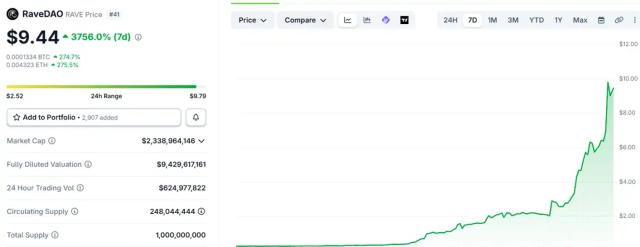
I had a sudden inspiration to analyze the Hyperbridge attack, so I had a simple local simulation of the attack process and discovered a few issues: 1. The attack essentially involved forging cross-chain messages and getting them verified by the Gateway. Many cross-chain bridge thefts follow a similar pattern, the core issue being vulnerabilities in the verification logic (e.g., checks were bypassed or missing in a certain path). 2. The hackers minted approximately 1 billion Bridged DOT tokens but only cashed out $237,000. Besides time constraints, market liquidity was genuinely poor. During a bull market with good liquidity, the losses could easily have been tens of millions of dollars. 3. For ordinary users: Minimize holding cross-chain wrapped tokens. Each additional bridge/contract adds another layer of risk. When funds are idle, especially during a bear market, it's advisable to store them in a cold wallet, rather than putting them all into DeFi for meager returns—principal safety should always be the top priority. Finally, cross-chain bridges remain a high-risk area; native assets are the most reliable protection. The counterfeit coins minted this time are still counterfeit coins, and the project team will eventually destroy them. The genuine coins you hold on the original chain will still be fine (unless the PolkaDot original chain also has problems).
This article is machine translated
Show original

很大很大的橙子
@0xVeryBigOrange
Bet ten bucks this is the project team doing evil themselves:
Polkadot bridge vulnerability exploited, 1 billion DOT minted on Ethereum network and already dumped
[MMS NEWS]
2026-04-13 12:52:15
Sector:
From Twitter
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share
Relevant content