The vulnerabilities of DeFi protocols come not only from code defects or attacks, but also from economic factors such as market volatility, governance manipulation, and liquidity crises. Traditional technical (code) audits mainly focus on whether the code runs as expected, but they usually cannot consider the impact of market pressure or manipulation on the stability of the protocol.
Technical (code) audits aim to ensure that the code runs as expected and that there are no exploitable vulnerabilities or defects. However, the scope of technical audits is usually limited to an independent review of the protocol itself, without considering the broader economic environment or the interdependencies between protocols.
What is an economic audit?
Economic auditing is a security practice that goes beyond the scope of technical auditing. Technical audits typically focus on finding code vulnerabilities or defects, while economic audits evaluate the protocol's performance under various economic scenarios by simulating real market conditions and stress testing.
The focus of economic audits is to understand the economic interactions within DeFi protocols, and how external factors such as market volatility, liquidity crises, and governance manipulation can exploit the vulnerabilities of the protocol.
One of the key aspects of economic audits is simulating market conditions, such as dramatic price fluctuations, changes in liquidity, or shifts in user behavior. Another critical step is reviewing the governance structure of DeFi protocols. Governance-related vulnerabilities may allow malicious actors to take control of the protocol through manipulation of the voting system, as seen in the Beanstalk incident.
Furthermore, economic audits will evaluate the incentive mechanisms within the protocol to ensure they promote healthy participation and prevent malicious behavior. Poorly designed incentives may encourage attacks or opportunistic behavior, undermining the stability of the protocol. Economic audits also analyze the potential cascading effects that may occur if a particular protocol or token is attacked, especially in the highly interconnected DeFi ecosystem, where such chain reactions can have severe consequences.
These audits aim to predict the chain reactions that a single attack may trigger across multiple protocols, similar to how financial crises in traditional finance can spread from one industry to another. The high degree of interconnectedness in DeFi makes these cascading effects particularly dangerous, as the failure of one protocol can severely impact the liquidity, pricing, and governance of other protocols.
Finally, economic audits also assess whether the risk parameters within the protocol are well-calibrated to withstand potential stress or manipulation. Economic audits can help protocols identify and mitigate economic vulnerabilities that technical audits cannot, providing a more comprehensive security framework for the DeFi ecosystem.
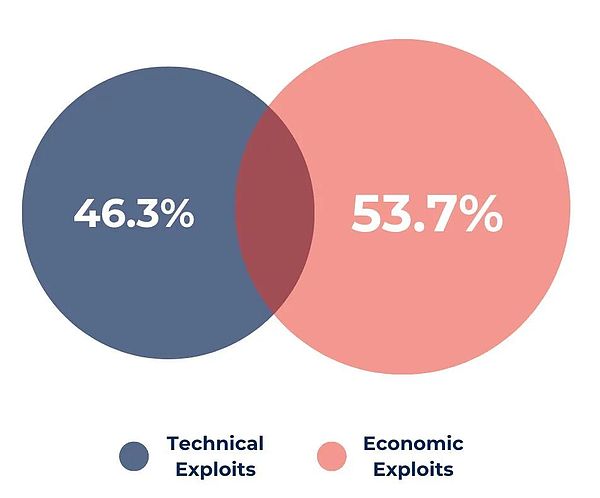
Technical Audit vs. Economic Audit
While both audits are crucial, they have different focuses and cannot substitute for each other.
Atomic operations vs. Complex operations dependent on external factors
Technical Audit: Focuses on ensuring that the code executes atomic operations, where an operation either completes entirely or fails entirely, minimizing the risk of partial execution failures that could lead to attacks. Technical audits examine the specific code logic to ensure it runs as expected and has no vulnerabilities or defects.
Economic Audit: Goes beyond the realm of atomic operations, focusing on the broader economic environment, where complex operations depend on factors external to the protocol, such as external liquidity, market prices, or governance decisions. Economic audits simulate these conditions to evaluate how external factors may expose vulnerabilities or risks in the protocol.
