There was a time when maintaining one's identity was a relatively simple matter; necessary archives such as passports and birth certificates were kept secure and shared face-to-face when needed. However, as the digital realm becomes our new territory, and as we enjoy the convenience brought by virtual identity verification, we gradually find that the convenience and accessibility of centralized data systems are accompanied by complex problems and fragmentation. This leaves users with a tricky choice: Should privacy and security be sacrificed for convenience and accessibility?
Initially, the idea of centralizing our data was intended to simplify the process, but it inadvertently made us more vulnerable. Data is stored centrally in digital databases, making it a magnet for hackers. This has resulted in a chaotic online environment where data leaks continue to occur and make it possible for third parties to take control of our personal information, which is often stolen, traded and misused.
Challenging the norm with ZKP
ZK is a concept in the field of cryptography that focuses on verifying the validity of information. It enables one party to prove to another party that they possess certain private information without exposing it. This is achieved by providing evidence that the information meets certain conditions while protecting additional details.
In the context of establishing an identity, the verification process appears to be fairly simple. This occurs when we provide our identity to an outside party to confirm certain information, such as the legal age requirement to purchase alcoholic beverages in the United States is 21. However, the real complexity lies in ensuring that we only share the specific information we wish to reveal, because every time someone checks our ID to confirm our age, they inadvertently obtain a wealth of additional personal data, including our date of birth, Residential address and other sensitive information. This situation requires us to rethink the way we authenticate to solve this challenge.
ZK cryptography enables us to completely change the traditional "trust and assumption" model and move towards the formalization of "verification and trust". In this new framework, trust is no longer taken for granted but is gradually earned through the verification of assertions. Individuals can now substantiate their claims, such as age, nationality or other identity-related proof, without revealing sensitive information.
Absolute anonymity may not always be consistent with the practical goal of effectively leveraging digital identity. At this time, the concept of selective disclosure, with the help of ZK technology, becomes particularly critical. While the default configuration emphasizes comprehensive privacy, we must realize that privacy operates on a continuum and users should have the ability to disclose only relevant information as needed.
Extended reading: Popular Science | What are zk-SNARKs? Vitalik sets the tone and zero knowledge proves that the next ten years are "very important"
Who is using ZK to build digital identities?
Polygon ID
Polygon ID represents a self-sovereign identity solution that incorporates ZKPs to establish default privacy settings. By employing the Circom ZK toolkit, it enables the creation of zero-knowledge cryptographic structures, specifically zkSNARKs circuits, thereby simplifying complexity and increasing efficiency.
The core of Polygon ID includes three key modules: identity holder, issuer and verifier, which are collectively called the "Trust Triangle" by Polygon.
- Identity Holder: The entity responsible for protecting claims in its digital wallet. The issuer issues a Verifiable Credential (VC) to the identity holder. Identity holders are then responsible for generating ZKPs for the VC they receive and submitting these proofs to verifiers. The role of the verifier is to verify the authenticity of the proof and check whether it meets pre-set standards.
- Issuer: The entity (individual or organization) responsible for issuing VC to identity holders. The issuer adds a cryptographic signature to the VC. It is worth noting that each VC is generated by a specific issuer.
- Verifier: Responsible for verifying the certificate submitted by the identity holder. The verifier initiates a request asking the holder to provide proof based on the VC stored in his digital wallet. During the verification process, the verifier performs a series of evaluations, such as confirming whether the VC is signed by the intended issuer and ensuring that the VC meets specific standards set by the verifier.
