Author: Sabastian
Source: https://blog.bitbox.swiss/en/how-bitcoin-vaults-combine-convenience-with-security/
If you're using a regular Bitcoin wallet and someone steals your private key, there's only one outcome: they can immediately transfer all your money. This isn't a problem with Bitcoin itself, because transaction finality is one of its core values. But it does present a difficult trade-off for advanced self-custody devices: the more secure your device, the more troublesome it might be to spend the funds in it (even if it's your own perfectly legitimate spending).
Bitcoin's "vault" wallet feature attempts to improve this situation. Instead of forcing users to go through an inconvenient signing process every time (e.g., accessing multiple backups of a multi-signature wallet ), a vault wallet makes legitimate transactions relatively easy to create while maintaining a more secure backup path. This is the appeal of vaults for long-term savings: not "absolute security," but a better balance between everyday convenience and recovery difficulty .
Let's explain in detail how it works!
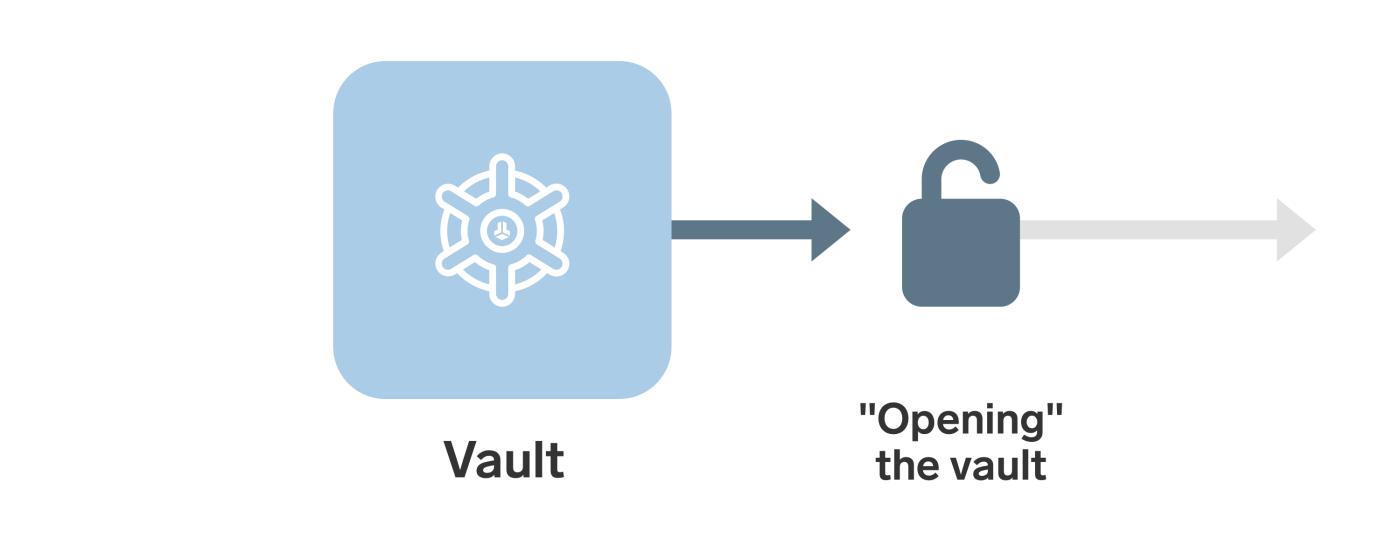
- Unlike regular wallets, safe wallets must be "opened" before you can spend money from them.
This "safe" is not that "safe".
First, it's important to understand that the term "vault" in the Bitcoin world has a rather broad meaning. Some companies use it to refer to more advanced cold storage products, often multi-signature wallets with additional redundancy (such as time conditions and cooperative custody ). Other times, it simply refers to the hardware signing device; for example, on our website, we call BitBox "your Swiss vault for Bitcoin." These are all harmless, but you should be aware that the label "vault" can refer to many different things; however, in this article, we're referring to a very specific wallet design .
From a more technical perspective, a Bitcoin vault refers to a wallet device that enforces " delayed withdrawals " and has a separate " wallet recovery path ." The purpose of this design is to make theft more difficult by eliminating the ability of an attacker to immediately empty the wallet. Let's discuss this in more detail.
Basic idea
The standard safe design can be explained using three concepts:
- Savings are kept in this safe —not a real safe, of course, but a wallet with specific spending conditions.