Technical Audit: Focuses on ensuring that the code executes atomic operations, where an operation either completes entirely or fails entirely, minimizing the risk of partial execution failures that could lead to attacks. Technical audits examine the specific code logic to ensure it runs as expected and has no vulnerabilities or defects.
Economic Audit: Goes beyond the realm of atomic operations, focusing on the broader economic environment, where complex operations depend on factors external to the protocol, such as external liquidity, market prices, or governance decisions. Economic audits simulate these conditions to evaluate how external factors may expose vulnerabilities or risks in the protocol.
Code vulnerabilities vs. Exploitability
Technical Audit: Aims to identify specific vulnerabilities in the code that could be exploited by attackers. For example, if a function does not properly implement security measures, a hacker may be able to use it to steal funds or manipulate critical parameters of the protocol.
Economic Audit: In contrast to technical audits' focus on code vulnerabilities, economic audits examine how broader economic conditions may expose the protocol to attack risks. For instance, an economically risky governance mechanism may lead to malicious takeovers or market manipulation events, which can have severe consequences for the protocol.
Audit Scope (Internal/External)
Technical Audit: The scope of technical audits is typically defined by the protocol itself. Their focus is on reviewing the codebase, identifying technical vulnerabilities, and ensuring the protocol functions as expected from a purely functional perspective.
Economic Audit: The scope of economic audits is much broader, not only focusing on the internal logic of the protocol but also analyzing its interactions with the wider DeFi ecosystem, including market conditions, liquidity, token interdependencies, and governance structures. This broader scope provides a more comprehensive risk analysis, which is particularly important in the dynamic and interconnected DeFi ecosystem.
Technical Audit: The scope of technical audits is typically defined by the protocol itself. Their focus is on reviewing the codebase, identifying technical vulnerabilities, and ensuring the protocol functions as expected from a purely functional perspective.
Economic Audit: The scope of economic audits is much broader, not only focusing on the internal logic of the protocol but also analyzing its interactions with the wider DeFi ecosystem, including market conditions, liquidity, token interdependencies, and governance structures. This broader scope provides a more comprehensive risk analysis, which is particularly important in the dynamic and interconnected DeFi ecosystem.
Vulnerability Exploitation in Different Contexts
Technical Audit: Primarily ensures that the code itself does not have specific vulnerabilities, such as reentrancy bugs or integer overflow errors. Once the technical audit is completed, the code is considered secure in a controlled environment.
Technical Audit: Primarily ensures that the code itself does not have specific vulnerabilities, such as reentrancy bugs or integer overflow errors. Once the technical audit is completed, the code is considered secure in a controlled environment.
Economic Audit: In contrast, economic audits evaluate the protocol's performance in real-world scenarios, where external economic pressures (such as price manipulation or governance attacks) may expose the protocol's vulnerabilities. Economic audits simulate these real-world economic conditions to ensure the protocol can maintain security even under the influence of these external factors.
Economic Audit: In contrast, economic audits evaluate the protocol's performance in real-world scenarios, where external economic pressures (such as price manipulation or governance attacks) may expose the protocol's vulnerabilities. Economic audits simulate these real-world economic conditions to ensure the protocol can maintain security even under the influence of these external factors.
Difference in Audit Scope
Technical Audit: The scope is typically limited to the internal operations and codebase of the protocol. The focus is on checking if the smart contracts are running as expected and ensuring the code is free of errors and logical vulnerabilities.
Technical Audit: The scope is typically limited to the internal operations and codebase of the protocol. The focus is on checking if the smart contracts are running as expected and ensuring the code is free of errors and logical vulnerabilities.
Economic Audit: The scope is broader, considering external factors such as market dependencies, governance structures, and liquidity constraints. Economic audits evaluate the protocol's interactions with the wider DeFi ecosystem and analyze whether it can withstand economic pressures.
Economic Audit: The scope is broader, considering external factors such as market dependencies, governance structures, and liquidity constraints. Economic audits evaluate the protocol's interactions with the wider DeFi ecosystem and analyze whether it can withstand economic pressures.
