Author: Buck Perley
Source: https://www.unchained.com/blog/from-vaults-to-networks-rethinking-bitcoin-custody
In the world of Bitcoin, we often believe we are building a completely new financial world and unleashing the power of programmable money. But when we truly observe the businesses currently built on Bitcoin, we can't help but ask ourselves: is this a technological revolution, or simply an evolution of an existing model? What I want to say is that we shouldn't interpret this programmable, autonomous currency as merely giving us the opportunity to build the exact same business model on another asset.
A true technological revolution occurs when people and businesses begin to create new habits and use the technology in entirely new ways. Building Bitcoin's native infrastructure means improving new ways for customers to access financial services. This, in turn, means creating not only new economic activities (completely new businesses), but also business and commercial relationships that were previously unimaginable.
Key Evolution
To capture these possibilities, let's start with the evolution of keys.
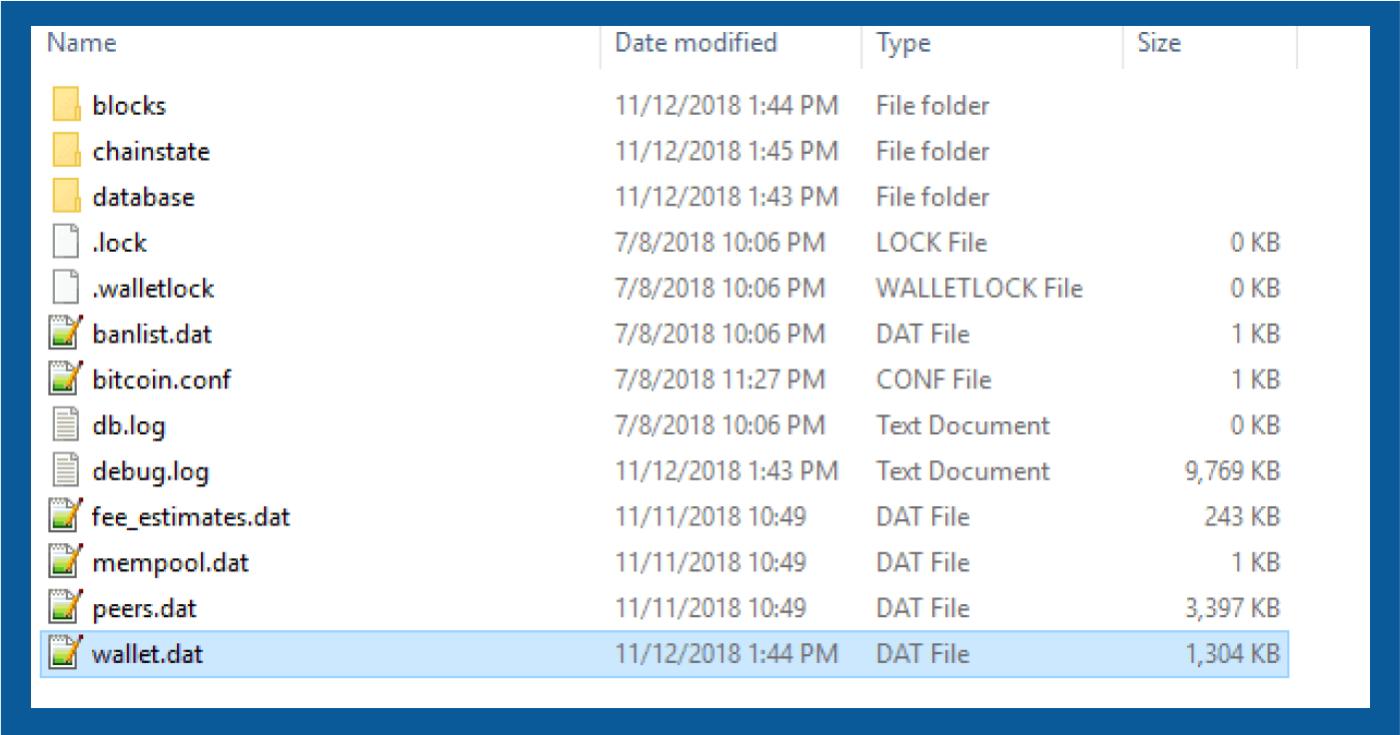
In the beginning, Bitcoin wallets were just a bunch of unrelated public and private key pairs… which was inconvenient to use. They were difficult to back up and difficult to restore. You could only access the raw data directly; you couldn't interact with it in a programmable way.
(Translator's note: The author is referring here to the earliest wallet implementation in Bitcoin/Bitcoin Core software—a wallet.dat file containing many unrelated public and private key pairs. This model is also known as a "keypool".)
