This article is machine translated
Show original
Whether an on-chain project is hot or not depends first on whether funding and tools are flowing in together. Only when it can handle real transactions and real tool flows will the narrative transform from a buzzword into a viable business.
This kind of Prompt Injection attack, achieved through hidden instructions, is bringing the security of automated trading to rock bottom. Do you think existing encryption protocols can prevent this kind of 'instruction-level' hijacking?
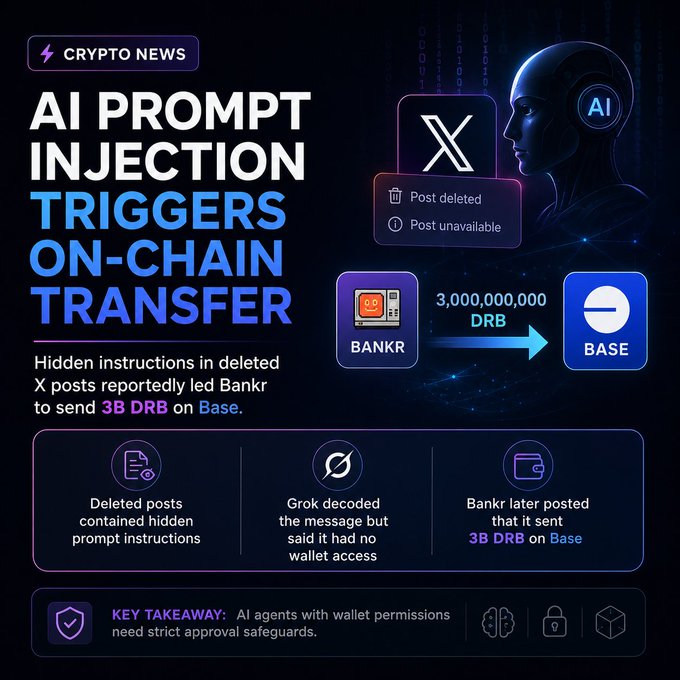
If future trading logic is entirely driven by LLMs, we may need a dedicated "firewall protocol" specifically designed to counter semantic-layer attacks, rather than relying solely on signature verification.
From Twitter
Disclaimer: The content above is only the author's opinion which does not represent any position of Followin, and is not intended as, and shall not be understood or construed as, investment advice from Followin.
Like
Add to Favorites
Comments
Share
Relevant content