Not your keys, not your money
Author: day
Produced by: Vernacular Blockchain (ID: hellobtc)
Cover: Photo by GuerrillaBuzz Blockchain PR Agency on Unsplash
Recently, various wallet security incidents in the industry have emerged one after another:
On April 18th, a 5,000 ETH stolen tweet by MetaMask wallet developer @tayvano_ was widely spread in the encryption community, believing that MetaMask had loopholes, which caused panic in the community. On April 19th, MetaMask replied that it was stolen because of the vulnerability, but it is researching the source of the vulnerability.
On April 20, the imToken official reminded that fraudsters pretended to be imToken official personnel, contacted users by sending text messages, etc., and induced users to visit fake websites and enter mnemonic words, causing users to suffer asset losses. On April 21, SlowMist researchers said The sticky ad after Google search "imToken" is a new type of phishing website, please do not click on the link, and pay attention to avoiding risks.

On April 22, Trust Wallet issued an announcement that there was a loophole in the addresses for creating new wallets from November 14 to 23 last year, creating a compensation process for affected users.
With the outbreak of on-chain interaction needs such as DeFi and NFT, the industry is no longer what it was in the early days. As long as you buy coins on CEX and put them on CEX, you can meet the needs of most investors. Most investors will part or even all of them. Tokens are placed in their own wallets, which has also led to this industry becoming a hacker's paradise. From time to time, it will be reported that some investors download fake APPs due to authorization, leak private keys or leaks in the wallet itself, resulting in their own assets being stolen. , In the end, it turned out to be nothing, and ensuring the safety of self-owned assets has become an indispensable skill in the industry.
Next, we will fully understand how to protect the security of blockchain assets from several aspects such as wallet-related knowledge, stolen cases, and protection of private keys.
Wallet related knowledge

Before ensuring the safety of your own assets, you need to have a certain understanding of some basic knowledge about wallets in the industry in order to better understand how to protect your assets. Next, a few related concepts are briefly introduced.
1. Symmetric encryption and asymmetric encryption
Before understanding the public (private) key, let's briefly understand the symmetric encryption and asymmetric encryption in cryptography. Symmetric encryption means that A can obtain B through a certain algorithm, and conversely, B can reversely decrypt A through the same algorithm. Here, the same algorithm is used for encryption and decryption; asymmetric encryption means that A passes A certain algorithm can obtain B, but B cannot reversely decrypt B through the same algorithm, and the encryption and decryption here need to use different algorithms. 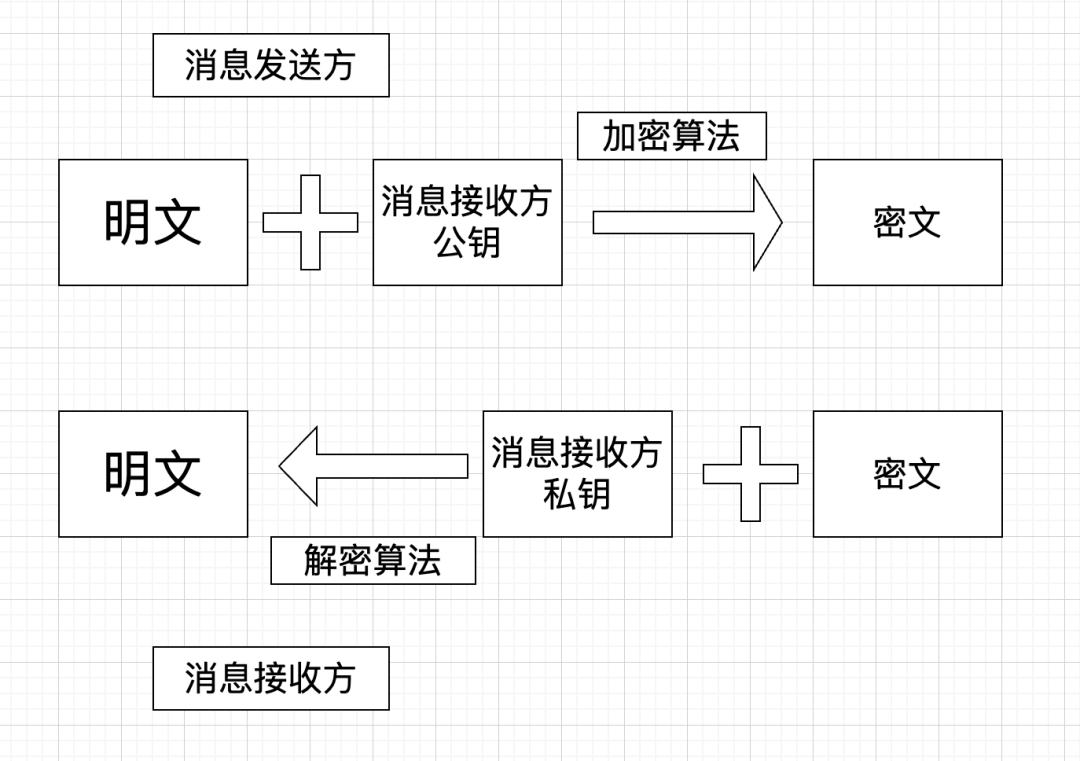
As shown in the figure, the difference between symmetric encryption and asymmetric encryption lies in whether the public key of the message receiver and the private key of the message receiver in the figure are the same key.