Later, "deterministic hierarchical wallets ( HD Wallets )" and "extended public keys (xpub)" emerged, which were quite effective for a time. Using human-readable phrases as wallet backups became possible. You could isolate information that needed secure storage (private keys) in a dedicated location, and data that was publicly available to some extent (public keys) became easier to migrate. Computer code could also interact with keys in more creative ways.
(Translator's note: In HD wallets, all private keys are definitively derived from the same secret seed, so only this secret seed needs to be backed up. An extended public key can generate a set of public keys, which in turn form a set of addresses.)
P2SH (Pay to Script Hash) addresses provide us with new methods for interacting with keys, the most important of which is "multi-signature". Building on the HD wallet, we have developed a new mental model to understand the interaction of multiple keys, thereby creating wallets with more complex logic.
The latest generation of industry standards, such as miniscript and "descriptors," have helped unlock the power of Bitcoin script opcodes in a more robust way, and have made it possible to have more complex key relationships, such as including not only seeds but also time factors.
As our understanding of how to protect Bitcoin's public/private keys changes, our expectations of how to use these technologies to safeguard Bitcoin also change.
Evolution of Custody Models
In the beginning, everything was done DIY, and for a time, things went very well. This was, and still is, the highest level of protection. However, power comes with responsibility. If all your Bitcoin is protected by a wallet.dat file, you are responsible for securing that data. Sure, this means no one can confiscate your Bitcoin (unless you're tortured), but it also increases the risk of loss (we who search for hard drives in junkyards certainly have experience with this).
The risks and complexities of keeping Bitcoin keys entirely in one's own hands have led to the rise of full custody services. This has also attracted the trust of those who lack technical expertise, concentrating significant risk on inexperienced and irresponsible individuals , resulting in very painful lessons .
However, the market is constantly evolving, and as the Bitcoin custody service market has matured, service providers have also become more sophisticated. Losses due to theft or software errors are increasingly rare on large, regulated exchanges, making it a reliable place to entrust your Bitcoin. Best practices for security have been improved and marketed due to better internal and customer-facing security protocols. Consumers can even purchase insurance for such services.
However, single points of failure remain prevalent in this model. From internet account theft to government attacks by social engineering firms, the world is a dangerous place. Furthermore, regardless of how well a custodian protects its actual private key data, this custodial model is fundamentally still based on single-signature custody: your login method and account access rights are essentially your private key—which completely controls your funds.
Beyond account-controlled addresses and balances, vaults have emerged based on "cooperative custody." If you're reading this article, you're likely using this custody model. Partnering with a key broker leverages the security of multi-signature wallets while offering the convenience of a custodian partner. The frameworks of many commercial products (including Unchained) allow a trusted participant to hold fewer than a threshold of keys, thus establishing a partnership that achieves security, recoverability, and enterprise-grade protection.
While the account itself is no longer a single point of failure, since the ability to log in does not directly move funds, and preventing login does not prevent movement, the account holder remains a single point of failure. Social engineering attacks remain a serious threat, just as significant as losses due to neglecting the storage of key materials (a risk not present in traditional escrow models).
Enabling composable security through networks
The true power of collaborative safekeeping models is revealed when our static safes move beyond the dynamic realm of open standards and networks. A system built on a network (that is, the relationships between independent and distributed nodes) is easier to migrate and combine, and ultimately more robust.
In this context, what does it mean to "develop infrastructure for a technological revolution"? Just as using the internet for online communication has brought entirely new ways of interaction to individuals and businesses, in the custody of Bitcoin, we can make the platform not only a guarantor of fund security, but also enable security as needed.
Now, let's look at which long-standing technologies and standards in the Bitcoin world can help us develop this entirely new business model.
Family and friends: The power of trust

"Trust" is often considered a negative word by Bitcoiners. But it's not necessarily what people think. One of the strengths of a network is its redundancy. Your security no longer depends on the weakest link in your defenses. When you leverage trust by building a network of key holders, each with their own security mechanisms, the risk is distributed, and security is multiplied.
