In 2024, North Korean hackers will steal more from crypto platforms than ever before
North Korean-linked hackers are notorious for their sophisticated and ruthless tactics, often leveraging advanced malware, social engineering, and cryptocurrency theft to fund state-sponsored actions and evade international sanctions. U.S. and international officials assess that Pyongyang uses stolen cryptocurrency to finance its weapons of mass destruction and ballistic missile programs, posing a threat to international security. By 2023, North Korean-linked hackers had stolen approximately $660.5 million through 20 incidents; by 2024, this figure increased to $1.34 billion across 47 incidents, a 102.88% increase in stolen value. These numbers account for 61% of the total amount stolen that year and 20% of the total number of incidents. Please note that in last year's report, we had published information about North Korea stealing $1 billion through 20 hacking attacks. After further investigation, we have determined that some of the larger hacks previously attributed to North Korea may no longer be relevant, reducing the amount to $660.5 million. However, the number of incidents remains unchanged, as we have identified other smaller hacks attributed to North Korea. As we obtain new on-chain and off-chain evidence, our goal is to continuously re-evaluate our assessments of North Korea-related hacking incidents. Unfortunately, North Korea's cryptocurrency attacks appear to be becoming more frequent. In the chart below, we examine the average time between successful DPRK attacks by the scale of the breach, and find that the frequency of attacks of various scales has decreased year-over-year. Notably, the frequency of attacks valued between $50 million to $100 million, as well as those over $100 million, is much higher in 2024 compared to 2023, indicating that North Korea is getting better and faster at carrying out large-scale attacks. This contrasts with the previous two years, when their typical profits were often less than $50 million per incident. When comparing North Korea's activity to all other hacking activity we monitor, it is clear that North Korea has been responsible for the majority of the largest-scale attacks over the past three years. Interestingly, the density of North Korean hacks with lower values, around $10,000, is also steadily increasing. Some of these incidents appear to involve North Korean IT workers increasingly infiltrating cryptocurrency and Web3 companies, compromising their networks, operations, and integrity. These employees often employ sophisticated tactics, techniques, and procedures (TTPs), such as using false identities, hiring third-party recruiting intermediaries, and manipulating remote work opportunities to gain access. In a recent case, the U.S. Department of Justice (DOJ) on Wednesday charged 14 North Korean nationals working as remote IT workers in the U.S. The companies earned over $88 million through stealing proprietary information and extorting employers. To mitigate these risks, companies should prioritize thorough hiring due diligence - including background checks and identity verification - while maintaining robust private key security to protect critical assets (if applicable). While all of these trends indicate North Korea has been highly active this year, the majority of their attacks occurred early in the year, with overall hacking activity stagnating in Q3 and Q4, as the earlier charts showed.Here is the English translation:In late June 2024, Russian President Vladimir Putin and North Korean leader Kim Jong-un will also hold a summit in Pyongyang and sign a joint defense agreement. So far this year, Russia has released hundreds of millions of dollars in previously frozen North Korean assets in accordance with UN Security Council sanctions, marking the continued development of the alliance between the two countries. At the same time, North Korea has deployed troops to Ukraine and provided ballistic missiles to Russia, and is reportedly seeking advanced space, missile and submarine technology from Moscow.
If we compare the average daily loss of DPRK vulnerabilities before and after July 1, 2024, we can see a significant decrease in the value of the stolen funds. As shown in the figure below, the amount stolen by North Korea decreased by about 53.73% afterwards, while the amount stolen by non-North Koreans increased by about 5%. Therefore, in addition to redirecting military resources to the conflict in Ukraine, North Korea's greatly increased cooperation with Russia in recent years may also have changed its cybercrime activities.
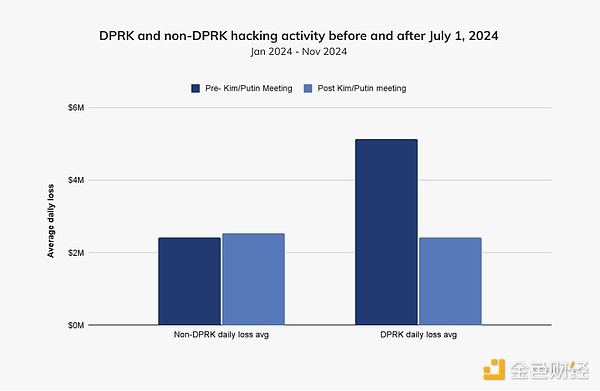
The decline in funds stolen by North Korea after July 1, 2024 is obvious, and the timing is clear, but it is worth noting that this decline may not be related to Putin's visit to Pyongyang. In addition, some events in December may change this pattern by the end of the year, and attackers often launch attacks during holidays.
Case Study: North Korea's Attack on DMM Bitcoin
A notable example of a North Korea-related hacking incident in 2024 involved the Japanese cryptocurrency exchange DMM Bitcoin, which was hit by a hack resulting in the loss of about 4,502.9 bitcoins, worth $305 million at the time. The attackers exploited vulnerabilities in the infrastructure used by DMM, leading to unauthorized withdrawals. In response, DMM, with the support of its parent company, fully reimbursed customer deposits by finding equivalent funds.
We were able to analyze the on-chain flow of funds after the initial attack. In the first stage, we saw the attackers transfer millions of dollars worth of cryptocurrencies from DMM Bitcoin to several intermediate addresses, ultimately reaching a Bitcoin CoinJoin mixing service.