2. Public (private) key, mnemonic, address
After understanding symmetric encryption and asymmetric encryption, you can better understand some basic concepts related to wallets.
Key pair : In asymmetric encryption, there is a pair of key pairs, namely a public key and a private key. The public key is public and the private key is not.
Public key : used to encrypt data, data encrypted with the public key can only be decrypted with the private key.
Private key : The private key can generate a public key to decrypt data encrypted by the public key.
Address : Corresponding to the "public key", because the public key is too long, so there is an "address", and the address is generated by the public key.
Mnemonic : Corresponding to the "private key", because the private key is a randomly generated string, which is too long and difficult to remember, so a set of human-readable words was created instead of the private key to help users remember the private key , generally 12 irregular phrases. (private key = mnemonic)

Electronic signature : A certain message (you transfer 100 Ethereum to someone), this message needs to be signed by your private key and broadcast to the blockchain.
Signature verification : The receiving end can verify that the message is indeed signed by your private key through your public key, that is, you published it, and the transaction records are on the chain. Therefore, whoever has the private key has mastered the wallet.
Simply understand, the public key (address) is equivalent to your account, and the private key (mnemonic) is equivalent to your account + password (the private key can generate the public key).
Using a bank card as an analogy, public key = bank account, address = bank card number, password = bank card password, private key = bank card number + bank card password, mnemonic = private key = bank card number + bank card password, Keystore + password = For the private key, for the basic knowledge of the wallet, you can refer to the popular science article "If you want to keep assets safely, you must first know these knowledge about the wallet" before the vernacular.
3. Storage of private key (mnemonic phrase)
Your coin is not stored in your wallet APP, but in the address corresponding to the private key in the blockchain network. As long as you have the private key, you can log in to all wallets through the private key (the wallet supports you to have coin chain), the wallet is only used as the front end of the account fund display, and does not save your private key.
If the private key is lost, it means that your assets will also be lost and cannot be retrieved through the wallet. When registering the wallet for the first time, the wallet page will generally remind users to pay attention to this. This is completely different from the QQ and WeChat we used before. If the password is lost, it can also be verified through the mobile phone, and the question and friend verification can be retrieved. Of course, this is also the charm of blockchain decentralization. Your assets are completely Be your own.