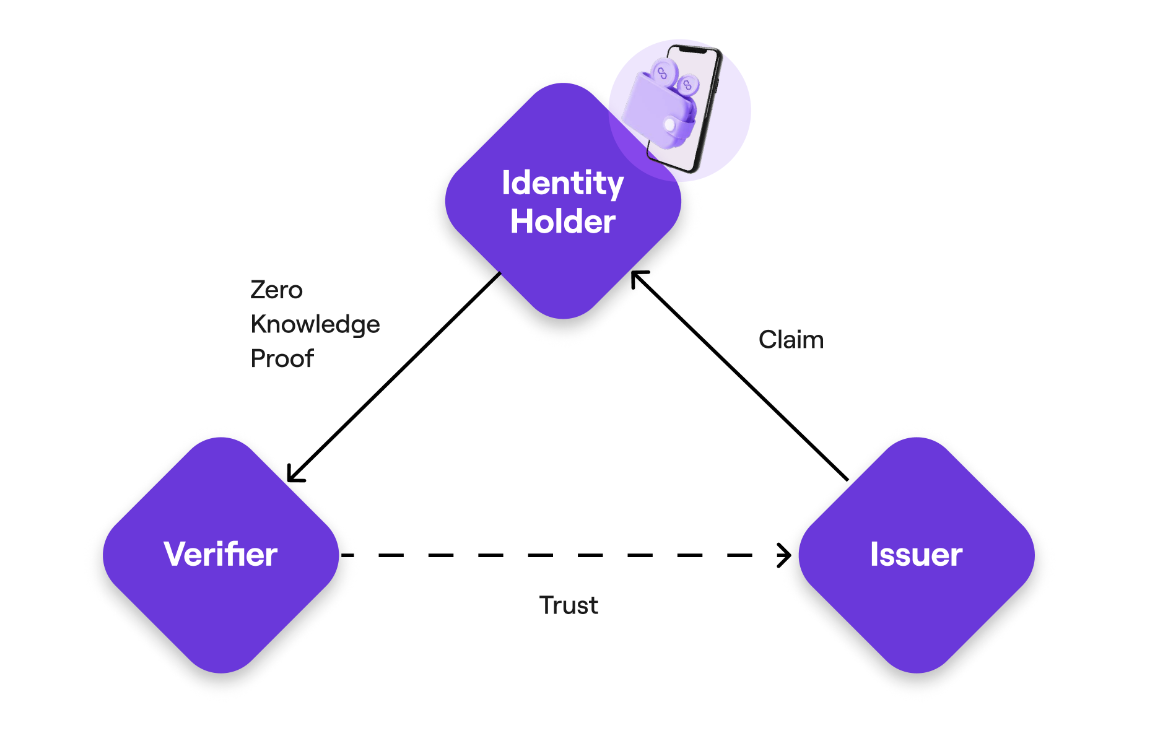
With zero-knowledge proofs to verify state transitions, Polygon ID achieves two key goals: maintaining the integrity of the identity state and preventing unauthorized modifications. This approach establishes a powerful mechanism to ensure privacy and security of identity state transitions.
Sismo
Sismo is a platform that uses zero-knowledge proof and privacy protection technology to give users greater control over their personal data. Sismo's innovative solution is centered around Sismo Connect, a Privacy Center alternative to traditional non-sovereign single sign-on (SSO) systems such as "Sign in with Google", or restricted options such as "Sign in with Ethereum".
Sismo Connect enables applications to request access to user data without directly touching sensitive personal information. By leveraging Sismo Connect, users can consolidate their identities in a data vault, a secure, encrypted repository for personal data collected from a variety of Web2 and Web3 sources, including credentials and certificates.
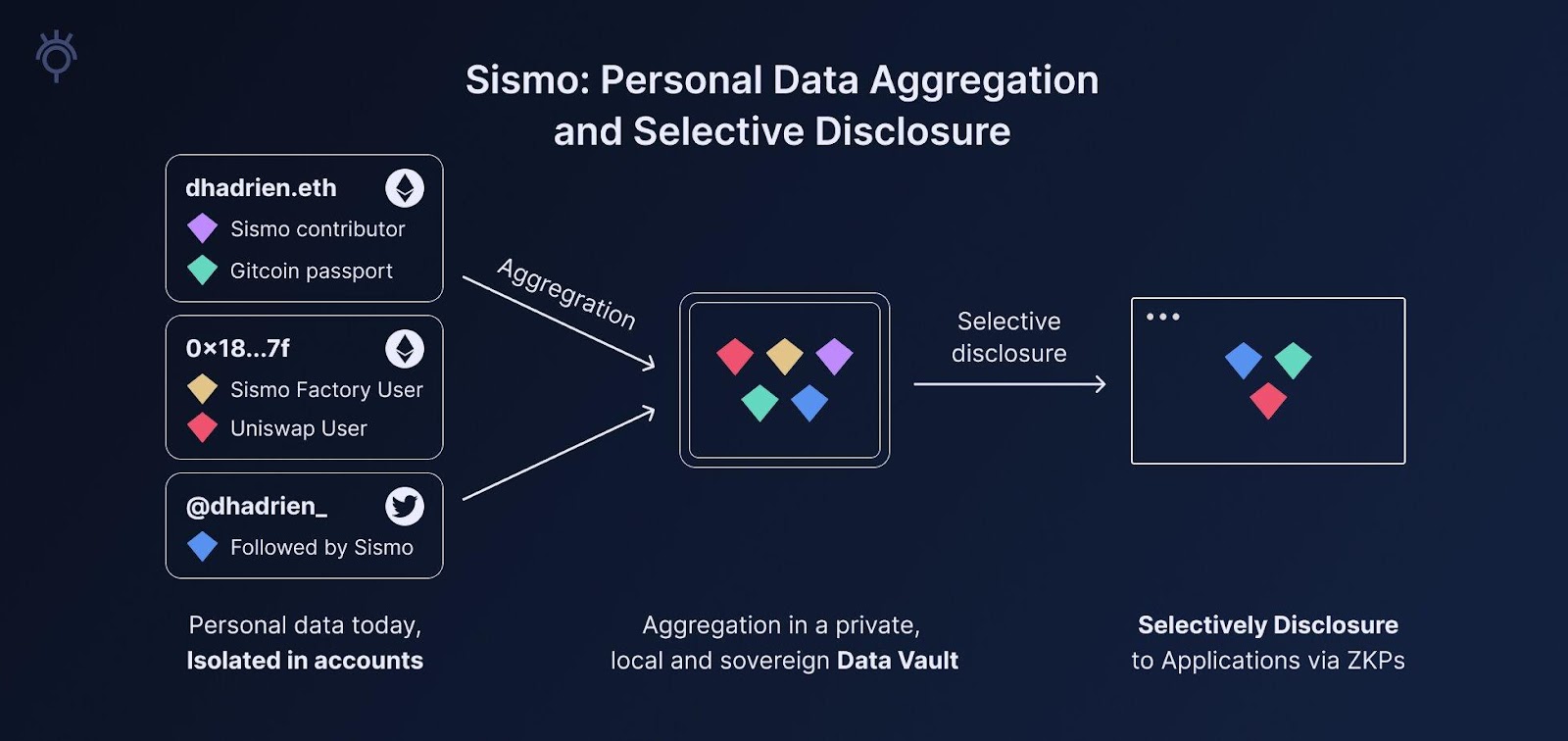
In a data vault, users can securely store individual data units called data gems that contain important aspects of their digital identities. These data gems can include records from registries, platform contributions, or specific demographic information. The Vault acts as a private and impenetrable repository, ensuring users have full ownership and control of their integrated digital identities.
By leveraging Sismo's communication protocol, users can confirm their ownership of data gems by generating zero-knowledge proofs. These proof-based verification methods enable users to confirm their control over specific data without revealing sensitive information, ensuring a high level of privacy protection throughout the process. Applications tightly integrated with Sismo Connect can accept and verify these certificates, empowering users to unobtrusively reveal their data gems while protecting the confidentiality of the underlying data sources.
For developers, integrating Sismo Connect into their applications provides access to a wide range of user data from Web2 and Web3 sources. By integrating Sismo Connect, applications can improve their functionality, including access management, reputation integration, and personalized user experience, while protecting user privacy through selective disclosure mechanisms.
ZPass by Aleo
zPass is Aleo’s recently launched privacy-centric credential protocol on October 25, built on the Aleo blockchain. This solution has been carefully designed to leverage ZK cryptography as a versatile tool to adapt to the ever-changing regulatory environment. The primary goal of the system is to provide strong verification while limiting exposure to current and potential future regulatory standards.
With zPass, individuals and organizations can securely store identity files on private devices and services, without requiring an online connection. They can then share these anonymous "certificates" to verify the underlying information of the relevant organization. This approach greatly simplifies the regulatory compliance and cybersecurity challenges typically associated with direct data storage.
Users have the autonomy to generate these certificates independently without modification or cooperation with the identity-issuing authority. This gives users precise control over what information they share and what they share it with, ensuring that only the personal information required for verification is revealed.