Technical audits and economic audits are complementary, and both are necessary to build a comprehensive security framework.
Key Vulnerabilities Not Covered by Technical Audits
Technical audits cannot address vulnerabilities that arise from external economic factors, interdependencies, and interactions with other protocols, which can be identified and mitigated through economic audits.
Token Correlations and Cascading Effects
Token correlations are an important source of risk in DeFi, as the tokens of different protocols may be interdependent. For example, when the token of one protocol experiences a price crash, it can trigger a chain reaction across multiple platforms.
Technical audits typically do not assess the potential cascading effects that may occur when the tokens within a protocol are impacted by external economic conditions (such as market downturns or attacks on other protocols).
In contrast, economic audits simulate these scenarios to analyze the protocol's response. For example, the collapse of Terra Luna, where the depegging of its stablecoin caused widespread damage across the DeFi ecosystem.
Oracle Dependence and Price Manipulation
Many DeFi protocols rely on oracles to obtain external data, such as token prices or interest rates. However, this dependence introduces a common vulnerability: if the oracles are compromised or the data they provide is inaccurate or manipulated, the protocol may face significant risks.
Price manipulation attacks are a typical form of economic attack, where attackers profit by manipulating the token prices provided by oracles, such as through arbitrage opportunities or forced liquidations.
Technical audits typically only ensure that the code can correctly interact with the oracle, but do not assess the risk of price manipulation at the oracle level, which can have a devastating impact on the protocol.
Governance Attacks
Governance vulnerabilities are another major risk in DeFi protocols, especially in systems where voting rights are tied to token holdings. Attackers can take over the protocol through the governance mechanism, proposing malicious proposals or stealing funds, as shown in the Beanstalk vulnerability incident. In this event, the attacker temporarily borrowed a large amount of tokens through a flash loan, gaining control of 79% of the voting rights, and then pushed through the malicious proposal and stole $181 million.
Technical audits often overlook the governance structure and focus on checking the smart contract code. However, economic audits analyze the potential vulnerabilities in the governance system, particularly the ability to temporarily increase voting rights through means like flash loans, a risk that is often difficult for technical audits to detect.
Liquidity Crises and Protocol Stress
Liquidity crises are a major vulnerability in DeFi protocols. When a protocol's liquidity suddenly drops, it can lead to price slippage, forced liquidations, or collateral shortages, triggering a vicious cycle that puts the entire protocol under stress. Liquidity crises can be triggered by various factors, such as market downturns, increased token volatility, or large withdrawals.
Technical audits ensure that smart contracts function correctly under normal conditions, but they do not simulate low-liquidity stress scenarios, where the protocol may become vulnerable to attacks or unexpected behavior. In contrast, economic audits model these stress conditions, evaluate how the protocol would respond to liquidity tightness, and verify the existence of mechanisms to address or recover from such crises.
Typical Economic Attack Cases
These cases demonstrate in detail how attackers exploit the economic weaknesses in the design and structure of DeFi protocols, rather than code vulnerabilities, to carry out attacks.
Case 1: Mango Markets Attack
Date: October 2022Attack Method: Price ManipulationLoss Amount: $116 million
In this vulnerability, the attacker manipulated the price of the Mango token ($MNGO), causing price differences across multiple exchanges, which triggered large-scale forced liquidations and eventually depleted the protocol's funds. The attack process was as follows:

Initial Setup: The attacker used two wallets, each with $5 million in USDC, to launch the attack. Wallet 1 placed a large sell order of $483 million worth of MANGO tokens at a low price of $0.0382.
Price Manipulation: Subsequently, Wallet 2 was used to purchase all the MANGO tokens sold by Wallet 1 at this low price. The attacker then began aggressively buying MANGO tokens across multiple trading platforms (including Mango Markets, AscendEX, and FTX), driving the price from $0.0382 to $0.91, a sharp increase in a short period of time.
Exploiting the Price Surge: This sudden price spike caused a large number of short positions to be liquidated, as the MANGO token price exceeded the collateral value of the short sellers. As a result, the attacker profited from the price increase, while the MANGO token price subsequently dropped to $0.0259.