4. Types of wallets
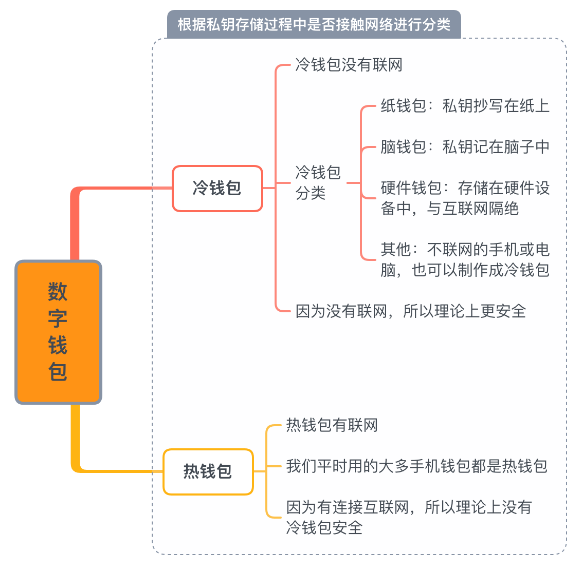
According to whether the private key is connected to the Internet, wallets can be divided into hot wallets and cold wallets, as shown in the figure above.
Hot wallet: client wallet, plug-in wallet, mobile APP.
Easy to use, easy to operate for novices, relatively high efficiency of transaction transfer, poor security, easy to be stolen.
Cold wallet: hardware wallet.
High security, suitable for storing large amounts of assets, complex creation, troublesome transfers, hardware damage or loss of private keys may cause loss of digital assets.
For a more detailed classification of wallets, please refer to the popular science article " Popular Science | What are the types of digital asset wallets? "
Through the above, we can know that the private key is everything, and all our measures to protect assets are actually to protect the private key, protect the private key, and protect the private key. (Prevent the loss of the private key and be obtained by others)
Theft case
After understanding the related concepts, let's take a look at the main lost cases at present. Through the cases, we can better protect our own wallets.
1. Leakage of private key (mnemonic phrase)
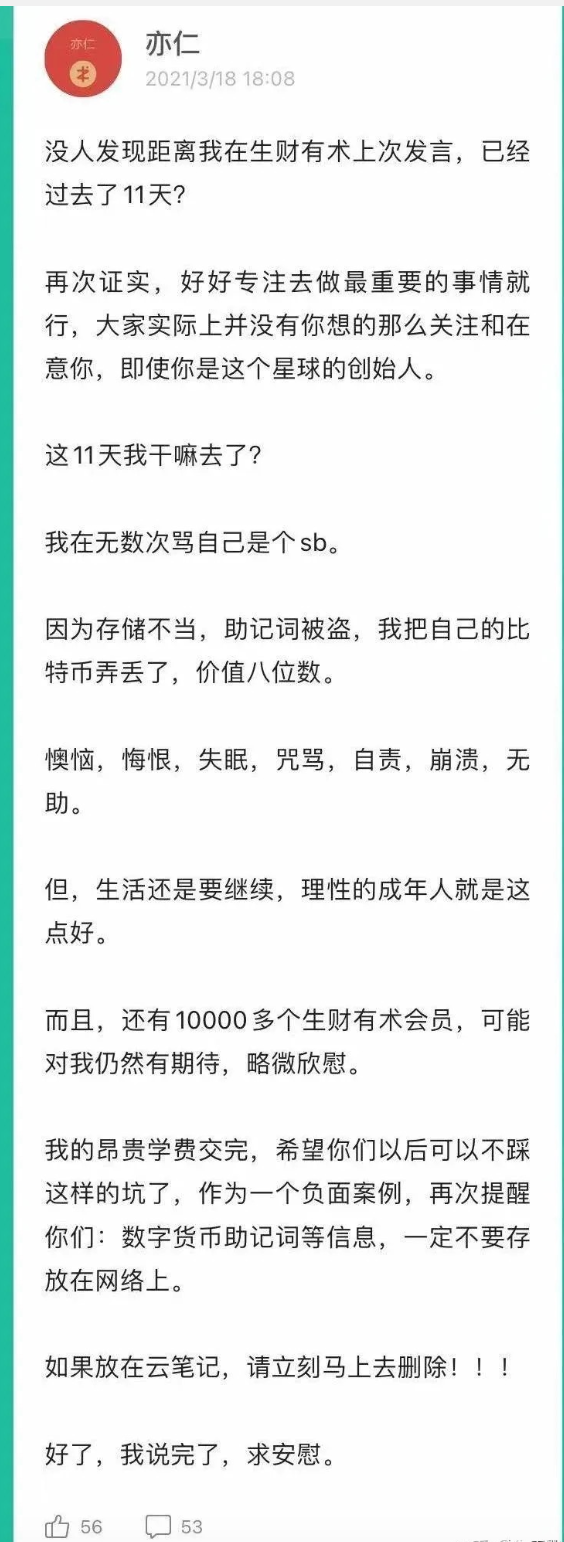
At the beginning of 2021, Yiren, the founder of Shengcaiyoushu, saved the Bitcoin private key in cloud notes, resulting in the loss of BTC with eight-figure assets.
