Author: Blockstream Team
Source: https://blog.blockstream.com/quantum-computing-and-bitcoin-eli5/
Newspaper and news website headlines are all saying that quantum computers will destroy Bitcoin. The truth is: one aspect of Bitcoin's security is at risk. Blockstream engineers are already developing a fix.
What is a "quantum computer"?
Your laptop "thinks" in bits: they're like tiny switches with only two states, either 0 or 1. All the calculations such a computer performs, from loading web pages to verifying Bitcoin transactions, boil down to flipping billions of these switches at incredibly high speeds.
Quantum computers, on the other hand, think in terms of "qubits." A bit has only two states (0 or 1), while a qubit can hold a certain combination of these two values, only breaking it down into a single value when you measure it. Combining many qubits together, the set of states they can represent expands exponentially with the number of qubits. The mathematics that governs quantum hardware allows us to perform calculations simultaneously on all these states, something traditional computers cannot do.
You can think of it like a maze. A conventional computer can only try one path at a time until it finds the way. A quantum computer, however, can explore many paths simultaneously. For a certain type of mathematical problem, this means that (a quantum computer) can solve a specific problem in far fewer steps. However, this isn't true for all types of mathematical problems; quantum computers only have a speed advantage on a small subset of mathematical problems, rather than a complete dominance.
Quantum computers shouldn't be simply understood as "faster computers." They won't make your internet browser faster, your live streams smoother, or your files load faster. They are specialized tools, and the problems they excel at solving are directly related to your Bitcoin keys.
How does the Bitcoin system ensure the secure custody of funds?
The Bitcoin system uses two mathematical methods to ensure the safety of your funds.
The first type is used to prove/verify ownership . When you transfer Bitcoin, you need to sign the transaction with a secret key (your private key) to prove that the Bitcoin is yours. Nodes throughout the network will check your signature using an associated public key. The entire system relies on the assumption that no one can deduce your private key from your public key (therefore, no one can forge your signature to spend your Bitcoin). Modern computers cannot do this; they couldn't calculate it from the Big Bang to today.
The second category is used for mining . Every moment, Bitcoin miners compete to find a hash value that meets certain criteria; the competition is now so fierce that they collectively attempt trillions of guesses per second. This keeps the Bitcoin network running and prevents anyone from rewriting the transaction history.
Quantum computers pose a direct threat to the first type of mathematics, but have a much smaller impact on the second type, primarily affecting the centralization of networks rather than their character.
Why can quantum computers change this equation?
By running Shor's algorithm, a quantum computer can reconstruct a Bitcoin private key from a public key. Then, using this private key, one can claim Bitcoin as if it were the rightful owner.
Imagine a lock. Today's computers, within an imaginable timescale, cannot open it. But a sufficiently powerful quantum computer could.
Mining uses a different kind of mathematics (SHA-256 hashing is allowed). The "Grover algorithm" allows quantum computers to achieve quadratic speedups when running hash functions, thus giving large miners with access to quantum computers an advantage over smaller miners. This poses a threat to the decentralization of the mining industry, but it doesn't affect the Bitcoin network's ability to confirm transactions. In fact, this risk is far more distant than the previously mentioned risk of forged signatures: the quantum computing hardware required is much larger than that needed to attack secp256k1 (which calculates the underlying private key using the current Bitcoin public key), and the Grover algorithm cannot be parallelized well, which limits the translation of its theoretical advantages into practical performance.
The quantum computing threat facing Bitcoin is primarily related to who holds Bitcoin, not to how the network operates . Many reports have gotten this backwards.
How urgent is the threat?
Quantum computing hardware is advancing rapidly, but the significance of these numbers depends on the specific context. IBM's Condor gate-based chip reached 1121 qubits in 2023. Google's Willow chip only reached 105 qubits in December 2024, but achieved a more significant result: it implemented the first "below-threshold" quantum error correction mechanism, a goal researchers have been pursuing since 1995. Larger arrays of "neutral atoms" can now be stored— the Caltech team demonstrated an array of 6100 qubits —but the number of qubits alone cannot measure its computational usefulness.