Result: The attack led to a significant loss of liquidity in the Mango Market, with over 4,000 short positions being liquidated, further destabilizing the protocol. This economic attack did not rely on technical vulnerabilities, but rather on cross-platform price manipulation, demonstrating that economic audits can help prevent or mitigate the impact of such attacks by simulating price manipulation scenarios.
Case 2: Beanstalk Attack
Date: April 2022Attack Method: Governance ManipulationLoss Amount: $181 million
The Beanstalk attack involved the attacker taking control of the governance system to push through malicious proposals. This attack highlights how governance vulnerabilities, if not properly managed, can cause as much damage as technical flaws. The key steps of the attack were:
1. Governance Vulnerability Attack: The attacker proposed two proposals to transfer the tokens in the Beanstalk treasury to their personal wallet. These proposals were disguised as legitimate governance changes. Beanstalk's governance system required a two-thirds vote through an emergency commit to approve proposals.
2. Flash Loan Attack: The attacker temporarily borrowed a large amount of Beanstalk tokens through a flash loan, enough to control 79% of the voting rights. With this absolute majority, the attacker successfully pushed through the proposals and executed the fund transfer, moving the tokens from the Beanstalk treasury to their personal wallet.
Result: This successful governance attack led to the BEAN token losing its peg, with its price dropping by 75%, significantly impacting the protocol's stability. The total loss from this attack was $181 million. If an economic audit had been conducted, simulating governance-related risks, this situation could have been mitigated to some extent. Economic audits can identify the risks of governance manipulation, particularly the ability to temporarily gain voting control through flash loans, a scenario often overlooked in traditional technical audits.
These two cases highlight the complementary role of economic audits to technical audits, ensuring that protocols can withstand attacks on price manipulation and governance vulnerabilities, areas that are often not adequately addressed in traditional security assessments.
Case 3: Terra Luna Stablecoin Depegging Incident
The collapse of the Terra Luna ecosystem is a prominent case of a protocol failure due to economic factors rather than technical vulnerabilities. This event is often seen as a textbook example of economic mismanagement, demonstrating how the loss of control in one aspect can trigger a chain reaction of collapse across the entire DeFi ecosystem.
Terra's stablecoin UST was algorithmically pegged to the US dollar, relying on its relationship with the Luna token to maintain price stability. The design premise was that UST could always be redeemed for Luna at a certain ratio, thereby preserving the price peg. However, this system was highly dependent on market confidence and liquidity, which began to unravel as external economic pressures mounted.
In May 2022, a major market event caused UST to depeg from the US dollar, with its price falling below $1. This triggered a "death spiral" effect, as UST holders rushed to redeem their tokens for Luna, rapidly diluting the Luna supply and causing its price to plummet. As the UST depegging continued to worsen, it formed a feedback loop that led to the collapse of both UST and Luna, ultimately rendering the protocol unable to recover.
The Terra Luna collapse had widespread ripple effects on the DeFi ecosystem. Many protocols were highly interconnected with Terra through liquidity pools, lending platforms, and staking services, and this event triggered a liquidity crisis, causing other protocols to suffer significant liquidations and fund losses due to their indirect exposure to Terra.
This collapse was not due to any specific code vulnerability or technical defect, but rather due to mismanagement of the economic model - namely, reliance on an algorithm-based stablecoin without sufficient reserves or protection mechanisms to withstand market volatility. Technical audits were unable to uncover this vulnerability, as the root of the problem lay in the economic model of the protocol, underscoring the necessity of economic audits that can simulate de-pegging scenarios and liquidity crises to identify such risks.
The collapse of Terra Luna has demonstrated how the failure of a protocol can trigger a chain reaction across the entire DeFi ecosystem, emphasizing the importance of assessing inter-protocol dependencies during the audit process. This collapse stemmed from an unsustainable economic model (the algorithm-based stablecoin) that was not prepared to withstand extreme market conditions. Economic audits can uncover a protocol's vulnerabilities by simulating these extreme scenarios.