In November 22, Shen Bo, the founder of Fenbushi Capital, had his digital assets worth US$42 million stolen. The stolen assets included: 38,233,180 USDC, 1607 ETH, 719,760 USDT and 4.13 BTC. According to the follow-up analysis of the security agency SlowMist, the theft was caused by the leakage of mnemonics.

2. The private key (mnemonic) is lost
British IT engineer James Howells lost his computer hard drive in 2013, which contained 8,000 bitcoins. Nine years later, he plans to spend $74.3 million rummaging through the junkyard to find the computer hard drive.
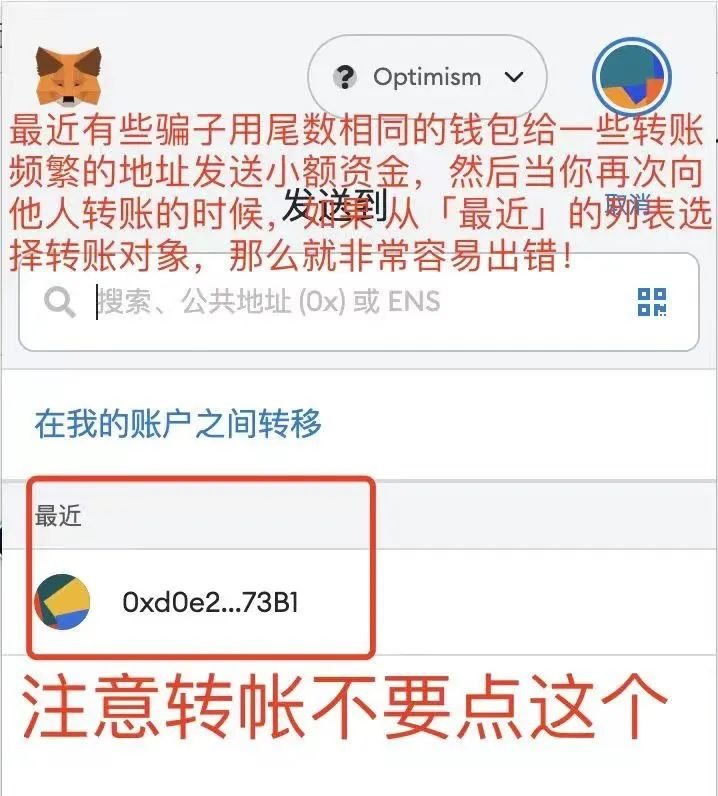
3. Click Viral Links
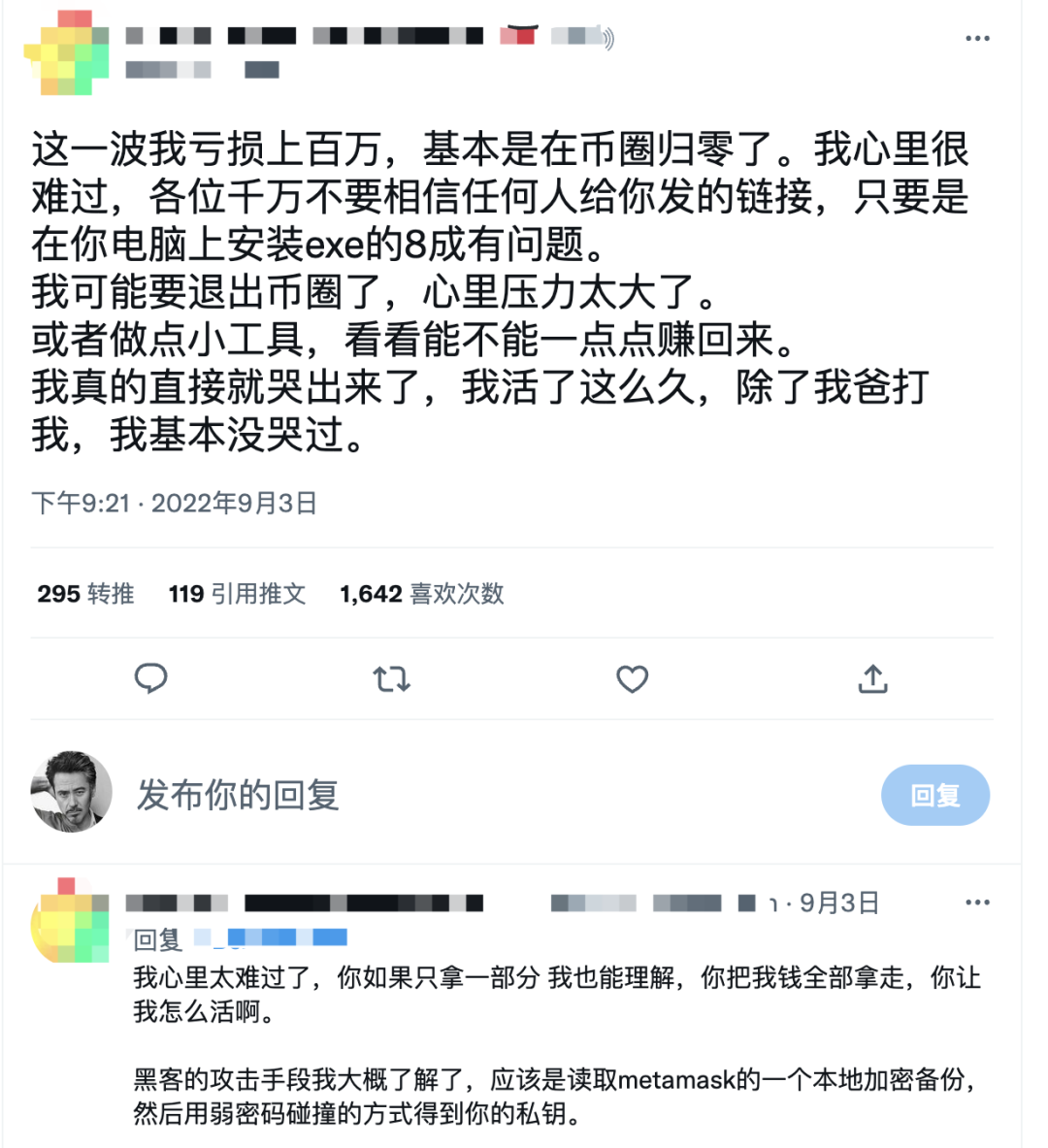
A user randomly clicked on the link sent by others, causing the hacker to read the local encrypted backup of metamask, and all assets were stolen.