- The " Withdrawal Path " can "open the safe," but it will only start the countdown; the payment will only be completed after the countdown ends.
- The " Recovery Path " feature can halt any attempt to open the safe during the countdown and transfer the funds back to a more secure wallet.
Using the word "path" simply means that there are certain locked conditions that allow funds to move only in a specific direction and in a specific way.
What's interesting about this approach is that the withdrawal path and the recovery path can, and should, represent very different wallet devices . For example, the withdrawal path could be just a hardware signature device that you carry with you, while the recovery path could be a very secure multi-signature wallet with five backups in different physical locations.
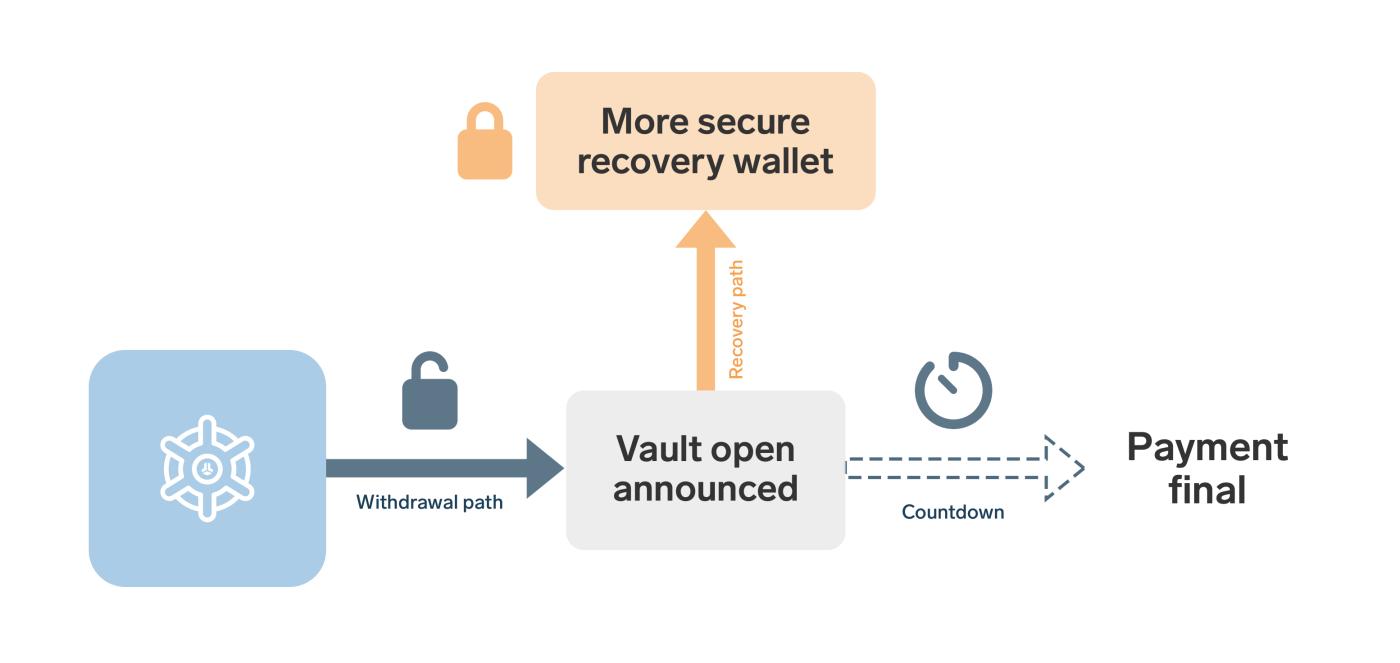
By combining two wallet devices in the same safe, we can combine the advantages of both : the withdrawal path offers convenience and ease of use, while the recovery path provides greater security and redundancy.