The capabilities required to break the shared private key currently used by Bitcoin far exceed those of any current hardware. A research paper published between May 2025 and March 2026 reduced the projected requirements by approximately 20 times.
- The 2022 estimate (from the University of Sussex, 2022 ) states that approximately 13 million physical qubits would be needed to break a 256-bit key in one hour.
- Updated estimate (from Google Quantum AI, March 2026 ): Less than 500,000 physical qubits
- The most aggressive estimate (on an architecture that has not yet been proven effective): less than 10,000 physical qubits.
Current hardware still lags far behind even the most aggressive estimates, and looking solely at the number of qubits provides only a glimpse into the bigger picture. Google's paper warns that qubit counts fail to reflect most of the characteristics that determine a quantum computer's usefulness: error rate, fidelity, connectivity, and the ability to maintain error correction for extended periods until computation is complete. While the gap is indeed narrowing, not all crucial dimensions are seeing equal progress.
Experts generally believe that a quantum computer powerful enough to break cryptography is still 10 to 20 years away. The Global Risk Institute's 2025 report states that the probability of a cryptography-related quantum computer appearing within the next 10 years is between 28% and 49%, the highest estimate in the report's seven-year history. Adam Back, CEO of Blockstream (and inventor of the proof-of-work system) , estimates it to be 20 to 40 years .
Many organizations are scheduling their work based on more imminent estimates. NIST (National Institute of Standards and Technology) has released a timeline for the decommissioning of currently in-service signature standards (ECDSA and RSA), starting in the late 2030s. Google's quantum computing team has publicly recommended that organizations migrate sensitive systems, with a similar timeline. Whether the threat arrives in 10 or 40 years, the planned timeframes cover the Bitcoin network's own upgrade cycle.
Here's the most important part: Bitcoin network upgrades often take years . The Taproot upgrade took about three and a half years (from the first activation proposal in the mailing list), and quantum migration could take even longer because every coin holder needs to move their coins to a new address type, not just upgrade the software. So, start preparing now, not wait until the threat becomes a reality.
The countdown has begun.
Attackers using quantum computing do not need to wait for quantum computers to mature before choosing their targets. Once a public key is exposed on the blockchain (and can be observed by anyone) – whether it's an old P2PK output (where the public key is naturally exposed), a transaction spending script for any address, or a Taproot (P2TR) output with deposited funds – the public key is permanently recorded on the blockchain and can be attacked once the hardware is mature.
This doesn't require decryption. The Bitcoin network doesn't encrypt its consensus data. An attacker only needs to wait for the hardware to mature before they can directly calculate the private key behind a publicly available public key.
Security researchers have discussed a similar pattern in traditional cryptography called "capture now, decrypt later"; a paper published by the Federal Reserve in 2025 referred to it as an active risk of distributed ledger networks. The situation with Bitcoin differs in the details (because it's not encrypted, so there's nothing to decrypt), but the pattern is the same: collect the target data now, and attack it later.
Data collection may have already begun. The thief arrived shortly after.
Are all Bitcoins exposed to risk?
No, not all Bitcoin addresses face the same level of quantum computing risk.
The risks lie in the public keys that potential attackers can see, including:
- Early Bitcoin addresses (P2PK type) from 2009 to 2010 directly displayed the public key in the address; this included the 1 million BTC widely speculated to belong to Satoshi Nakamoto.
- Any address that has been used to send a transaction will have its public key revealed on the blockchain because the spending script will inevitably expose the public key (regardless of the address's type).
- A P2TR (Taproot) address exposes a version of the public key when funds are deposited into it. This was considered an acceptable sacrifice in the design of Taproot, as the threat of quantum computing seemed far off. Proposals like BIP 360 are designed to remove this exposure.
- Transactions that remain in the transaction pool. They haven't yet appeared on the blockchain, but their public keys (exposed in the transaction's spending script) are already visible to those observing the network. Therefore, a quantum attacker has the opportunity to compute the private key needed to sign the transaction before miners confirm it.
Researchers at Chaincode Labs estimated in March 2025 that approximately 30% of Bitcoin in circulation (about 6 million BTC) had their public keys exposed.