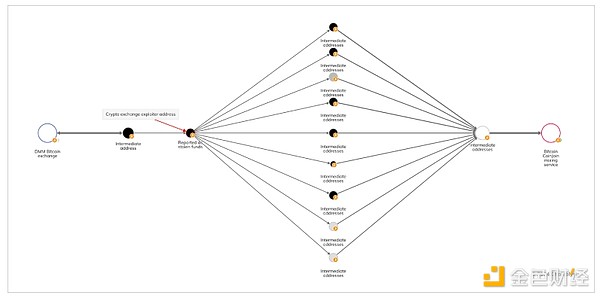
After successfully mixing the stolen funds using the Bitcoin CoinJoin mixing service, the attackers transferred a portion of the funds to Huioneguarantee, an online marketplace associated with the Cambodian conglomerate Huione Group, which is a major player in this field and facilitates cybercrime.
DMM Bitcoin has transferred its assets and customer accounts to SBI VC Trade, a subsidiary of the Japanese financial group SBI Group, with the transition scheduled to be completed by March 2025. Fortunately, emerging tools and predictive technologies are on the rise, which we will discuss in the next section to prepare for the prevention of such destructive hacker attacks.
Using Predictive Models to Prevent Hacker Attacks
Advanced predictive technologies are transforming cybersecurity by detecting potential risks and threats in real-time, providing proactive methods to protect digital ecosystems. Let's look at an example involving the decentralized liquidity provider UwU Lend.
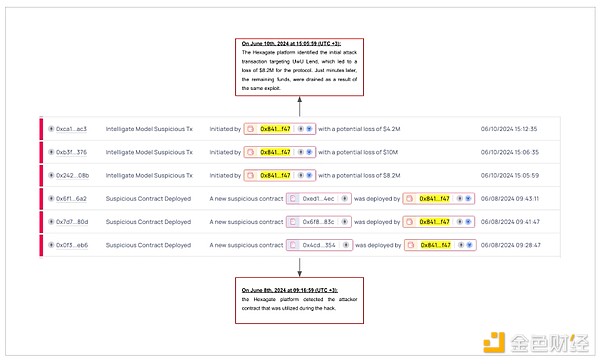
On June 10, 2024, attackers manipulated UwU Lend's price oracle system to obtain around $20 million in funds. The attackers launched a flash loan attack to change the prices of Ethena Staked USDe (sUSDe) on multiple oracles, leading to incorrect valuations. As a result, the attackers were able to borrow millions of dollars within seven minutes. Hexagate detected the attack contract and its similar deployments about two days before the vulnerability was exploited.
Although the attack contract was accurately detected in real-time about two days before the vulnerability was exploited, its connection to the exploited contract was not immediately apparent due to its design. With the help of other tools like Hexagate's security oracles, this early detection can be further leveraged to mitigate the threat. Notably, the first attack that caused $8.2 million in losses occurred just minutes before the subsequent attack, providing another important signal.
Such warnings issued before major on-chain attacks have the potential to change the security posture of industry participants, enabling them to fully prevent costly hacker attacks rather than just respond to them.
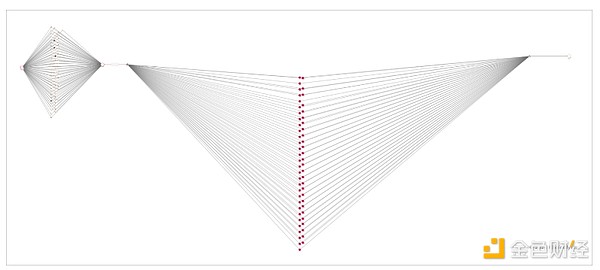
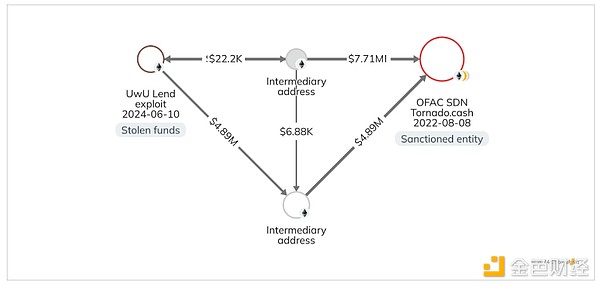
In the figure below, we see the attacker transferring the stolen funds through two intermediate addresses before reaching the OFAC-approved Ethereum smart contract mixer Tornado Cash.
However, it is worth noting that merely accessing these predictive models does not guarantee the prevention of hacker attacks, as protocols may not always have the appropriate tools to take effective action.
The Need for Stronger Crypto Security
The increase in cryptocurrency thefts in 2024 highlights the industry's need to address the increasingly complex and evolving threat landscape. While the scale of cryptocurrency theft has not yet returned to the levels of 2021 and 2022, the resurgence underscores the gaps in existing security measures and the importance of adapting to new exploitation methods. To effectively address these challenges, collaboration between the public and private sectors is crucial. Data-sharing initiatives, real-time security solutions, advanced tracking tools, and targeted training can empower stakeholders to quickly identify and eliminate malicious actors, while building the resilience required to protect crypto assets.
Furthermore, as the regulatory framework for cryptocurrencies continues to evolve, scrutiny of platform security and customer asset protection may intensify. Industry best practices must keep pace with these changes to ensure prevention and accountability. By establishing stronger partnerships with law enforcement and providing teams with the resources and expertise for rapid response, the cryptocurrency industry can strengthen its anti-theft capabilities. These efforts are not only critical for protecting individual assets, but also essential for building long-term trust and stability within the digital ecosystem.