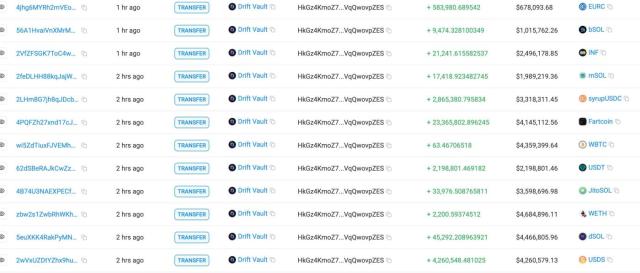
.@DriftProtocol on #Solana was exploited several hours ago. According to its public statement, this incident was not caused by a bug in its programs or smart contracts, and there is no evidence of compromised seed phrases. The attack used durable nonce accounts, pre-obtained fraudulent multisig approvals, and a rapid admin takeover. Specifically, the attacker prepared malicious admin-transfer transactions in advance and later triggered them through a durable-nonce flow. At execution time, one key transaction began with AdvanceNonceAccount, which consumed or advanced the durable nonce and enabled the pre-signed transaction flow to execute on-chain. In this context, AdvanceNonceAccount was the key step that made delayed execution possible, rather than allowing the transaction to expire quickly like a standard recent-blockhash transaction. The flow then proceeded through proposalApprove and vaultTransactionExecute, ultimately triggering UpdateAdmin and completing the admin takeover. After that, the attacker: 1. created a malicious or illiquid collateral market, identified on-chain as CVT, with permissive risk parameters; 2. switched to an attacker-controlled oracle and inflated CVT pricing; 3. raised or removed withdrawal guardrails across major real-asset markets. The attacker then posted large amounts of CVT as collateral, borrowed against the inflated value, and withdrew real assets including USDC, wETH, dSOL, JLP, and cbBTC. Based on currently traceable on-chain activity, this was the primary value-extraction path. The current loss estimate is $285,279,417. Admin transfer transaction: t.co/I2bS0QisEM Loss-tracking reference: t.co/20IIFHwtqp
BlockSec Phalcon(Phalcon_xyz) Message

Major Project Events
3240 subscribers
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share
Relevant content