Author: Zhou, ChainCatcher
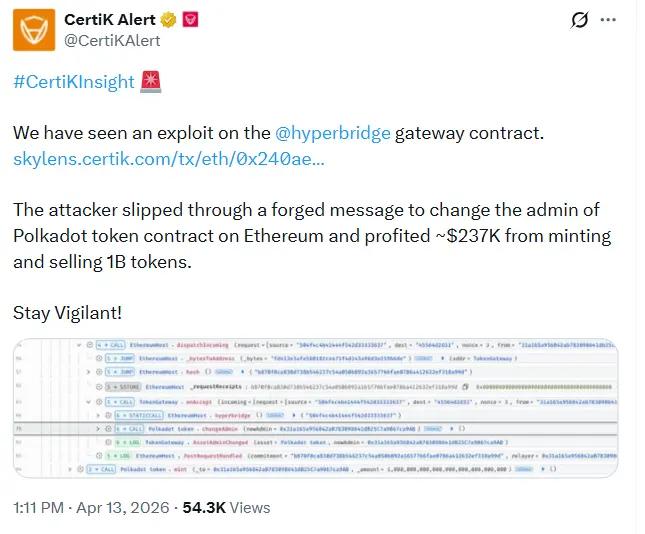
According to CertiK's analysis, the attackers submitted a carefully crafted cross-chain request to the HandlerV1 contract on the Ethereum side via Hyperbridge's ISMP protocol, and successfully bypassed the verification mechanism by using a genuine MMR proof that had been accepted by the system in the past.
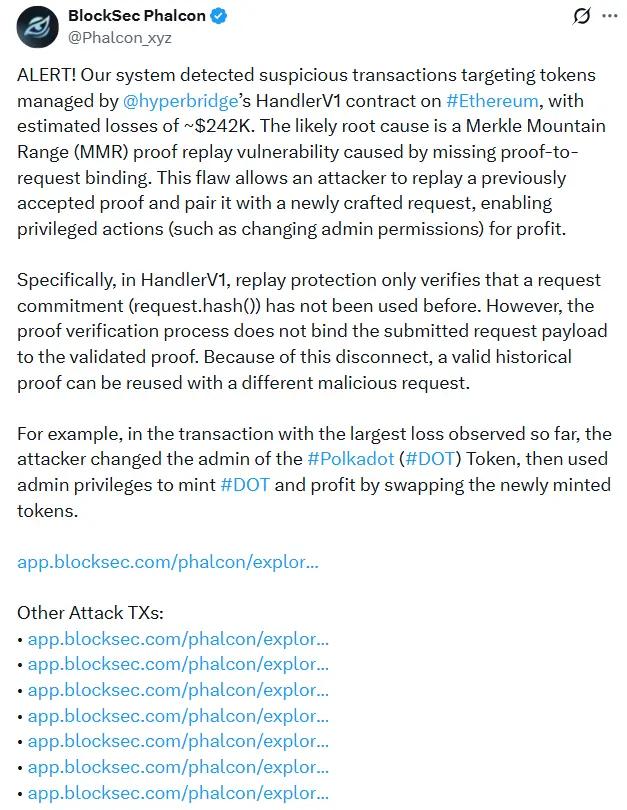
BlockSec Phalcon subsequently issued a technical alert, classifying the vulnerability as an MMR proof replay vulnerability. According to their analysis, the root cause of the vulnerability lies in the fact that the HandlerV1 contract's replay protection only verifies whether the hash value of a request has been used, but the proof verification process does not bind the submitted request payload to the proof being verified.
This logical gap allowed the attacker to replay a historical valid proof and pair it with a newly constructed malicious request. The attacker then executed the ChangeAssetAdmin operation via the TokenGateway.onAccept() path, transferring the administrator and minting permissions of the wrapped DOT contract on Ethereum (address: 0x8d...8F90b8) to an address controlled by the attacker.
According to on-chain data, after gaining the right to mint, the attackers minted 1 billion bridged DOT tokens, which is about 2,805 times the reported circulating supply of the token on Ethereum at the time, which was about 356,000.