For example
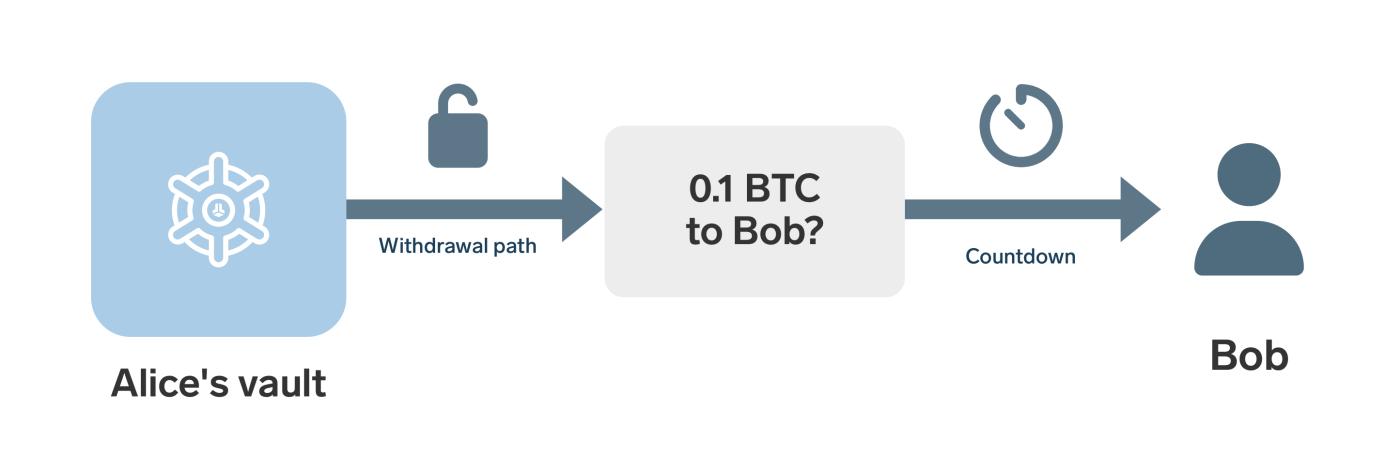
Suppose Alice holds 1 BTC in her vault wallet and wants to send 0.1 BTC to Bob. To do this, she first needs to open the vault using the standard withdrawal path . As mentioned earlier, this path can be very simple and doesn't even need to be optimized for security. Alice uses only a hardware signature in her withdrawal path. However, theoretically, she could even use a hot wallet on her smartphone without compromising the vault's security.
(Translator's note: "Cold storage" and "hot wallet" refer to private key storage devices that are offline and connected to the internet, respectively. For example, seed words written on paper are a form of cold storage; hardware signature devices are also a form of cold storage. Wallet software that stores private keys and runs on connected mobile phones and computers is a hot wallet.)
"Opening the safe" means creating a special transaction . This transaction indicates that someone is attempting to spend the funds in the safe and begins a countdown, let's say 24 hours. Within those 24 hours, Alice can cancel the payment to Bob and transfer the funds to a more secure wallet device. Only after 24 hours is the payment considered complete, and Bob can then claim the funds using a second transaction.
When Alice spent money from the safe and sent payments to Bob, she used a relatively simple withdrawal path. In this case, this meant she only needed to generate a signature using her regular wallet. However, in case of an accident, she