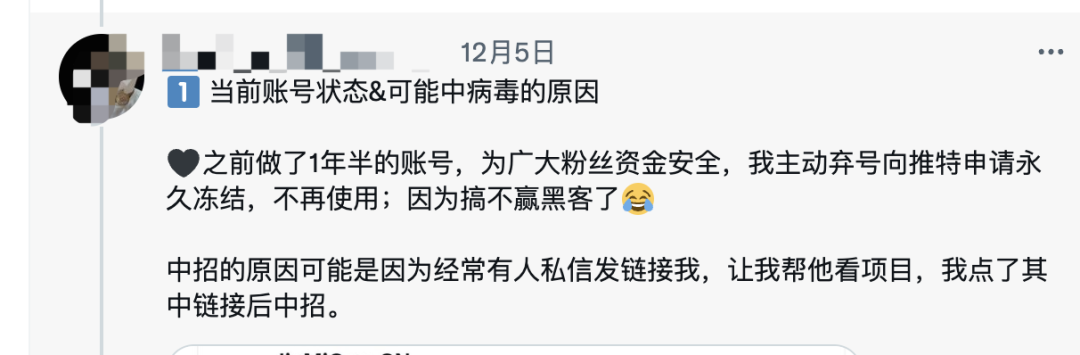
Twitter KOLs click on other people’s private links, resulting in the theft of Twitter accounts, and then release poisonous AirDrop information, using fans’ trust in KOLs to click on links to steal fan assets.
4. Random authorization, the application has loopholes
On October 2, Token Pocket's DEX Transit Swap officially stated that it was hacked and lost more than $15 million in assets, and reminded users to cancel the authorization.

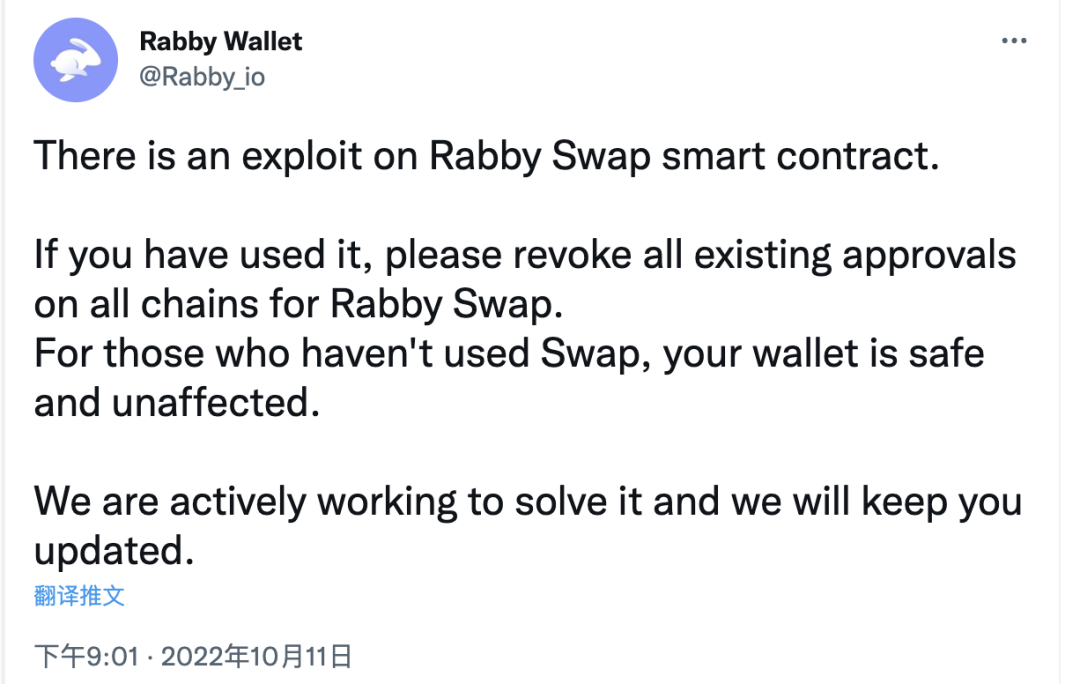
On October 11, Rabby, a plug-in wallet developed by the DeBank team, claimed that its Swap contract had a loophole, and suggested that users cancel the Rabby Swap authorization. In the end, the hacker made a profit of more than 190,000 US dollars.
