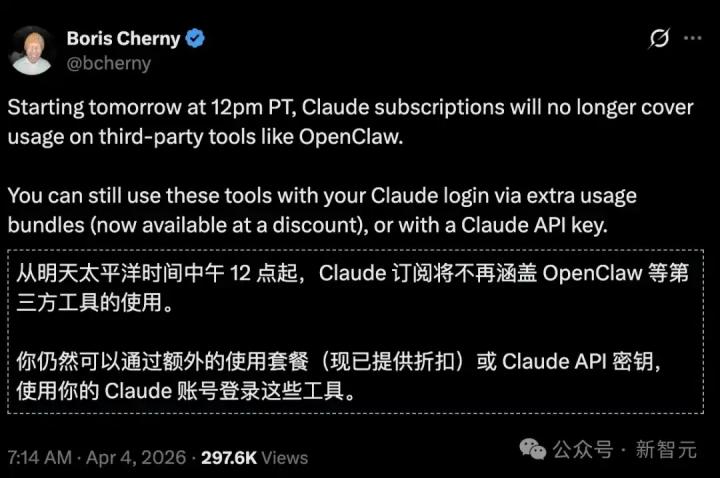
Now that AI agents are taking over more and more workflows, a problem that many people have overlooked has come to the forefront: when AI has the ability to operate computers, access APIs, and even execute transactions, how can we ensure that it is not used maliciously?
In our practical work at WEEX Labs, we focus not only on the "intelligence" of AI, but also on its "immunity." Based on our relentless pursuit of asset and information security, we have summarized three ironclad rules of security that must be followed when building multi-agent systems.
Ironclad Rule 1: Physical and Logical Isolation – Rejecting “Naked” AI
Many developers, for convenience, run AI agent scripts directly on their personal work computers or private servers. WEEX Labs believes this is tantamount to leaving a backdoor for hackers.
• Standalone environment operation: All OpenClaw instances must be deployed in a standalone, controlled cloud virtual environment (VM).
• Refuse to use personal devices: It is strictly forbidden to grant permissions to the AI using personal devices or the main account. This is because if a third-party API called by the AI agent is hijacked, hackers could steal your private data or identity token through the AI's local environment.
• Principle: Put AI in a “digital sandbox” and let it shine in a restricted environment.

Rule Two: The Principle of Minimum Authority – It's an "intern," not a "CEO."
When assigning permissions to AI agents, the principle of least privilege must be followed.
• Access to private keys is strictly prohibited: Under WEEX's security guidelines, AI agents can perform market monitoring, public opinion analysis, and copywriting, but are absolutely prohibited from touching any sensitive operations involving core assets, seed phrase, or private keys.
• API Scope Control: If the AI needs to call the API, only allow read-only or limited access. Even if the AI logic malfunctions, the potential losses will be limited to a very small extent.
• Principle: Never hand over the "vault key" to an intelligent agent that is still learning and evolving.

Rule Three: Set a "Safety Brake": Use rules to lock in potential anomalies.
AI has a strong ability to self-correct logically, but it may also get stuck in a strange "loop instruction".
• Monitoring and Braking: As mentioned in the cost control section, WEEX Labs has set a maximum retry threshold (e.g., shutdown after 3 failures) . This is not only to save money, but also to prevent the AI from making catastrophic, high-frequency erroneous operations when attacked or vulnerable.
• Budget warning prompt: We have embedded security defense instructions in the underlying Prompt, requiring AI to immediately issue an alert to human administrators when it detects abnormal instruction requests or unauthorized attempts.
• Principle: Humans must retain the ultimate authority to "shut down with one click".
In the deep waters where Web3 and AI converge, security is not an option, but a prerequisite for survival. WEEX Labs firmly believes that only automation built on a robust security foundation can truly revolutionize productivity. We will continue to optimize this "Security-First" AI collaboration architecture, exploring a more robust path to innovation for users and industries.