
Researchers have found that the success rate of a single poisoning attempt on Ethereum is approximately 0.01%. In other words, on average, only about 1 in 10,000 poisoning transfers could result in a user mistakenly sending funds to an attacker.
Therefore, poisoning attacks are no longer limited to a few addresses, but tend to send thousands or even millions of poisoned transfers. When the number of attempts is large enough, even a small success rate can accumulate to generate considerable illicit profits.
A single successful large-scale money transfer fraud can easily cover the costs of thousands of failed attempts.
Lower transaction costs spurred an increase in poisoning attempts.

The Fusaka upgrade, activated on December 3, 2025, introduced scalability optimizations that effectively reduced transaction costs on Ethereum. This change benefits both ordinary users and developers, while also significantly reducing the cost for attackers to initiate a single poisoning transfer, enabling them to send poisoning attempts on an unprecedented scale.
Following the Fusaka upgrade, Ethereum network activity significantly increased. In the 90 days after the upgrade, the average daily transaction volume increased by 30% compared to the 90 days prior to the upgrade. During the same period, the average daily increase in newly created addresses was approximately 78%.
Furthermore, we observed a significant increase in dust transfer activity. In these transfers, attackers send transactions with the same tokens as the user's historical transfers, but in extremely small amounts.
The following data compares dust transfer activity for several major assets within 90 days before and after the Fusaka upgrade. For stablecoins such as USDT, USDC, and DAI, dust transfers refer to transactions with a value of less than $0.01; for ETH, it refers to transactions with a transfer amount of less than 0.00001 ETH.
USDT
- Before upgrade: 4.2 million times
- After upgrade: 29.9 million times
- Increase: +25.7 million times (+612%)
USDC
- Before upgrade: 2.6 million times
- After upgrade: 14.9 million times
- Increase: +12.3 million times (+473%)
DAI
- Before upgrade: 142,405 times
- After upgrade: 811,029 times
- Increase: +668,624 times (+470%)
ETH
- Before upgrade: 104.5 million times
- After upgrade: 169.7 million times
- Increase: +65.2 million times (+62%)
Data shows that shortly after the Fusaka upgrade, dust transfer activity (below $0.01) surged, peaked, and although it declined somewhat, it remained significantly higher than pre-upgrade levels. In contrast, transfer activity above $0.01 remained relatively stable during the same period.
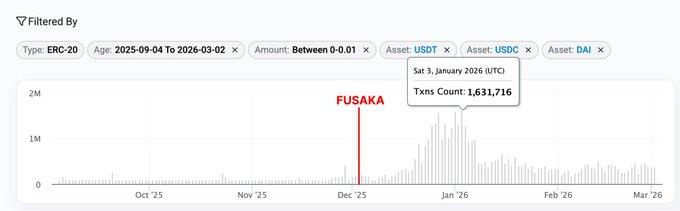
Chart: Comparison of USDT, USDC, and DAI dust transfer trends (<0.01 USD) within 90 days before and after the Fusaka upgrade. (Source)

Chart: Comparison of USDT, USDC, and DAI regular transfers (>0.01 USD) trends within 90 days before and after the Fusaka upgrade. (Source)
In many attack campaigns, attackers first distribute tokens and ETH in bulk to newly generated fake addresses, which then send dust transfers one by one to the target address. Because dust transfers involve extremely small amounts, attackers can conduct large-scale operations at very low cost as transaction costs decrease.
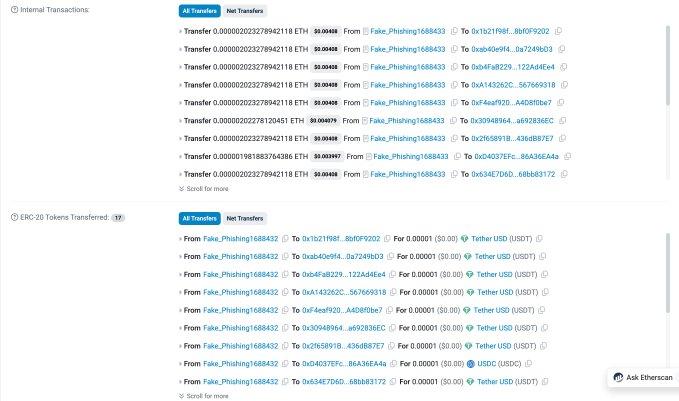
Illustration: Address Fake_Phishing1688433 sent tokens and ETH in bulk to multiple different fake addresses in a single transaction. (Source)
It's important to clarify that not all dust transfers are poisoning attempts. Dust transfers can also originate from legitimate activities, such as token swaps or small interactions between addresses. However, after reviewing a large number of dust transfer records, it can be determined that a significant portion of them are highly likely poisoning attempts.