Temporarily secure : Older address formats, such as P2PKH, P2SH, P2WPKH, and P2WSH, hide the public key behind an additional mathematical layer (the address displays the hash of the public key). The public key is only revealed when you spend funds. If you receive Bitcoin with such an address but never spend it, your public key remains hidden. Approximately 65% of Bitcoin is held on unrevealed public keys.
This hidden state ends when you spend funds. Transactions broadcast across the entire network expose the public key, and a sufficiently powerful quantum attacker could attempt to calculate the private key capable of signing your transaction before it is confirmed. P2WSH addresses offer the strongest public-key hiding capabilities currently available, but even this will end when you spend funds.
Secure : Proof-of-Work and address derivation, and all structures that use SHA-256 hashing to link transactions together. Quantum algorithms cannot meaningfully brute-force these operations.
What will happen to Satoshi Nakamoto's money?
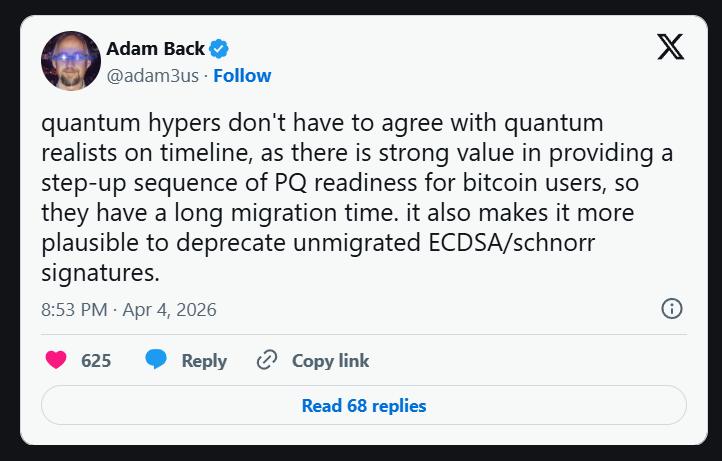
Adam Back points out that a long post-quantum migration window makes it more logical to "discard unmigrated ECDSA/schnorr signatures" via a soft fork. Under this approach, coins have several years to migrate to quantum-resistant addresses and remain secure; while coins that have never moved, whether due to a lost private key or from Satoshi Nakamoto's wallet, become unspendable by anyone, including attackers. Back also specifically opposes proposals to actively freeze quantum-vulnerable addresses, arguing that this would be an overreach by the developers.
The solution is not the most difficult part.
The cryptographic solutions are already in place. After eight years of evaluation, NIST (the US standardization body) finalized the first three post-quantum cryptography standards in August 2024. Mathematical readiness is there. But upgrading the Bitcoin network is the difficult part .
Larger signatures mean higher on-chain transaction costs . Even the smallest NIST-standardized post-quantum signature scheme (ML-DSA, FIPS 204) has a combined signature and public key size of approximately 3700 bytes. Bitcoin's current Schnorr key path cost is 64 bytes. This means that the cryptographic overhead for each transaction increases by approximately 58 times, and the number of transactions that can be accommodated per block decreases proportionally. Larger signatures mean larger transaction sizes and higher fees (borne by everyone).
Bitcoin changes slowly, and that's its nature . Modifying the Bitcoin protocol requires broad consensus within a global, decentralized network. However, Bitcoin has indeed been upgraded. Segregated Witness (2017) fixed transaction melting issues and improved scalability. Taproot (2021) brought smarter programming capabilities and better privacy. Both were soft forks accepted by the entire network. Post-quantum migration should follow a similar script, but it will be far more complex than either of these.
Every Bitcoin holder must act . Upgrading Bitcoin's code does not automatically make funds quantum-resistant. Each holder needs to actively transfer their coins from the old address to the new quantum-secure address. At Bitcoin's current throughput (approximately 3 to 10 transactions per second), it would take months or even years for all coins to complete this migration.
BIP 360 proponents point out that even under optimistic assumptions, a full migration would take several years. This process can only begin when the community agrees on a plan, and such a plan has not yet emerged.
Things that are already under development
The Blockstream team did not stand idly by.