still has a more secure recovery path as a backup plan. For example, if an attacker gains access to her everyday wallet and attempts to steal the 1 BTC, Alice can preemptively use the recovery path to transfer the funds to her more secure wallet. In simpler terms, she can always use this recovery path to move the funds to a safer location.
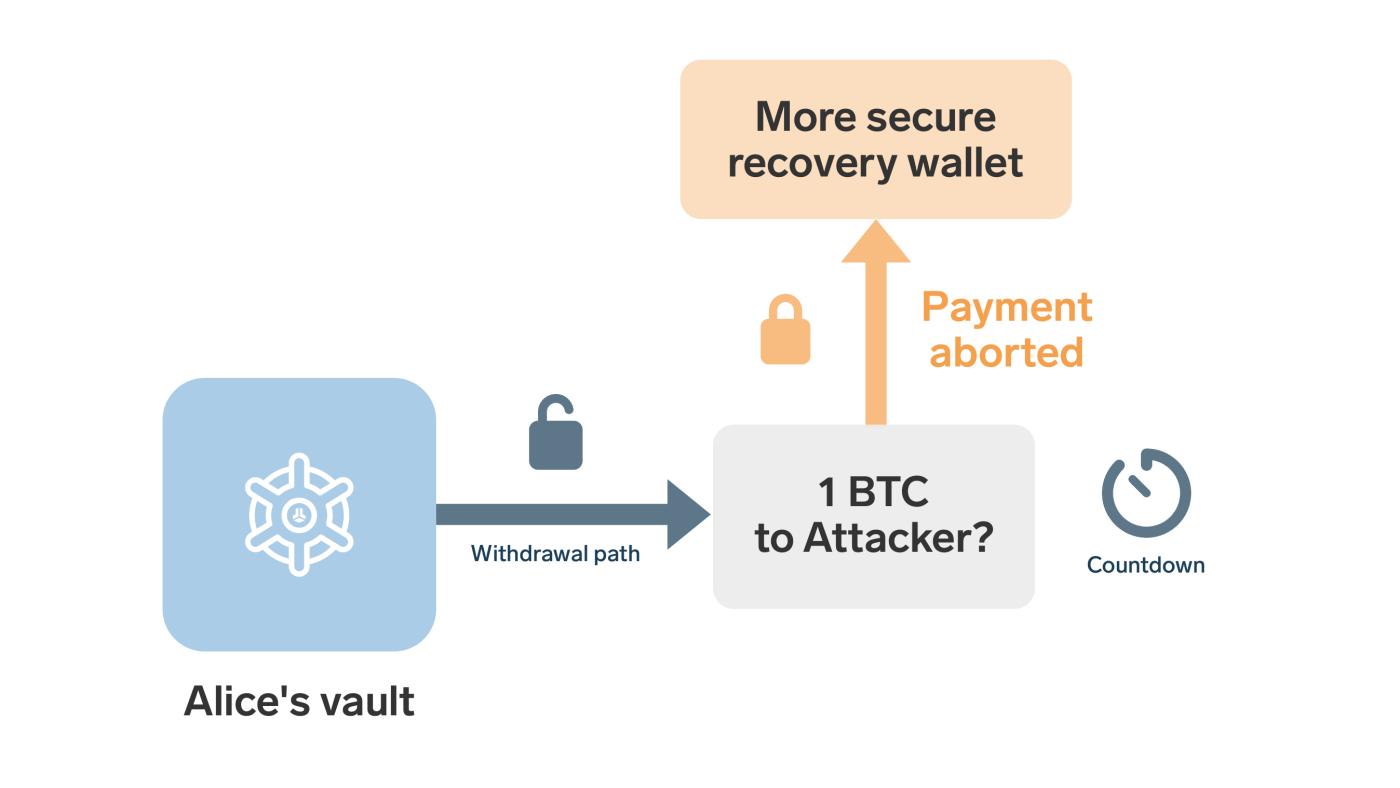
This is possible because the transaction to open the safe is subject to strict conditions ; it can only be completed by spending time on the recovery path or by being taken by the target recipient after the countdown ends.
Choice
Like almost all measures to increase wallet security, safes address the current trade-offs by adding another layer of compromise.
You get two benefits: an easy-to-use wallet for everyday spending, while still having the advanced security and redundancy of a decentralized multi-signature device.
However, this also brings three disadvantages:
- Safe-watching : After a malicious attacker opens the safe, there needs to be a waiting period. This is only helpful if the wallet's owner notices the attack and responds promptly. This issue is similar to Lightning Network users needing a "watchtower."
- Delayed payment : Obviously, legitimate payments also take longer because there is a (necessary) waiting time when using the withdrawal route.
- More transactions : Withdrawing cash from a vault requires at least two transactions, which incurs higher transaction fees (and is more likely to cause network congestion).