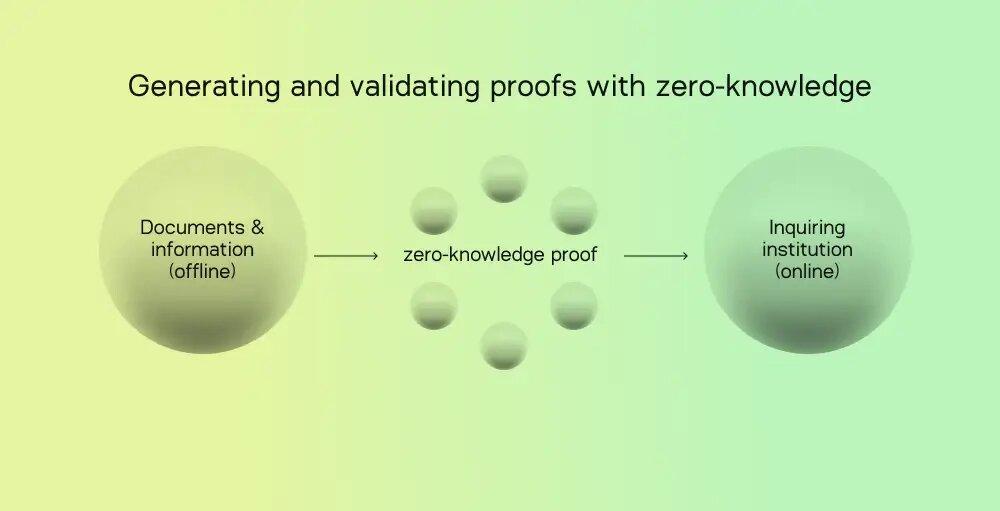
For example, imagine a scenario where a user wants to use their passport to confirm their identity to access a specific online service. With zPass, users can independently process and verify passport information locally. The final result is a binary true/false result and a ZKP used to confirm the accuracy of the result without exposing the actual archive.
zPass makes it easy to embed established credentials, such as passports, as verifiable evidence into the Aleo blockchain. This is achieved through Aleo's ability to execute programs that generate proofs directly on the user's device, all by leveraging WebAssembly (WASM). This approach ensures that sensitive data is protected in a secure local environment.
zkSBT by Manta Network
Manta Network 's zero-knowledge Soulbond Token (zkSBT) is at the forefront of privacy and security, outperforming traditional Soulbond Token (SBT), which are non-transferable digital identity tokens stored on the blockchain. zkSBT leverages zero-knowledge proofs to facilitate secure and confidential minting while protecting the privacy of ownership. These tokens can be applied to various blockchain networks, including Ethereum, Polygon, BNB Chain, etc., while maintaining their privacy features within the Manta Network's ecosystem. Verification is achieved through Proof Keys, which eliminates the need to disclose wallet details, making verification seamless.
zkSBT is closely tied to zkAddress, which serves as a reusable and transparent destination for confidential assets within the Manta Network. Each zkSBT is associated with a specific zkAddress, allowing multiple zkSBTs to co-exist under a single zkAddress. zkSBT includes metadata, including profile pictures, AI-generated images, and social relationship data, providing exceptional flexibility.
Manta Network has introduced a key technology called Proof Key. It enables users to confirm their identity and zkSBT ownership on the blockchain without relying on wallet signatures. This innovation simplifies mobile app integration and opens the door to a variety of verification scenarios. These include protecting the privacy of profile pictures, conducting on-chain transactions without exposing address details, verifying ownership of game items, and securely accessing decentralized social graph information.
Extended reading: "Kicker" overtakes in corners? Analyzing the market feasibility of Manta and dappOS
Worldcoin
In the Worldcoin ecosystem, World ID is a global identity protocol driven by two key technologies. These technologies enable individuals to digitally affirm their individuality and humanity while protecting their privacy. The basic components of this system include ZKP and Semaphore, which is a universal open source privacy layer based on zk-SNARKs technology and suitable for Ethereum applications. The system relies on a strong Proof of Person (PoP) credential, verified through an advanced biometric imaging device called The Orb. This synergy enables individuals to digitally validate their unique identity and humanity.
Every time a user uses their World ID, ZKP comes into play to verify their unique human identity. This means that no third party has access to a user's World ID or wallet public key, ensuring that cross-application tracking is impossible. Importantly, it ensures that the use of World ID is completely independent of any form of biometric data or iris coding. The basic principle is that when you are trying to establish your unique human identity, you should be able to do so without having to reveal any personal information about yourself, such as name, email address, social profiles, etc.