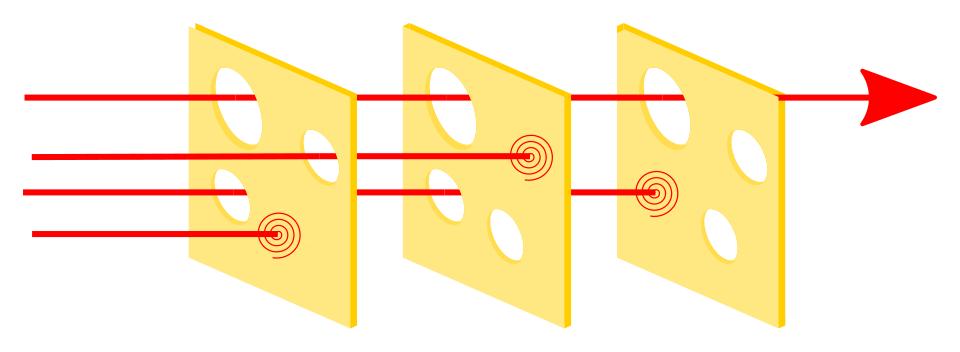
By joining a network that holds the keys , you can eliminate risks at the account holder level. Someone who believes they might be a victim of social engineering can add a family member (or a trusted close friend) as one of the key holders. While a family member's security may not be as robust as that of a company holding billions of dollars worth of Bitcoin, and a certain level of trust is required, a successful attack in a 2-of-3 arrangement requires breaching multiple points simultaneously. Because social engineering attacks often rely heavily on artificially created tension or carefully cultivated long-term trust , executing them simultaneously across multiple individuals and social contexts becomes an order of magnitude more difficult.
Perhaps more importantly, viewing Bitcoin custody from this network perspective allows us to comprehensively rethink existing business models and how to build a platform that can leverage networks. Imagine a Deliberate Use of Funds (DAF) where you don't directly trust them to properly use your funds, but instead join a network, publish your public key, and help distribute funds—not only making charitable donations but also paying various fees. This network makes you an active member, not a passive observer of your donations.
Flexible thresholds to suit your security needs
Achieving security through composability depends not only on "who" is in your network, but also on the shape of your network. When designing thresholds for multi-signature wallets, "less" often trumps "more." In most cases, a 2-of-3 threshold is sufficient , while multiple proxies sharing the key can make this model more secure. However, there are other scenarios where different threshold settings are more reasonable.
We can view this trade-off as a choice between "access autonomy" (the ability to move funds independently) and "proxy tolerance" (a key agent can act independently). Sometimes, a threshold setting offers both access autonomy and proxy tolerance, such as a 2-of-4 threshold, where you can recover funds independently without third-party assistance, but a key agent can also recover funds; this model also has its advantages.
The power of interoperable standards
Unlike traditional banking systems, Bitcoin's native financial services mean developing a platform based on open standards and open-source code. The platform shouldn't require you to enter their enclosed garden, because the funds you use belong to you. The more portable your interactions with funds are, the larger, more robust, and more compatible your network can be, as well as the incentives can be.
One example is development based on standards like " address descriptors ," which allows users to easily migrate to software using the same standards. Being able to interact with your own funds without entering a platform-defined area means you can:
- Manage your own wallet on your own node
- Partner with key holders who have never created an account on your platform.
- Interact directly with your wallet, without going through an API (Application Programming Interface) with a gateway.
- It leverages the security of key networks without being tied to a subjective, feature-deficient user experience.
- Allows other companies to join the key network without trust.
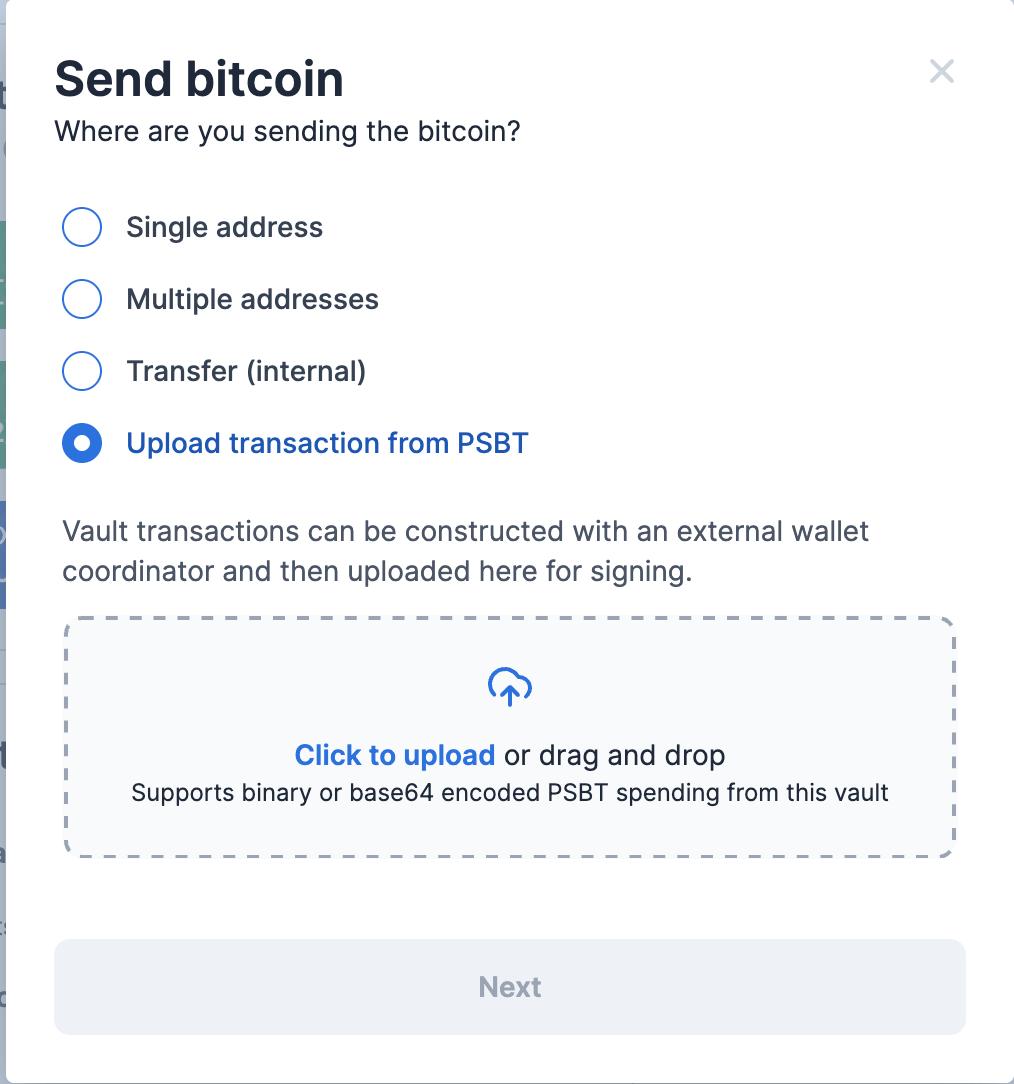