III. Core Prevention Principles
Always carefully verify the target address before sending any funds.
Here are some practical tips for reducing risk when using Etherscan:
Use recognizable address identifiers
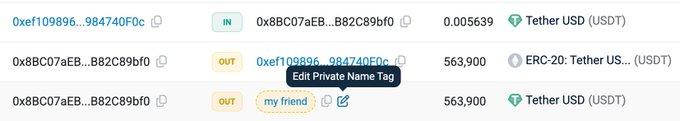
Set private name tags on Etherscan for addresses you frequently interact with. This helps make legitimate addresses easily distinguishable from many similar addresses.
Using domain name services such as ENS can also improve the visibility of the address in the browser.
At the same time, it is recommended to use the wallet's address book function to add frequently used addresses to the whitelist to ensure that funds are always sent to the intended destination.
Enable address highlighting
Etherscan's address highlighting feature helps users visually distinguish between addresses that look similar. If two addresses look almost identical but are highlighted differently, one of them is very likely the address used for poisoning.
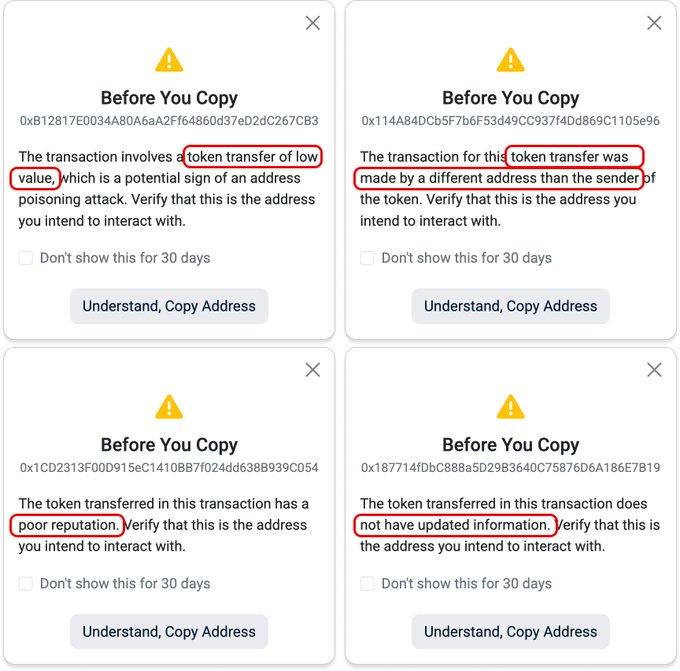
Double-check before copying the address.
Etherscan will proactively pop up a warning window when a user copies an address that may be associated with suspicious activity. This suspicious activity includes:
- Low-value token transfers
- Fake token transfer
- Tokens with a poor reputation
- Tokens with outdated information
When you see this kind of reminder, please be sure to pause your operation and carefully verify whether the address you copied is the target address you actually intend to interact with.
Remember, there is no "undo" button in the crypto world. Once funds are sent to the wrong address, the chances of recovery are extremely slim.
Summarize
As transaction costs decrease, making high-volume attack strategies more economical, address poisoning attacks are becoming increasingly rampant on Ethereum. These attacks also negatively impact user experience, with large amounts of poisoned spam messages flooding various user-facing transaction history interfaces.
Effectively preventing address poisoning attacks requires not only increased user security awareness but also improved interface design. For users, the most crucial habit to cultivate is to carefully verify the target address before sending funds.
At the same time, relevant tools and user interfaces should play a more important role in helping users quickly identify suspicious activities.
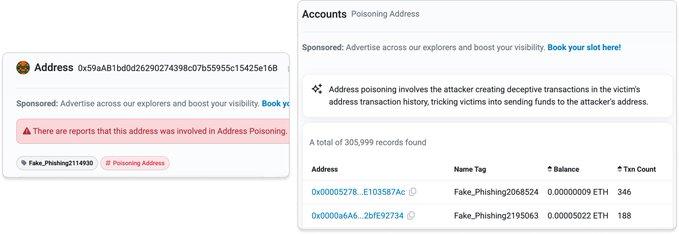
Poisoning address label on Etherscan (https://etherscan.io/accounts/label/poisoning-address)
Etherscan is continuously improving its browser interface and API services to help users more easily identify such attacks. We proactively flag spoofed addresses, identify and hide zero-value token transfers, and label counterfeit tokens. By providing this curated data, users can more easily discover potential address poisoning attempts without manually sifting through massive amounts of transaction records.
As poisoning attacks become increasingly sophisticated with the aid of automation and high-volume dust transfers, clearly identifying these risk signals is crucial to helping users distinguish between suspicious activity and legitimate transactions.