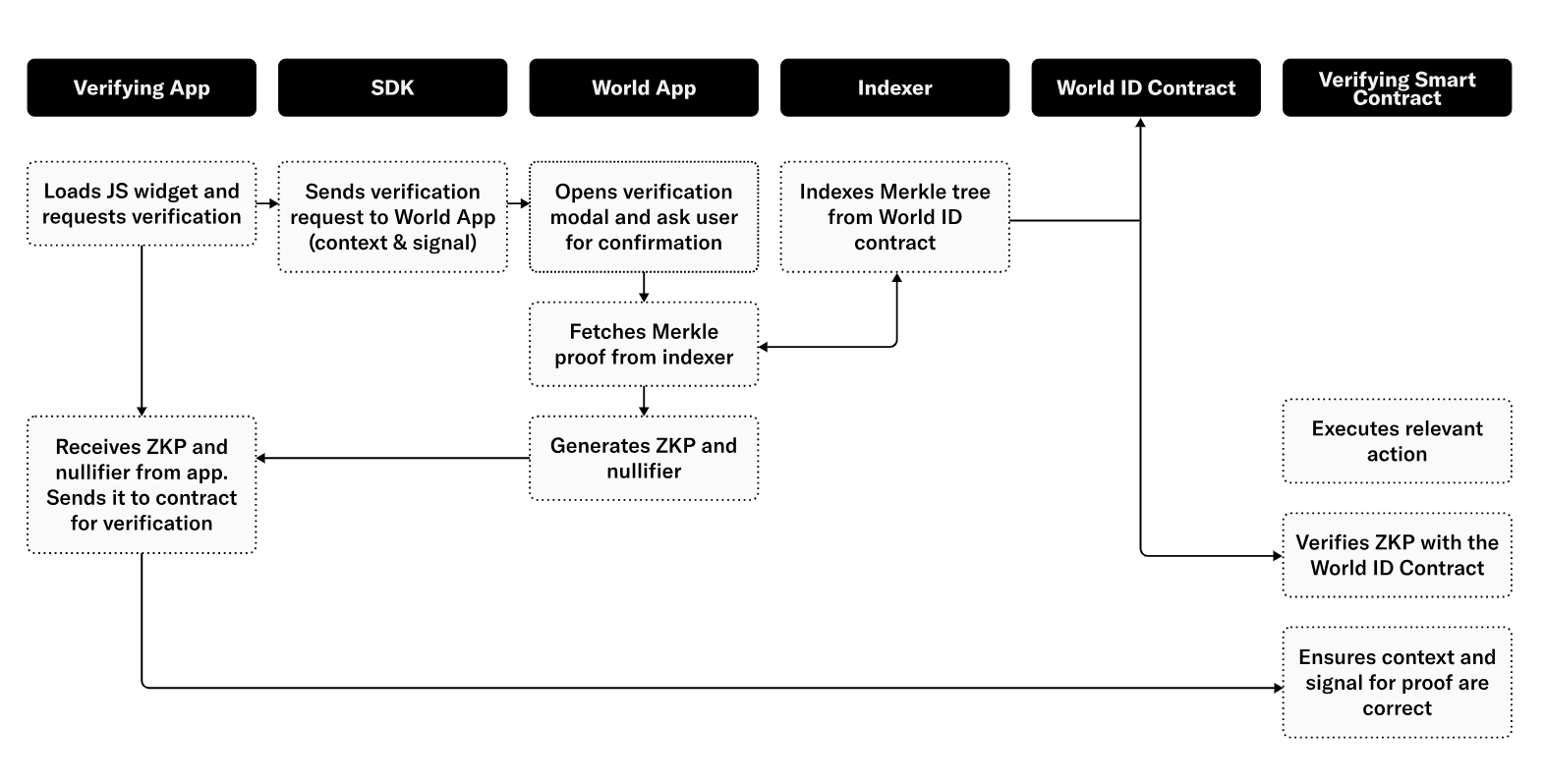
Outlined below is the process for verifying World ID registrations, enabling users to establish their unique human identity without revealing personal information.
The main goal of the project is to verify human uniqueness through encrypted on-chain iris scans to curb the proliferation of bots and artificial intelligence. When necessary, the system will generate ZKP to verify identity. Nonetheless, Worldcoin has faced scrutiny from community members concerned about the privacy, ethical considerations and security risks associated with storing biometric data. Although the project has been criticized, as of October 2023, more than 2.3 million World IDs have been registered, covering more than 100 countries.
Summarize
In the evolving digital environment, ZKP is becoming increasingly important. ZKP paves the way for the future of identity verification, ensuring user privacy is respected. The main obstacle facing decentralized identity verification solutions using ZK technology is the fragmentation of data across blockchain networks. There is currently no universally interoperable solution that enables users to use their identities seamlessly across networks, which limits the use of DID within each blockchain.
However, DID technology using ZK is gradually gaining popularity and attracting the attention of industry leaders. As the Web3 space continues to expand, we find ourselves on the verge of a potential industry breakthrough. Companies like Sismo are working hard to bridge the gap between Web2 and Web3. PolygonID appears to have the necessary technology and broad market access to make it a catalyst for DID.
As technology continues to develop and our understanding of ZKP continues to deepen, we can foresee that digital identity verification based on ZK technology will be more widely used, thereby enhancing the security and privacy of our online interactions and creating a more secure and more secure environment. Lay a solid foundation for a confidential digital future.