The Liquid sidechain is a testbed . The Liquid network is a sidechain of Bitcoin, developed by Blockstream. This sidechain uses the Simplicity programming language, a smart contract programming language specifically designed for Bitcoin's security model. On the Bitcoin mainnet, deploying new cryptography requires a network-wide protocol change. However, on the Liquid sidechain using Simplicity, the same functionality can be deployed as a single smart contract without requiring a network-wide consensus change. This means that quantum-resistant protections can be rolled out in weeks, unlike Bitcoin, which requires years to implement a soft fork.
The first post-quantum transaction has already occurred on this live network . In March 2026, Blockstream's research division deployed " SHRINCS " (a compact post-quantum signature scheme) on Liquid. Five real transactions were broadcast and confirmed, creating the first post-quantum transaction on a Bitcoin sidechain in a production environment.
SHRINCS generates a 324-byte signature in normal operation. (If the same public key is reused in rich-state mode, the signature size increases by 16 bytes for each additional signature). The smallest signature under the NIST standard is over 2420 bytes. This 7-fold reduction in size determines whether signatures will account for the majority of transaction costs or whether they are practical in the context of blockchain.
SHRINCS relies solely on the security of SHA-256—which Bitcoin already uses in proof-of-work, address derivation, and Merkle trees. There are no new cryptographic assumptions; they are all assumptions already used in Bitcoin. Many of the post-quantum candidates initially submitted to NIST were broken by conventional computers during the standardization process, highlighting the value of a conservative cryptographic foundation.
Replace your hardware signer with SHRIMPS . In March 2026, Blockstream cryptographer Jonas Nick proposed SHRIMPS, specifically designed to address the lifecycle of hardware signers: what happens when your current device fails or you switch to a newer generation? A single backup can be imported to up to 1024 devices, allowing them to sign independently, with a signature size of 2.5 KB—still three times smaller than NIST's Hash Signature Standard (SLH-DSA). If you anticipate replacing your hardware signer, remember that SHRIMPS was specifically designed for this purpose.
The road to the Bitcoin mainnet . Blockstream's research department is exploring the design philosophy ofOP_SHRINCSVERIFY : the proposed opcode would allow Bitcoin scripts to directly verify post-quantum signatures based on hash functions. This work is still in the public discussion stage and has not yet become a final BIP. If a future version of this proposal is adopted, coin holders will be able to add quantum-resistant signature spending methods to their addresses individually, without waiting for the entire network to migrate.
This approach complements BIP 360 (Pay to Merklegen) (which removes the quantum-fragile key-spending path of Taproot). BIP 360 provides the address structure, while OP_SHRINCSVERIFY provides signature verification capabilities. They complement each other perfectly.
The testbed model . Liquid is a living financial network protecting billions of dollars in value. It's not new cryptography on Liquid that can produce the kind of evidence needed for Bitcoin's consensus upgrade process. OP_CAT already exists on the Liquid sidechain and spurred the BIP 347 proposal to include it in Bitcoin. Post-quantum cryptography could follow the same pattern: develop it on Liquid, prove it works in a real economic environment, and then use data from the production environment to formulate concrete proposals for the future.
What can we do today?
- Use modern wallet software . The Blockstream app uses a newer address format. In most address types, your public key is hidden (until you spend funds).
- Avoid address reuse . Most modern wallet software automatically generates a new address for each transaction. If your current software doesn't have this feature, please switch to another software. Reusing the same address increases your exposure to future quantum threats.
- Transfer your funds out of old addresses where your public keys have been exposed . If you have Bitcoin stored in addresses that have already been spent, especially old paper wallets or withdrawal addresses from early exchanges, transfer the funds to a completely new address. This will remove the "public key exposed" status from your funds.
- Follow the news . Keep track of the progress of BIP 360 and OP_SHRINCSVERIFY.
Advice for businesses : Consider the maturity timeline of quantum computers in your long-term custody plans. The migration window means that the decisions you make in 2026 will shape your experiences over the next 10 years.
The quantum computing threat facing Bitcoin is real and concrete, not as the news headlines suggest. However, Bitcoin's upgrade cycle is measured in years, and the resources required to break the cryptography used in Bitcoin are rapidly decreasing. There is time to prepare, but we must cherish it.
Understanding Blockstream's Post-Quantum Research
(over)