Introduction: When the "all-around assistant" becomes the "secret agent mole"
In 2026, when AI agents were all the rage, OpenClaw (formerly known as Clawdbot) became the first choice for many developers and enterprises to build customized AI assistants, thanks to its powerful cross-channel communication and private deployment capabilities.
However, the price of convenience is often invisible. WEEX Labs' security team recently observed that OpenClaw is experiencing an unprecedented "security aftershock." When an AI agent with the highest system execution privileges is "running naked" on the public internet, it is no longer your assistant, but rather the sharpest breaching tool in the hands of hackers.

Horrifying data: 258 vulnerabilities and 82 "surprise attacks"
Open source does not equate to absolute security transparency. According to CNNVD's report and WEEX Labs' field tests, OpenClaw's security defenses are completely collapsing.
• Vulnerability outbreak period: To date, a total of 258 vulnerabilities have been disclosed in the past.
• The growth rate in 2026 was astonishing: 82 new vulnerabilities were added in the first quarter of this year alone, with new risks emerging every day on average.
• High-risk accounts for more than half: Among them, high-risk and super-risk vulnerabilities with a CVSS score of ≥7.0 account for as high as 40.2% .
This means that if you are still running a version prior to 2026.2.15, your system may be under surveillance by dozens of "backdoors" known to hackers but unknown to you.
The Tragedy of Architecture: Layers of Protection, Yet Each Layer Can Be Breached
Why are OpenClaw vulnerabilities so numerous? WEEX Labs' in-depth analysis of its architecture reveals that due to "blurred trust boundaries," almost all four layers of its architecture contain fatal flaws.
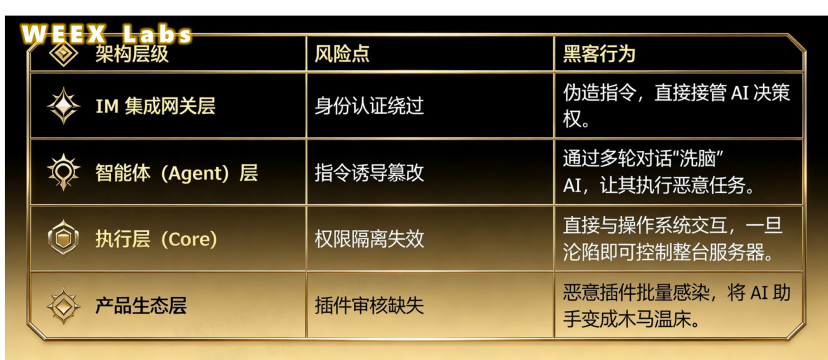
WEEX Labs' view: This "unprotected end-to-end" design logic, in the absence of security audits, turns the AI Agent into a "bomb" with its own consciousness.
The disappearing boundaries: 85% of "opening the door to thieves"
This is the most troublesome aspect for security professionals: the extremely irresponsible default configuration.
According to actual tests, OpenClaw is bound to the address 0.0.0.0:18789 by default, which means that as long as you deploy it, hackers from all over the world can try to access it.
• Public network exposure rate: up to 85% .
• Sensitive information in plaintext: API keys and chat history are not stored in encrypted form.
• High-risk skills are enabled by default: Powerful skills such as "code execution" and "file management" run without hindrance by default.
WEEX Labs Summary
The current state of OpenClaw is a microcosm of the current AI Agent ecosystem: in the pursuit of "intelligence" and "automation," security has been treated as a peripheral element that can be sacrificed.
However, in today's world where Web3 and AI are deeply integrated, permissions are assets. A compromised AI agent means that your private keys, data, and system control have all been handed over to another party.