The lack of sufficient reserves and failure to account for extreme market volatility were key reasons for the Terra Luna collapse, highlighting the importance of testing for such risks in economic audits.
This case underscores that even if a protocol's code is technically sound, it remains vulnerable to economic collapse if its economic model is not adequately stress-tested and the market environment is not properly considered.
The Layered Architecture of DeFi Protocols
DeFi protocols typically consist of multiple layers, each playing a specific role in the overall functionality of the protocol. These layers usually include:
1. Core Protocol Layer: This is the foundation of the protocol, containing the smart contracts that define the protocol's operations, such as lending, staking, or trading. Technical audits typically focus on this layer, ensuring that the smart contracts execute as intended and are free of vulnerabilities or coding errors.
2. Oracle Layer: DeFi protocols often rely on oracles to fetch real-time data from external sources (such as price data, interest rates, etc.). This layer is crucial for the proper functioning of the protocol, as incorrect data can lead to price errors, undercollateralization, or other risks. Economic audits will examine the protocol's reliance on oracles and the potential risks of oracle manipulation, which technical audits may not fully cover.
3. Governance Layer: Many DeFi protocols adopt decentralized governance structures that determine key protocol changes. The governance layer involves voting, token-based decision-making, and protocol modifications. Economic audits will analyze vulnerabilities in the governance structure, such as vote buying or flash loan attacks, where attackers temporarily acquire a large number of votes to influence protocol decisions.
4. Liquidity Layer: The liquidity layer ensures that the protocol has sufficient liquidity to operate normally. In lending or trading protocols, the liquidity layer determines whether users can access funds or execute transactions. Economic audits will simulate liquidity stress scenarios, testing the protocol's performance under conditions of insufficient liquidity, such as mass withdrawals or sudden market downturns.
Economic Risks in the Layered Architecture
Within the layered architecture of DeFi protocols, the interactions between layers can introduce economic risks that are often not covered by traditional technical audits.
1. Inter-Protocol Dependencies: Many DeFi protocols are interdependent, relying on other protocols to provide liquidity, collateral, or data. For example, a lending protocol may depend on an external stablecoin as collateral. If that stablecoin collapses or loses its peg to the fiat currency, the lending protocol may become undercollateralized, leading to widespread liquidations.
2. Cascading Effects Across Protocols: Attackers can exploit vulnerabilities in one layer to leverage the inter-protocol relationships and impact other layers, leading to more widespread losses. For instance, an attacker may manipulate the price of an asset in one protocol (through oracle manipulation) to affect lending, trading, or collateral operations in other protocols.
3. Liquidity Crises: The layered architecture also introduces the risk of liquidity crises, where the liquidity of one layer depends on another. Sudden withdrawal of liquidity from liquidity pools can disrupt the normal operation of the protocol, leading to a cascading failure that affects the functioning of other layers.
The interconnectivity of DeFi protocols means that risks often propagate across multiple layers. A vulnerability in one layer (such as the oracle or governance layer) can trigger a chain reaction, leading to the failure of other layers (such as the liquidity layer or core operations layer). Technical audits primarily focus on the core protocol, ensuring that smart contracts execute as intended, but they cannot simulate the systemic risks arising from these inter-layer interactions.
The layered architecture of DeFi protocols introduces complex economic risks that cannot be fully captured by technical audits alone. Economic audits, on the other hand, provide a critical assessment of the interactions between different layers, analyzing how they can be exploited or stressed under real-world conditions, helping to identify potential points of failure.
Conclusion
Relying solely on technical audits is insufficient to protect DeFi protocols from broader economic risks. Economic audits, through simulating real-market conditions and stress testing, evaluate a protocol's resilience to price manipulation, liquidity crises, and governance vulnerabilities. The DeFi industry must prioritize economic risk management to safeguard protocols from systemic threats. Currently, the economic audit market is underdeveloped, presenting a significant opportunity for companies focused on this domain. The future of DeFi security will require a combination of technical and economic audits to ensure protocols can withstand a wider range of vulnerabilities.