The attacker then used Odos Router and Uniswap V4 liquidity pools to exchange all the tokens for approximately 108.2 ETH, which was then transferred to the attacker's external account. Based on the price at the time, the attacker profited approximately $237,000, while the entire attack consumed only about $0.74 in gas fees.
BlockSec Phalcon also mentioned that a previous attack using the same method targeted MANTA and CERE tokens, resulting in a loss of approximately $12,000. The total loss from the two attacks was approximately $242,000.
Following the incident, South Korea's leading exchanges Upbit and Bithumb announced the suspension of deposit and withdrawal services for DOT and AssetHub Polkadot networks to prevent potential fake deposit risks.
Polkadot officials stated that the vulnerability only affects DOT transferred to Ethereum via Hyperbridge; it does not affect DOT assets within the Polkadot ecosystem, nor does it affect DOT transferred through other cross-chain bridges. Polkadot and its parachains, as well as native DOT, remain secure and unaffected. Hyperbridge is currently suspended to allow for an investigation into the issue.
It's worth noting that despite the minting scale reaching as high as 1 billion tokens , the actual losses were far lower than the theoretical figures. Due to the extremely limited on-chain liquidity of wrapped DOT on Ethereum, the concentrated sell-off of 1 billion tokens instantly drove the price of wrapped DOT from $1.22 to $0.00012831, a drop of 99.98%, with the vast majority of tokens unable to be effectively liquidated.
According to CoinMarketCap data, the price of the native DOT token was also briefly dragged down by market sentiment, falling by nearly 5% at one point.
Users on X bluntly stated that no one could have imagined that DOT, once a cross-chain legend alongside Ethereum, would ignite social media in this way. Cross-chain bridges have once again become the "Achilles' heel" of the crypto world; what was once ignored has now become a scene of devastation and lamentation. When 1 billion DOT appeared out of thin air, all technical specifications became worthless.
Some users jokingly said that the low liquidity "saved Polkadot's life" in this unexpected event, keeping the actual loss to about $237,000.
However , while the low liquidity of bridged assets limited hackers' profits, it exposed the potential vulnerabilities of the cross-chain interoperability layer.
Hyperbridge , developed by Polytope Labs, is a cross-chain interoperability project within the Polkadot ecosystem. It has long prioritized cryptographic proofs over multi-signature committees as its core security mechanism, positioning itself as a trust-minimized cross-chain infrastructure. The project has consistently emphasized its resilience against common bridging attacks.

However, this incident may indicate that the integrity of the cryptographic proof mechanism itself is not enough to guarantee security, and the specific implementation logic of the Ethereum Gateway contract also constitutes an attack surface.
From a broader perspective, this incident is a microcosm of the increasingly severe security situation in DeFi since 2026. Several major attacks have occurred this year, including Venus incurring $2.15 million in bad debt due to price manipulation, Resolve over-minting 80 million USR, and Drift suffering a theft of over $285 million in assets. These attacks employed diverse methods and involved a wide range of sectors.
Taking over the right to mint coins and issuing unlimited amounts is not a new attack pattern. However, because Hyperbridge has extremely low liquidity, its losses were unexpectedly minimized.
According to CertiK data, 46 security incidents were recorded in March alone, with total losses of approximately $39.8 million, the highest monthly record since November 2024. CertiK also pointed out that the increased frequency of code vulnerability exploitation may be related to the rise of AI-assisted vulnerability discovery tools.
The rising frequency of attacks is also prompting the industry to re-examine the boundaries of security and regulation. Dante Disparte, Chief Strategy Officer of Circle, previously called for protocols, wallets, exchanges, and stablecoin issuers to consider security and accountability as shared obligations in response to the Drift Protocol hack. He suggested that DeFi protocols could develop on-chain technical protection measures by referencing the circuit breaker mechanisms of traditional markets, and that legislation should be pushed to incorporate property rights and financial privacy protection standards into law before the next major incident .