PSBT (format), short for "Partially Signed Bitcoin Transactions," is one example. If transaction data—i.e., the transaction's inputs, outputs, and signature—can be transmitted using a public serialization standard, rather than relying on proprietary APIs, it further expands the methods you can use in Bitcoin custody. Our recently developed transaction creation feature based on uploading PSBTs (available only upon request) means you can create transactions not only anywhere with your wallet, but also anywhere. It allows you to create and sign transactions on air-isolated devices, send transactions via email, and even request signatures from a platform-based key broker network after creating and signing transactions in other software. These new standards bring infrastructure to Bitcoin much like TCP/IP brought to the internet. Now we have standardized methods to network Bitcoin-native enterprises, so individuals can also leverage enterprise-grade security in their own custody devices.
New network, new services
The key idea behind all of this is that a truly Bitcoin-native financial services platform is built on open standards and should not force users to choose a particular model or platform. The ultimate state of truly open infrastructure is a diverse range of user experiences and new types of business that were previously impossible.
Just a heads-up, this is not legal advice, but purely hypothetical: let's imagine a business and customer relationship that would not exist without a solution native to Bitcoin.
Imagine you're starting a company offering customer-controlled, Bitcoin-backed HSAs. You believe the safest option for your target customer base (who are generally tech-illiterate) is a 2-of-4 threshold multi-signature custody system. You want to provide autonomy, ensuring customers can always spend independently; but you also want to provide fault tolerance, preventing them from losing access to their funds if something goes wrong with their private key materials. You also want to eliminate the burden of unilaterally transferring funds, so you share the responsibility of the key custodian with a platform provider (like Unchained, which is what we do in DAF ).
Setting up this account requires you (as the service provider) to request two public keys from a client. Because public keys can be publicly shared, the client can share public keys that are actually controlled by someone else (or an organization) with you. The client can decide to delegate one or even two keys to someone else and then share the extended public keys with you. Once you have these public keys, you can independently create this vault and manage your funding strategy.
But how will customers interact with your business? You could limit yourself to a service provider's platform (like unchained.com ), but you also feel that a more personalized experience for everyday use would be better. So you ask a trusted AI programming assistant to develop an app that can import wallet configuration files in JSON format . You want this app to connect to your own bitcoind node via RPC, rather than trusting someone else's node. It will be able to generate new addresses and generate tax reports at the end of the year based on changes in the balance.
What if you need to sign a transaction with a vendor that isn't part of the system? That's where PSBT comes in. PSBTs can be created by anyone with access to available UTXOs. Your system might be responsible for creating the transaction to be signed, or even collecting the first signature, before requesting another signature from the unchained system.
You still have a lot to do, such as providing alternative threshold options, device-independent xpub sharing (further decoupling customers from key sharing), and even allowing enterprises to share public keys with customers to enhance customer privacy. The power of networks and open standards is undeniable. Bitcoin has fundamentally changed the landscape of monetary power competition. The network of Bitcoin users can similarly transform our financial system.
(over)