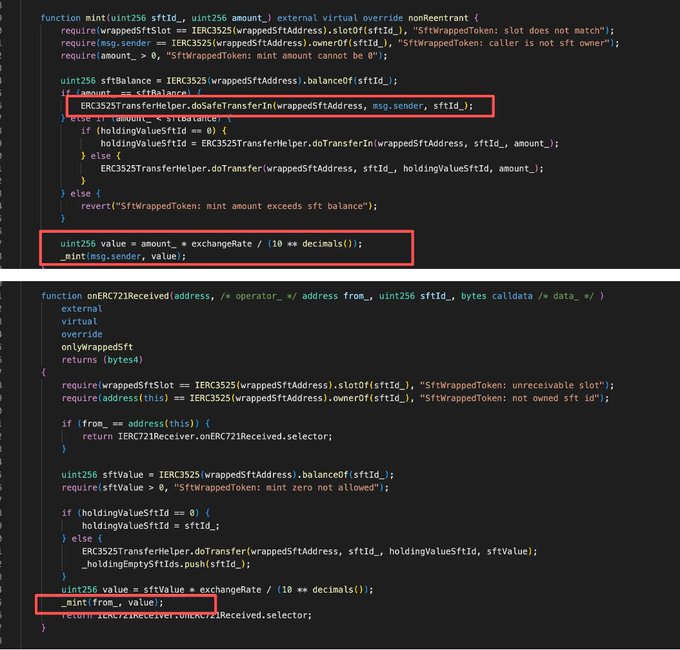
The @SolvProtocol BitcoinReserveOffering contract was reportedly exploited, resulting in a loss of ~$2.7M. The root cause is a reentrancy issue caused by an unintended interaction between mint() and the ERC721 receiver callback. When redeeming the entire value of an ERC-3525 SFT, the contract transferred the SFT via safeTransferFrom (doSafeTransferIn), triggering onERC721Received. The callback immediately minted BRO based on the SFT value. After returning, mint() resumed and minted BRO again for the same value, effectively double-counting the asset. By repeatedly cycling burn → mint, the attacker amplified their BRO balance, inflating a small initial amount into a large supply and ultimately exchanging it for SolvBTC to realize the profit. Attack TX: app.blocksec.com/phalcon/explo...…

Solv Protocol
@SolvProtocol
03-06
Incident Update: BRO Vault
A limited exploit occurred in one of our BRO vaults, affecting a very small number of users (<10).
The impacted amount is 38.0474 SolvBTC.
All other vaults and user funds remain secure and unaffected. We're actively investigating with top security
Sector:
From Twitter
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share
Relevant content