5. Download fake APP (with virus software)
After some hackers obtain platform user information, they spread panic messages to users through text messages. The platform is no longer safe. They need to click on the link to reinstall the application or log in to the account. After logging in, the account funds are stolen.

A user downloaded a fake Binance app, and when transferring money, transferred it to someone else's address, and the assets of 5 ETH were completely lost.

We can see from the above cases that user assets are stolen, mainly in the following situations: leakage of private key (mnemonic), loss of private key (mnemonic), click on a virus link, arbitrary authorization, application loopholes, There are several situations such as downloading fake APP (virus software) .
Next, let's sort out what methods can avoid the above situation from happening.
How to Avoid Property Damage
1. Storage of the private key (core: not easy to lose, not easy to damage, other people cannot touch or use it)
Back up the wallet in time after it is generated, double backup, because once it is lost, it will not be retrieved
The mnemonic is stored on a medium that is not connected to the Internet and is not easy to be lost or damaged , such as copying it on paper and encrypting it by yourself (increase or decrease specific characters for easy memory); find a camera that will never be connected to the Internet for storage; there are some wallets Providers will sell iron plates related to mnemonics.
Use a cold wallet (hardware wallet), choose a well-known cold wallet ; buy from official channels, not through third-party channels (there may be viruses in third-party channels); set a strong password, and back up the private key at the same time to prevent the loss of the hardware wallet or damaged.
2. Prevent leakage of private key (mnemonic)
- Do not copy and paste the private key, some software can read the user's clipboard
- Do not save the private key in WeChat collection, transfer files, Baidu Cloud, Evernote and other network platforms
- Never tell anyone the private key. Remember, it is anyone. Some scammers pretend to be the wallet official to defraud your private key. Don’t believe it, the wallet party has no right to obtain the user’s private key
- Do not copy and paste private keys when using public Wi-Fi
- Download all kinds of apps, you should go to official channels, all app stores are sometimes untrustworthy (remember, all), there are fake apps
- Be cautious when signing wallets. Heavy users of DeFi protocols and NFT interactions should remember to revoke authorization in time to prevent theft of assets due to application loopholes
- Don’t click on the links (text messages) sent by others, download files shared by others, and don’t even click on the links of some KOLs, as they may contain viruses
- Once you find that there is a little asset leakage in the wallet, you should abandon the wallet as soon as possible, and don't take any chances
- Not using a free VPN
- Stay on top of the news and stay abreast of new stolen information in real time
All the above measures are actually to protect your private key from disclosure, Not your key, not your coin!
3. Decentralization of assets
You can disperse your own funds in wallets and trading platforms. Although the FTX accident has led to a lack of trust in the centralized trading platform , for the vast majority of people, it is better to keep assets in several centralized trading platforms than in their own hands. It is relatively safer and more convenient than a wallet . As long as the loss is not particularly large, several leading platforms can generally afford compensation.
There are a few points to note when using a centralized trading platform:
- Enable triple verification (mobile phone, email, Google secondary verification)
- Open the whitelist for coin withdrawal
- Download the app from official channels
- When transferring funds, confirm whether the address is correct
epilogue
Through the above relevant knowledge, novice users can have a comprehensive understanding of blockchain asset security related knowledge. With the development of blockchain and the increase of interaction on the chain, the use of wallets will gradually become an item. Important basic skills and various measures are actually not absolutely safe , but relatively speaking, they can allow us to avoid most pitfalls, and with the development of blockchain, new problems will continue to appear, and we need to continue to improve own knowledge base.
Small amounts of funds may not be kept in accordance with the above method, but the preservation of your own large positions of funds must be cautious and cautious, because one of your mistakes may cause you to be thrown away by the blockchain train forever. Can never catch up.
Disclaimer: As a blockchain information platform, the articles published on this site only represent the personal opinions of the authors and guests, and have nothing to do with Web3Caff's position. The content of this article is for information sharing only, and does not constitute any investment advice or offer, and please abide by the relevant laws and regulations of your country or region.