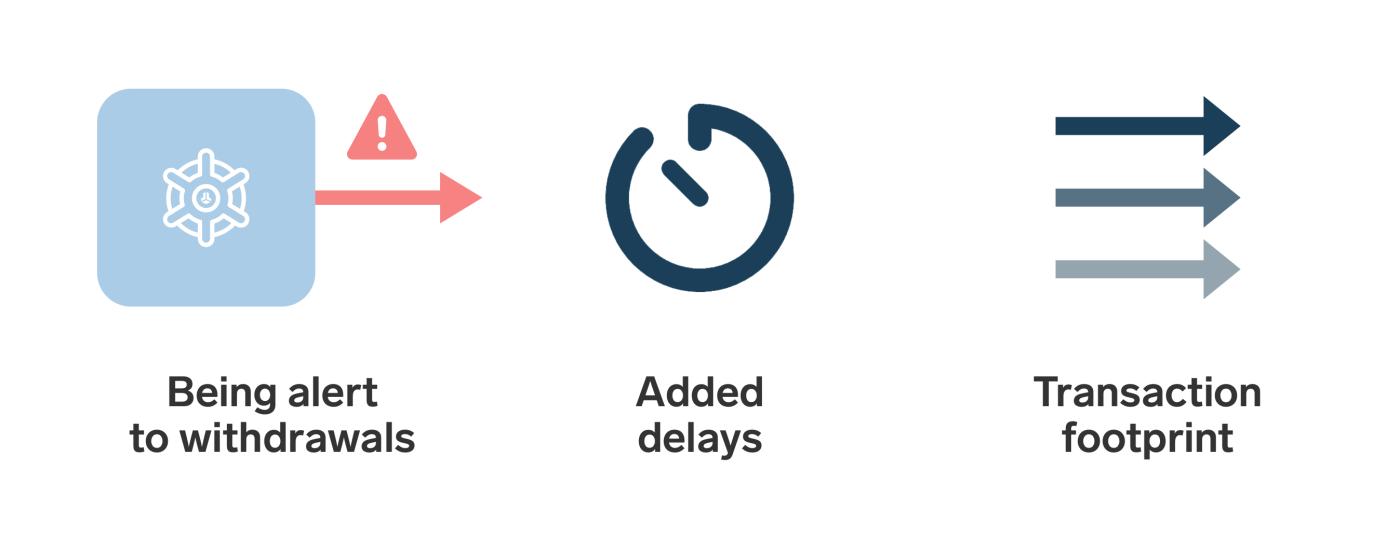
Choosing the length of the waiting period is itself a trade-off: increasing the duration makes it easier to detect and counter malicious withdrawals; but it will also further delay daily transactions—and vice versa.
Even setting aside these drawbacks, while safes have their strengths, they are not magic. Safes do not make Bitcoin "absolutely unstealable," nor do they eliminate the need for good security practices. You still need to create and manage backups, you still need to use secure hardware signers, and you still have to deal with the added technical complexity due to multi-signature and the safe itself.
This is why safes are often considered an " advanced tool " rather than a recommended solution suitable for everyone.
Suitable scenarios for safes
Safes are particularly suitable for a scenario where frequent transfers are not required, but accessibility is still desired . Examples include long-term savings, company finances, and family savings. Owners want stronger protection than a simple wallet but don't want every legitimate transaction to involve complex signature operations.
A well-designed safe can mitigate the consequences of private key hijacking because suspicious withdrawals won't succeed immediately. However, equally important, it also reduces operational burden. Users don't need to use multiple signers (or private key backups) for every routine transaction; they can spend via the withdrawal path, relying only on a more robust device in case of unforeseen circumstances. This also allows the focus of backup backup paths to shift entirely to security, as convenience is no longer a concern.
Combining these benefits also helps make estate planning easier , because your heirs won't need to use your withdrawal routes after your death (which would be tantamount to "stealing" from your safe). Adding them to a recovery route system doesn't introduce additional complexity.
The need for covenants
Bitcoin already supports useful wallet features such as multi-signature and time locks. Using tools like Miniscript , experienced users can create wallets with delayed recovery paths or inheritance-oriented clauses.
But a complete safe wallet requires more than just that. It needs to restrict not only when the money can be moved, but also where it can be moved to next. This is where " covenants " come into play.
A restriction clause is a spending condition that limits the characteristics of the next spending transaction. It is necessary for vaults because vaults need to be able to promise a very specific spending restriction, such as that money can only be withdrawn in a predefined deferred transaction, or can only be cancelled (returned to a known recovery wallet).
Without restrictive clauses, a Bitcoin safe can only rely on pre-signed transactions and careful state management. This is possible, but harder to implement well and more difficult to use. As of this writing, various restrictive clause proposals remain at the " proposal " stage. Therefore, at least for now, a native Bitcoin safe is more of an interesting concept, and its realization awaits in the future.
Conclusion
Bitcoin vaults attempt to achieve the best of both worlds, making self-custody neither too vulnerable nor too cumbersome. Instead of forcing users to rely on the strongest, most cautious security path for every everyday transaction, they incorporate separate delayed withdrawal and recovery paths behind the scenes. This transforms a theft from a potentially disastrous event into a process where the owner has time to discover and retaliate, while legitimate spending remains relatively easy.
This idea has its appeal, especially for large or infrequently moving funds. But vaults also offer important insights into broader Bitcoin security: better self-custody isn't just about better key storage; it's also about how wallets are structured, and convenience and recoverability aren't necessarily mutually exclusive.
Currently, the vast majority of users do not need safes. However, as Bitcoin wallets become more expressive, safes may eventually become the clearest example of how better Bitcoin scripting tools can improve self-custody in real-world scenarios.
(over)